Overview
Scenarios
The existing network architecture of the on-premises data center needs to be migrated to the cloud without any changes.
- Servers in two overlapping CIDR blocks in the on-premises data center need to access each other.
- Servers need to access external resources with a specified IP address.
For example:
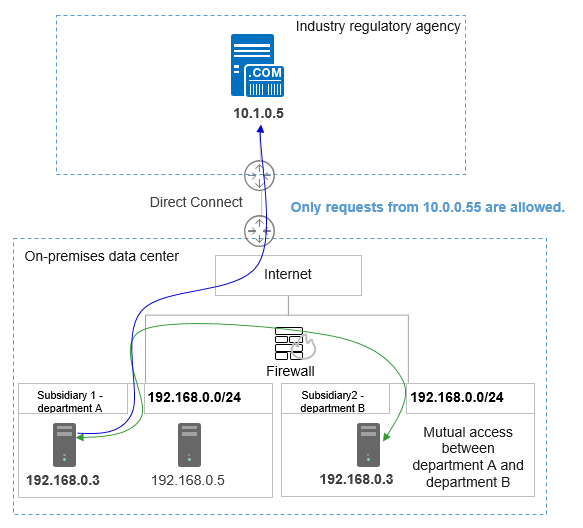
A company with multiple branches had overlapping subnets for different branch offices. In Figure 1, department A and department B are assigned the same CIDR blocks 192.168.0.0/24, and servers on the two CIDR blocks can communicate with each other. In addition, department A needs to periodically use a specified IP address to access archived data of hosts in the industry supervision agency.
Workloads in the on-premises data center were huge and complex. Re-planning and reconstructing CIDR blocks would impact existing workloads. The customer wanted to migrate the existing network to the cloud without any modifications and required that servers in the overlapping subnets could still access each other after the migration. In addition, servers in department A can still access serves in the industry supervision agency using the specified IP address.
Solution Architecture
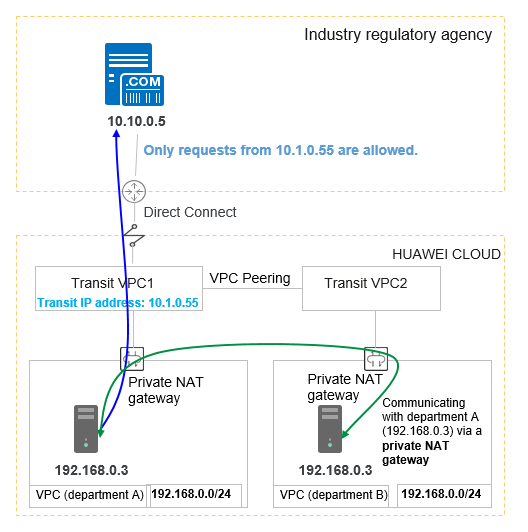
Private NAT gateways of Huawei Cloud provide network address translation (NAT) for servers in a VPC to enable mutual access between servers in overlapping subnets of VPCs and private address mapping of servers. This resolves the issue that VPC peering connections created between VPCs that have overlapping subnet CIDR blocks may not take effect.
See Figure 2.
- The CIDR block 192.168.0.0/24 of department A and that of department B were migrated to the VPC, and two private NAT gateways were used to enable mutual access between servers from the two departments.
- SNAT rules were configured to map the private IP addresses of servers in department A to 10.1.0.55 to access external servers.
Solution Advantages
- Customers can directly migrate off-cloud on-premises data center services to the cloud without reconstructing the existing network architecture, reducing network reconstruction costs.
- Servers with overlapping private IP addresses can communicate with each other.
- Servers in a private network can access external resources using a specified IP address to meet security requirements.
Constraints and Limitations
Pay attention to the following points when using a private NAT gateway:
- Manually add routes in a VPC to connect it to a remote private network through a VPC peering connection, Direct Connect, or VPN connection.
- Only one SNAT rule can be added for each VPC subnet.
- SNAT and DNAT rules cannot share a transit IP address.
- A DNAT rule with Port Type set to All ports cannot share a transit IP address with a DNAT rule with Port Type set to Specific port.
- The total number of DNAT and SNAT rules that can be added on a private NAT gateway varies with the private NAT gateway specifications.
- Small: 20 or less
- Medium: 50 or less
- Large: 200 or less
- Extra-large: 500 or less
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot