Service Border
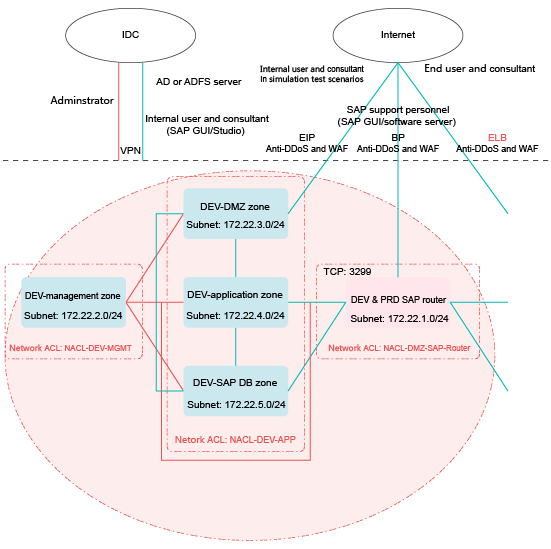
The development and test environment needs to interconnect with enterprise intranets for service development and tests and communicate with the public network. Therefore, set up VPN channels between the development and test environment and enterprise intranets (IDCs). Configure access control policies between the cloud and the on-premises system and between the cloud and the Internet.
VPN
The development and test environment is used for service development and tests in an enterprise. Therefore, static connections are usually required in the development and test environment. When security and latency are taken into consideration, the recommended priority is as follows: Direct Connect > IPsec VPN > SSL VPN.
Currently, the HUAWEI CLOUD VPN service supports only Direct Connect and IPsec VPN. If you need to use SSL VPN, you can deploy it using a third-party image.
Security Policies
The development and test environment needs to communicate with enterprise intranets and allow access from the Internet. Therefore, networks ACLs are used for access control.
As shown in Figure 1, network ACL NACL-DEV-APP is associated with the subnets for the DEV-DMZ, DEV-application, and DEV-SAP DB zones. Configure outbound rules of network ACL NACL-DEV-APP to strictly control access to enterprise intranets (IDCs), allowing access to only specified IP addresses and ports in IDCs.
Configure inbound rules of network ACL NACL-DEV-APP based on your service requirements to control access from IDCs to the development and test environment. For a fixed scenario, such as an AD server, configure access control policies to allow the AD server to communicate with specified IP addresses and ports in the cloud. For end users, configure access control policies to allow them to access a specified IP address segment and port range and management ports, such as 22 and 3389.
Network ACL NACL-DEV-APP is associated with the subnets for the DEV-DMZ, DEV-application, and DEV-SAP DB zones. Network ACL NACL-DMZ-SAP-Router is associated with the subnet for the DEV&PRD SAP router. Configure their inbound rules to strictly control access from the Internet, allowing access from the Internet to only specified IP addresses and ports in the development and test environment.
IP addresses and ports in this section are only used as examples. If the public IP address is not fixed, you can create an ACL rule to allow access from a specified public source IP address to meet your service requirements (such as technical support) and then delete the rule when it is not required. If there are other services, you can add ACL rules as required.
|
Rule |
Destination IP Address |
Protocol |
Destination Port |
Allow or Deny |
Description |
|---|---|---|---|---|---|
|
* |
0.0.0.0/0 |
Any |
Any |
Deny |
Denies all outbound traffic that is not processed using preset fixed rules. |
|
Rule |
Source IP Address |
Protocol |
Destination Port |
Allow or Deny |
Description |
|---|---|---|---|---|---|
|
For SAP technical support personnel (SAP GUI or software server) |
123.123.123.0/24 |
TCP |
3299 |
Allow |
Allows Internet SAP technical support personnel (SAP GUI or software server) from specified source IP addresses to access the DEV&PRD SAP router and then access backend services. |
|
* |
0.0.0.0/0 |
Any |
Any |
Deny |
Denies all inbound traffic that is not processed based on preset rules. |
|
Rule |
Destination IP Address |
Protocol |
Destination Port |
Allow or Deny |
Description |
|---|---|---|---|---|---|
|
For AD or ADFS servers |
IP address of an AD or ADFS network in the IDC |
TCP |
AD or ADF port |
Allow |
Allows access to AD or ADFS servers in IDCs. |
|
* |
0.0.0.0/0 |
Any |
Any |
Deny |
Denies all outbound traffic that is not processed based on preset rules. |
|
Rule |
Source IP Address |
Protocol |
Destination Port |
Allow or Deny |
Description |
|---|---|---|---|---|---|
|
For Internet users and consultants |
123.123.123.0/24 |
TCP |
80 |
Allow |
Allows Internet users and consultants from specified IP addresses to access web services in the development and test environment. |
|
For Internal users and consultants |
123.123.123.0/24 |
TCP |
443 |
Allow |
Allows Internet users and consultants from specified IP addresses to access web services in the development and test environment. |
|
For IDC users and consultants |
A subnet (subnet b) in an IDC |
TCP |
80 |
Allow |
Allows internal users and consultants in a subnet (subnet b) in an IDC to access web services in the development and test environment. |
|
For IDC users and consultants |
A subnet (subnet b) in an IDC |
TCP |
443 |
Allow |
Allows internal users and consultants in a subnet (subnet b) in an IDC to access web services in the development and test environment. |
|
* |
0.0.0.0/0 |
Any |
Any |
Deny |
Denies all inbound traffic that is not processed based on preset rules. |
For security group rule configuration, see the related content in Network Isolation and Access Control.
Security Services
- Anti-DDoS
The development and test environment needs to communicate with the public network. Therefore, it is recommended that you deploy Anti-DDoS on SAP router, SRM, and Hybrids servers. You can use HUAWEI CLOUD Anti-DDoS to protect elastic IP addresses (EIPs).
- WAF
The development and test environment needs to provide web applications for the Internet. Therefore, it is recommended that you install WAF to defend against OWASP TOP10 and other web attacks. You can use the HUAWEI CLOUD WAF service to create WAF instances to protect EIPs.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot