Rotating Certificates
IAM Identity Center uses certificates to set up a SAML trust relationship between IAM Identity Center and your external identity provider. When you change the identity source to an external identity provider, you must also obtain at least one SAML 2.0 certificate from the external identity provider. SP certificates are usually generated manually when signed requests are required, while IdP certificates are usually included in the SAML metadata file and are automatically installed when you upload the IdP SAML metadata during identity source change.
You may need to import certificates periodically to rotate invalid or expired certificates issued by your identity provider. This helps prevent authentication disruption or downtime. The process of replacing old certificates with new ones is called certificate rotation. Certificates can be deleted only after you ensure that they are no longer in use by the associated identity provider.
You should also consider that some identity providers may not support multiple certificates. In this case, rotating a certificate may temporarily interrupt services for your users. After the certificate is rotated and the trust with the identity provider is re-established, services will be restored. You are advised to rotate certificates during off-peak hours.
- If an existing SAML certificate is disclosed or handled improperly, you should immediately replace it and delete the old one.
- Each SP supports a maximum of two certificates, but only one certificate can be activated.
- The default validity period of an SP certificate is 10 years.
- All imported certificates are automatically activated. Currently, a maximum of two certificates are supported.
Rotating SP Certificates
- Manually generate a certificate.
- Log in to the Huawei Cloud management console.
- Click
 in the upper left corner of the page and choose Management & Governance > IAM Identity Center.
in the upper left corner of the page and choose Management & Governance > IAM Identity Center. - Choose Settings in the navigation pane.
- On the Identity Source tab, click Modify SAML 2.0 Configuration in the Authentication Method row.
- On the displayed page, click Generate Certificate.
- Locate the certificate and click Activate in the Operation column. The old certificate status automatically changes to inactive.
- Delete the old certificate.
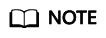
- On the Manage SAML 2.0 Authentication page, select the certificate to be deleted from the SP certificate list and click Delete.
- In the displayed dialog box, enter DELETE and click OK.
Figure 1 Deleting a certificate
Rotating IdP Certificates
- Obtain a new certificate from your identity provider.
Go to the identity provider website and download the SAML 2.0 certificate. Make sure that the certificate file is downloaded in PEM encoding format. Most identity providers allow you to create multiple SAML 2.0 certificates, which are likely to be marked as disabled or inactive.
- Import the new certificate to IAM Identity Center.
- Log in to the Huawei Cloud management console.
- Click
 in the upper left corner of the page and choose Management & Governance > IAM Identity Center.
in the upper left corner of the page and choose Management & Governance > IAM Identity Center. - Choose Settings in the navigation pane.
- On the Identity Source tab, click Modify SAML 2.0 Configuration in the Authentication Method row.
- On the displayed page, click Import.
- In the displayed dialog box, click Select File, select the obtained new certificate, and click Import Certificate.
Figure 2 Importing a certificate

Then IAM Identity Center will trust all incoming SAML messages signed from both of the certificates that you have imported.
- Activate the new certificate in the external identity provider.
Return to the identity provider website and mark the new certificate that you created earlier as primary or active. All SAML messages signed by the identity provider should be using the new certificate.
- Delete the old certificate.
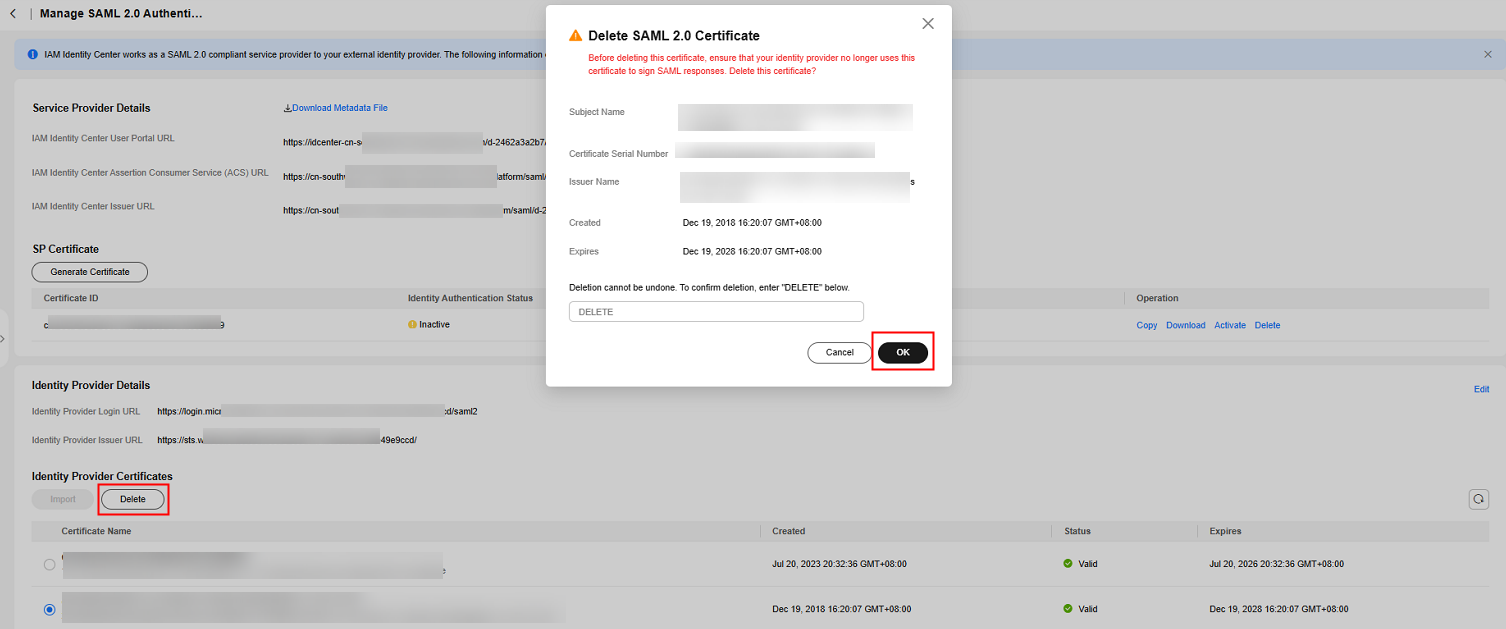
- Before deleting this certificate, ensure that your identity provider no longer uses this certificate to sign SAML responses.
- There must always be at least one valid certificate in the certificate list.
- On the Manage SAML 2.0 Authentication page, select the certificates to be deleted in the IdP certificate list and click Delete.
- In the displayed dialog box, enter DELETE and click OK.
Figure 3 Deleting a certificate
- Return to the identity provider website and delete the old certificate.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





