Adding a Target Host to a Host Cluster
To better meet actual service requirements, maintain system stability, and enhance deployment efficiency, it is necessary to add one or more target hosts to the host cluster.
This section describes how to add a target host to a host cluster.
Prerequisites
- A host cluster is available. You have the permission to add hosts to the cluster.
- A host bound to a public IP address is available and meets the following conditions. (If you do not have a host, purchase one by referring to Purchasing an ECS in Custom Config Mode.)
- The system host has been configured. For details, see Configuring a Linux Host or Configuring the Host Running Windows.
(This configuration has been completed for Huawei Cloud ECSs (Linux) by default. You do not need to configure it again. However, you need to configure it for Windows system hosts.)
- If you need to monitor a host, you need to create an agency for the host. For details, see Creating an Agency for a Host.
- The system host has been configured. For details, see Configuring a Linux Host or Configuring the Host Running Windows.
Adding a Target Host
- Go to the CodeArts homepage.
- Log in to the CodeArts console, click
 , and select a region where you have enabled CodeArts.
, and select a region where you have enabled CodeArts. - Click Go to Workspace.
If your account uses the old billing mode (see Old Billing Modes), click Access Service.
- Log in to the CodeArts console, click
- Click the target project name to go to the project.
- Choose CICD > Deploy.
- On the Basic Resources tab page, click the name of the created cluster to go to the Target Hosts page.
- Click Add Host and select Adding IP for Add Hosts by.
- Select Direct Connection for Host Connection Mode and add a target host. Enter the following information and click OK.
Table 1 Parameters of the target host (Linux) Parameter
Description
Host Name
Enter a custom target host name.
Enter 3 to 128 characters. Use digits, letters, hyphens (-), underscores (_), and periods (.).
IP
Enter the public IP address bound to the target host. IPv4 or IPv6 address is supported.
OS
The default value is the OS of the current host cluster and cannot be changed.
Configure the target host by referring to Configuring a Linux Host to ensure the successful connectivity verification.
Authorization
Select Password or Key for authentication as required.
- If you select Password, the Username and Password are displayed. Take ECS as an example. Enter the ECS username and password.
- If you select Key, the Username and Key are displayed. For details about how to generate and obtain a key, see Obtaining the Linux key.
SSH Port
Port 22 is recommended. You may customize the port.
Table 2 Parameters of the target host (Windows) Parameter
Description
Host Name
Enter a custom target host name.
Enter 3 to 128 characters. Use digits, letters, hyphens (-), underscores (_), and periods (.).
IP
Enter the public IP address bound to the target host. IPv4 or IPv6 address is supported.
OS
The default value is the OS of the current host cluster and cannot be changed.
Configure the target host by referring to Configuring the Host Running Windows to ensure the successful connectivity verification.
Authorization
Windows target hosts support only password authentication. Take ECS as an example. Enter the ECS username and password.
Winrm Port
Port 5986 is recommended. You may customize the port.
- Select Agent for Host Connection Mode and add an agent host and a target host. Enter the following information and click OK.
- Add an agent host.
Table 3 Parameters of the agent host (Linux) Parameter
Description
Host Name
Enter a custom agent host name.
Enter 3 to 128 characters. Use digits, letters, hyphens (-), underscores (_), and periods (.).
IP
Enter the public IP address bound to the agent host. IPv4 or IPv6 address is supported.
OS
The default value is the OS of the current host cluster and cannot be changed.
Configure the agent host by referring to Configuring a Linux Host to ensure the successful connectivity verification.
Authorization
Select Password or Key for authentication as required.
- If you select Password, the Username and Password are displayed. Take ECS as an example. Enter the ECS username and password.
- If you select Key, the Username and Key are displayed. For details about how to generate and obtain a key, see Obtaining the Linux key.
SSH Port
Port 22 is recommended. You may customize the port.
Table 4 Parameters of the agent host (Windows) Parameter
Description
Host Name
Enter a custom agent host name.
Enter 3 to 128 characters. Use digits, letters, hyphens (-), underscores (_), and periods (.).
IP
Enter the public IP address bound to the agent host. IPv4 or IPv6 address is supported.
OS
The default value is the OS of the current host cluster and cannot be changed.
Configure the target host by referring to Configuring the Host Running Windows to ensure the successful connectivity verification.
Authorization
Windows proxies support only password authentication. Take ECS as an example. Enter the ECS username and password.
Winrm Port
Port 5986 is recommended. You may customize the port.
- Add a target host.
Table 5 Parameters of the target host (Linux) Parameter
Description
Host Name
Enter a custom target host name.
Enter 3 to 128 characters. Use digits, letters, hyphens (-), underscores (_), and periods (.).
Agent Host
Select the target agent host as the network agent of the target host that cannot connect to the public network.
IP
Enter the IP address of the target host. IPv4 or IPv6 address is supported.
OS
The default value is the OS of the current host cluster and cannot be changed.
Configure the target host by referring to Configuring a Linux Host to ensure the successful connectivity verification.
Authorization
Select Password or Key for authentication as required.
- If you select Password, the Username and Password are displayed. Take ECS as an example. Enter the ECS username and password.
- If you select Key, the Username and Key are displayed. For details about how to generate and obtain a key, see Obtaining the Linux key.
SSH Port
Port 22 is recommended. You may customize the port.
Table 6 Parameters of the target host (Windows) Parameter
Description
Host Name
Enter a custom target host name.
Enter 3 to 128 characters. Use digits, letters, hyphens (-), underscores (_), and periods (.).
Agent Host
Select the target agent host as the network agent of the target host that cannot connect to the public network.
IP
Enter the IP address of the target host. IPv4 or IPv6 address is supported.
OS
The default value is the OS of the current host cluster and cannot be changed.
Windows: Configure the target host by referring to Configuring the Host Running Windows to ensure the successful connectivity verification.
Authorization
Windows target hosts support only password authentication. Take ECS as an example. Enter the ECS username and password.
Agent Forwarding Port
Set this port to the listening port specified during Configuring a Windows Agent. Port 54 is recommended. You can also use a custom port.
- Add an agent host.
- Select Importing ECS.To add your Huawei Cloud ECS as the target host or agent host, click Add Host, and select Importing ECS for Add Hosts by.

Before importing a purchased ECS, confirm that these conditions are met:
- ECS is running.
- ECS and the host cluster have the same OS.
- When using an official agent pool, the agent host must have a public IP address.
- ECS has been imported as the target host. It cannot be imported as an agent host.
- In the agent mode, configure the agent host before using the target host.
- Importing an ECS (host)
Click Import in the row where the ECS is located. On the displayed page, set the parameters for the Linux and Windows hosts by referring to step 6 and step 7.
- Importing ECSs (hosts) in batches
Select the ECSs to be imported and click Import Selected in the lower part. On the displayed page, set the parameters for the Linux and Windows hosts by referring to step 6 and step 7.
After the configuration, click
 next to the parameter to fill down it to the hosts listed underneath.
next to the parameter to fill down it to the hosts listed underneath.
- Verify the host connectivity.
After the host is added, the system automatically verifies the connectivity. If the connectivity verification fails, click Failed and rectify the fault based on the failure cause displayed in the dialog box or click View Solution.
For details about connectivity verification, see Host Management.
Configuring Target Hosts of Different Systems
CodeArts Deploy supports adding Linux and Windows target hosts. The following sections describe how to configure them.
To ensure that the connectivity verification of the Linux host is successful, ensure that Python is installed on the Linux host and the SELinux mechanism is enabled. The target host must meet the following requirements:
- Install Python: Install Python 2.6 or later. If Python earlier than 2.6 has been installed, run the following commands to install the following modules on the host:
- Ubuntu
sudo apt install python-minimal python-simplejson
- CentOS or EulerOS
sudo yum install python-minimal python-simplejson ln -s /usr/bin/python2 /usr/bin/python
Before using Advanced Packaging Tool (APT) or Yellowdog Updater Modified (yum), ensure that an available source has been configured.
- Ubuntu
- Enable SELinux and install libselinux-python:
- Run the following command to check the SELinux status:
/usr/sbin/sestatus
Mode corresponding to the value of SELinux:
SELinux=disabled: disabled.
SELinux=enforcing: forcible mode, indicating that any behavior that violates the security policy is prohibited.
SELinux=permissive: permissive mode, indicating that any behavior that violates security policies is not prohibited but are recorded in logs.
- If SELinux is set to disabled, SELinux is disabled on the host. In this case, perform the following steps to change the SELinux status.
- Run the following command to edit the config file of the SELinux:
vi /etc/selinux/config
- Modify the SELinux parameters as required.
SELinux=enforcing: forcible mode, indicating that any behavior that violates the security policy is prohibited.
SELinux=permissive: permissive mode, indicating that any behavior that violates security policies is not prohibited but are recorded in logs.
- After the modification, press Esc to exit. Run the following command to save the file and exit.
wq
- Create the hidden file .autorelabel in the root directory, run the following command, and restart the Linux host.
touch /.autorelabel
- Run the following command to edit the config file of the SELinux:
- Run the following commands to install libselinux-python:
- Ubuntu
sudo apt install libselinux-python
- CentOS or EulerOS
sudo yum install libselinux-python
- Ubuntu
- Run the following command to check the SELinux status:
To configure a host running Windows 10, Windows Server 2016 or Windows Server 2019 as a target host, see the configuration method of Windows Server 2012. For details about how to obtain the script, see Windows2016ConfigureRemotingForAnsible.zip.
For details about automatic configuration of a target host running Windows 7, see the configuration method of Windows 2012 and obtain the script.
To use an automatic configuration script to add a host running Windows Server 2012 as an authorized host, perform the following steps:
- Before configuring the script, check whether you have completed security settings by referring to Configuring a Security Group.
- Obtain the automatic configuration script.
- Download Windows2012ConfigureRemotingForAnsible.zip.
- Decompress Windows2012ConfigureRemotingForAnsible.zip to obtain script Windows2012ConfigureRemotingForAnsible.ps1.
- Configure the host.
Log in to the host, open PowerShell, access the directory where script Windows2012ConfigureRemotingForAnsible.ps1 is stored, and run the following command:
.\Windows2012ConfigureRemotingForAnsible.ps1
The output is as follows.

The system may display a message indicating that the file cannot be loaded and a digital signature is required.
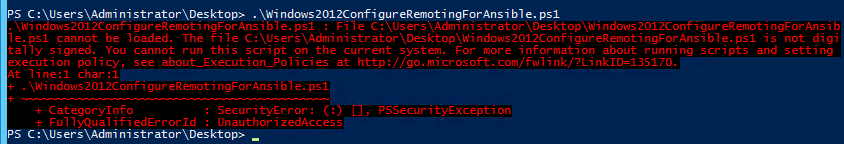
This error occurs because the script cannot be executed in default mode of PowerShell. If this happens, run the following command in PowerShell to change the execution policy to unrestricted:
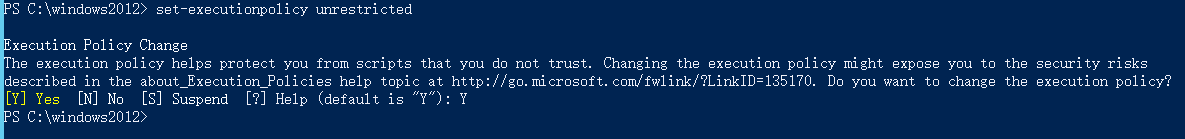
set-executionpolicy unrestricted
Enter Y to confirm the change.
- View the configuration.
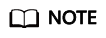
Run the following command in PowerShell:
winrm e winrm/config/listener
- If the output contains HTTPS and Hostname is not left blank, the listening is successful. The Windows Server 2012 deployment environment is automatically configured.
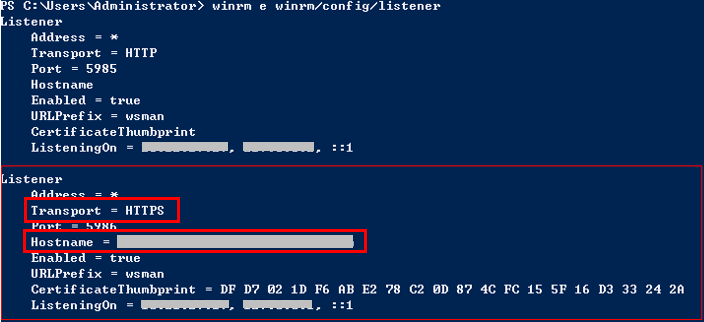
- If Hostname is left blank in the command output, the host does not have IIS or signature certificate information. In this case, run the following script:
# Configure WinRM. winrm enumerate winrm/config/listener winrm quickconfig winrm set winrm/config/service/auth '@{Basic="true"}' winrm set winrm/config/service/auth '@{CredSSP="true"}' winrm set winrm/config/service '@{AllowUnencrypted="true"}' # Install IIS. Import-Module servermanager Add-windowsfeature Web-Server,Web-WebServer,Web-Common-Http,Web-Static-Content,Web-Default-Doc,Web-Dir-Browsing,Web-Http-Errors,Web-App-Dev,Web-ASP,Web-ISAPI-Ext,Web-Health,Web-Http-Logging,Web-Log-Libraries,Web-Request-Monitor,Web-Security,Web-Filtering,Web-Stat-Compression,Web-Mgmt-Tools # Create a self-signed certificate. New-SelfSignedCertificate -CertStoreLocation Cert:\LocalMachine\My\ -DnsName 'windows-deploy-connect' # Check the self-signed certificate. ls Cert:\LocalMachine\My # Add a secure connection using the created self-signed certificate. $windows_test_key=(Get-ChildItem -Path Cert:\LocalMachine\My | Where-Object {$_.Subject -match "windows-deploy-connect"}).Thumbprint cmd /c "winrm set winrm/config/Listener?Address=*+Transport=HTTPS @{Enabled=`"true`";Port=`"5986`";Hostname=`"windows-deploy-connect`";CertificateThumbprint=`"$windows_test_key`"}"
- If the output contains HTTPS and Hostname is not left blank, the listening is successful. The Windows Server 2012 deployment environment is automatically configured.
To manually add a host running Windows Server 2012 as an authorized host, perform the following steps:
- Change the PowerShell execution policy to unrestricted.
Open PowerShell as an administrator and run the following command:
set-executionpolicy unrestricted
The output is as follows.
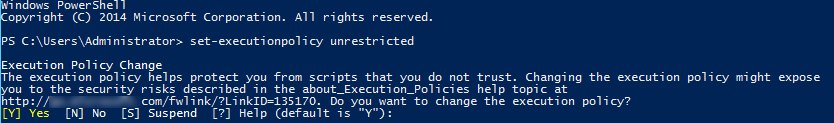
Enter Y to confirm the change.
- Configure Windows remote management (WinRM).
- Run the following commands in PowerShell:
winrm enumerate winrm/config/listener winrm quickconfig winrm set winrm/config/service/auth '@{Basic="true"}' winrm set winrm/config/service/auth '@{CredSSP="true"}' winrm set winrm/config/service '@{AllowUnencrypted="true"}' - Run the following command to check whether the configuration is successful:
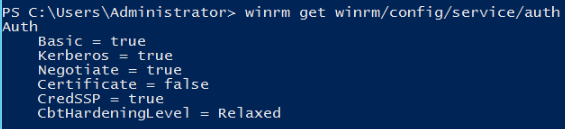
winrm get winrm/config/service/auth
If the values of Basic, Kerberos, and CredSSP are all true, the configuration is successful.
- Run the following commands in PowerShell:
- Install the certificate.
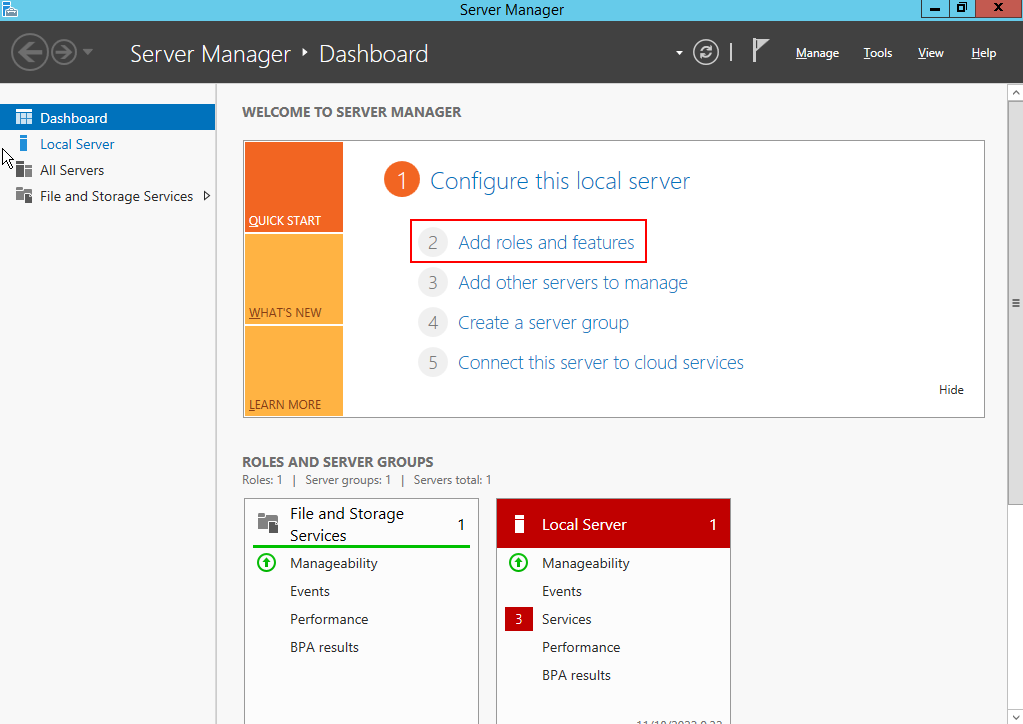
- Open Server Manager, and start IIS.
- Click , as shown in the following figure.
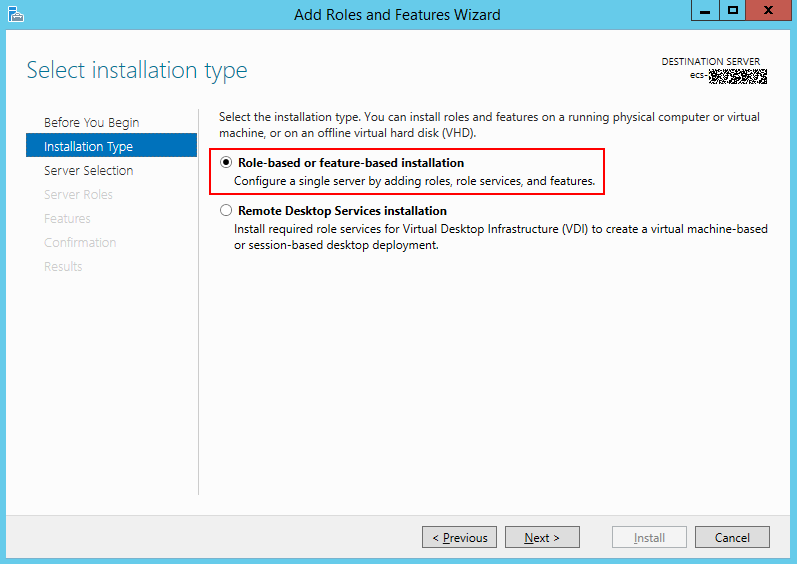
- On the Installation Type page, select the first option and click Next.
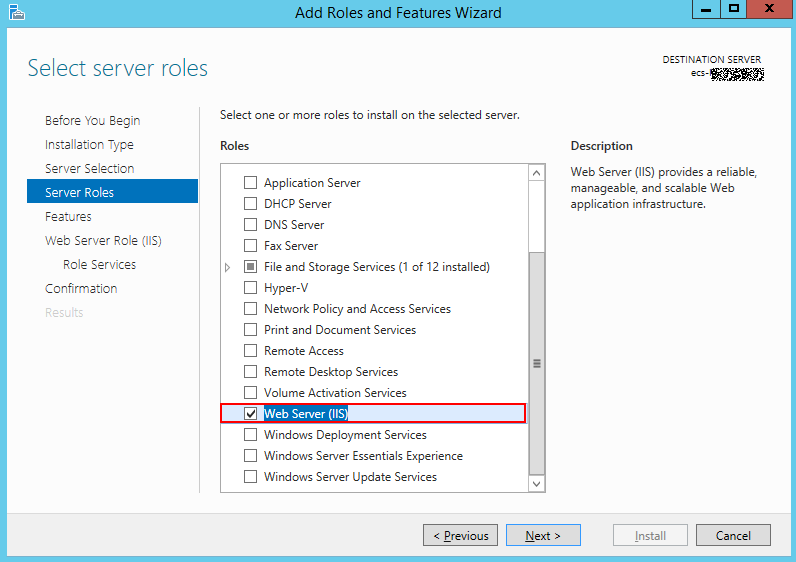
- Go to the Server Roles page and select Web Server (IIS).
- Go to the Features page, select .NET Framework 4.5, and click .
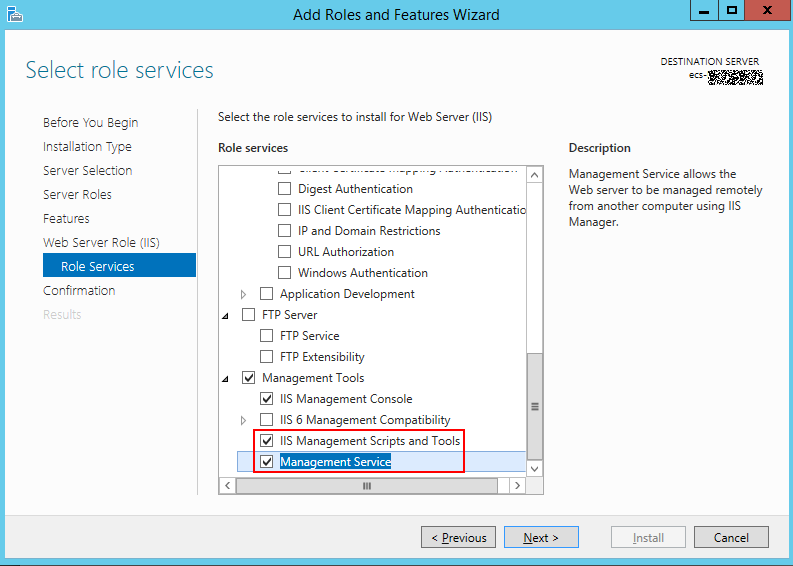
- Go to the Role Services page, select IIS Management Scripts and Tools and Management Service, and click to complete the installation.
- Add a certificate.
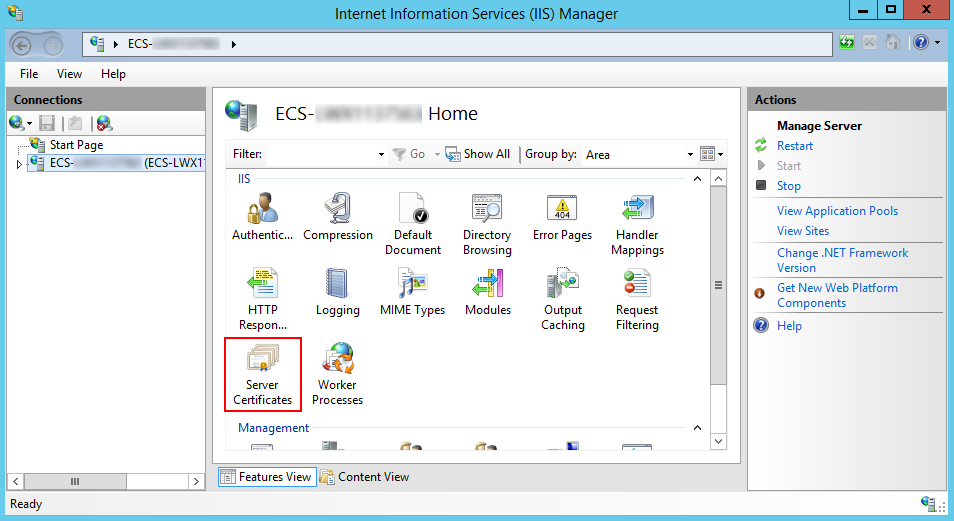
- Press Windows+R to open the Run dialog box, enter the inetmgr command for opening the IIS management window, and click OK.
- Open IIS Manager, and double-click Server Certificates.
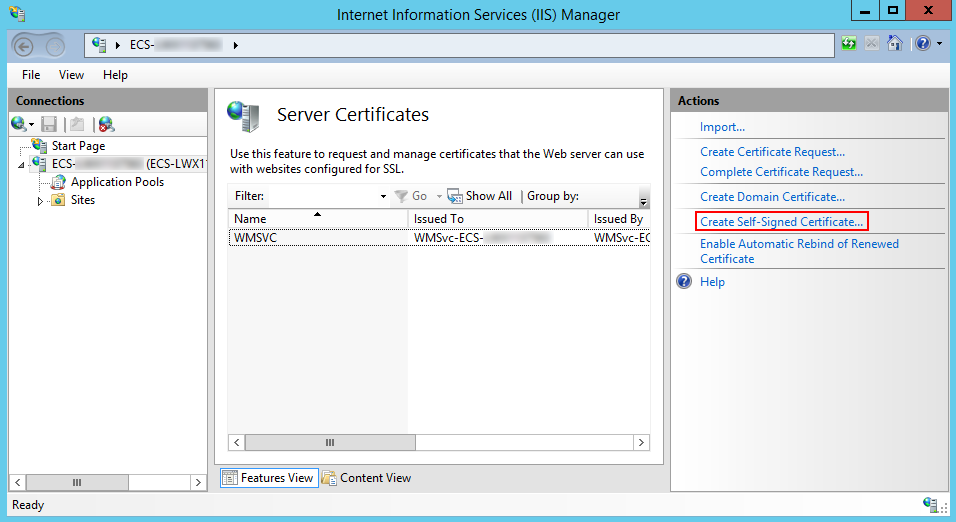
- On the Server Certificates page, click Create Self-Signed Certificate.
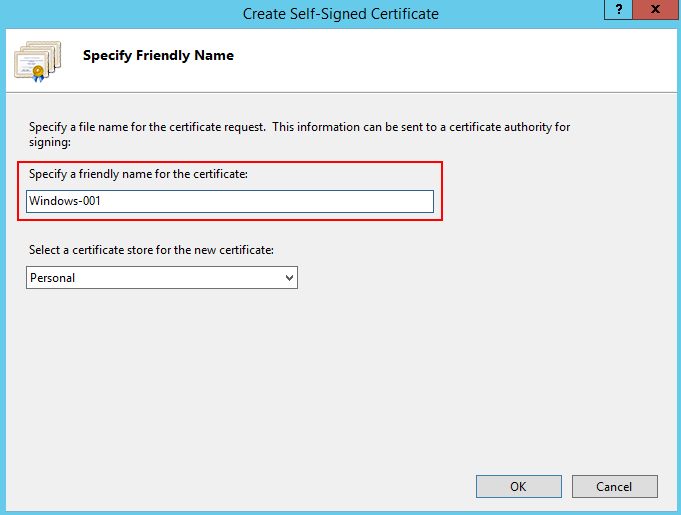
- In the Specify Friendly Name dialog box, enter the certificate name and click OK.
- Run the following command to view the certificate in PowerShell:
ls Cert:\LocalMachine\My
If the following two columns of data are displayed, the certificate is added.
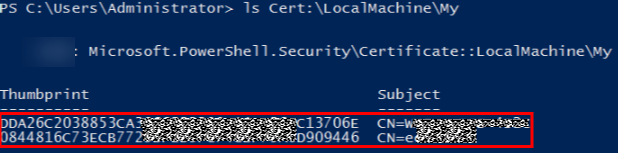
- Use the certificate to listen to the HTTPS port and configure a secure connection.
The commands are in the following format:
winrm create winrm/config/Listener?Address=*+Transport=HTTPS @{Port="User-defined port; default: 5986";Hostname="Certificate domain name";CertificateThumbprint="Certificate key value"}
- Hostname is the value in the Subject column in the preceding step.
- CertificateThumbprint is the value behind "CN=" next to the Thumbprint column in the preceding step. Every two characters are separated by a space.
Enter the following commands in the command prompt, as shown in the following figure.
winrm create winrm/config/Listener?Address=*+Transport=HTTPS @{Port="5986";Hostname="XXXXXXXXXXXXXXXX";CertificateThumbprint="DF D7 02 1D F6 AB E2 78 C2 0D 87 4C FC 15 5F 16 D3 33 24 2A"}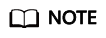
Run the command in the command prompt and separate every two characters in the value of Thumbprint with a space. Otherwise, the connectivity verification may fail. If the characters are not separated by spaces, delete the signatures and add them again.
If the system displays a message indicating that the service cannot create the resource because it already exists, run the following command to delete the resource and perform this step again:
winrm delete winrm/config/Listener?Address=*+Transport=HTTPS
- Run the following command to check whether the listening is successful in PowerShell:
winrm e winrm/config/listener
If the output contains HTTPS, the listening is successful.
- Before verifying the connectivity, check whether you have completed security settings by referring to Configuring a Security Group.
Obtaining the Linux Key
- Check whether the key exists on the host.
Log in to the host and run the following command to switch to user root:
sudo su root
Run the following command to view the key file:
ls ~/.ssh
- If a message is displayed indicating that the directory does not exist or the ~/.ssh directory does not contain the id_rsa file, generate a key.
- If the id_rsa file exists in the ~/.ssh directory, use the existing key file or generate a new one.
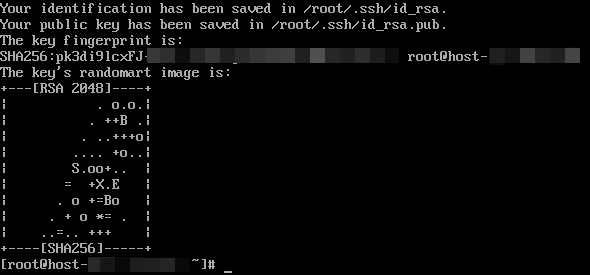
- Generate a key.Perform the following steps:
- Generate a key.
ssh-keygen -t rsa
- When the following information is displayed, press Enter.

- When the following information is displayed, press Enter. By default, no password is set. (Setting the password will fail the key verification of CodeArts Deploy.)

- When the following information is displayed, press Enter.
- If the following information is displayed, the key has been generated.
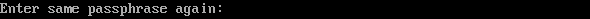
- Run the following command to check the key file generated in the .ssh directory. The id_rsa and id_rsa.pub files store the generated private key and public key, respectively.
ls ~/.ssh
- Generate a key.
- Check the information about the generated key.Run the following command:
cat ~/.ssh/id_rsa
- If the key prefix is -----BEGIN RSA PRIVATE KEY-----, the key is correct. Copy the key and save it to the local PC. Enter the key when adding a host or agent.
- If the key prefix is -----BEGIN OPENSSH PRIVATE KEY-----, the key is incorrect. Run the following command to generate a new key:
ssh-keygen -m PEM -t rsa
- Authorize the key.
Run the following command to add the public key to the authorized_keys file of the host:
cat ~/.ssh/id_rsa.pub >> ~/.ssh/authorized_keys
- To perform operations on the authorized_keys file, you must have permission to operate the id_rsa and id_rsa.pub files.
- When the key is used for connectivity verification, the username must be the name of the user who operates the authorized_keys file.
- Do not copy unnecessary spaces when manually copying the key. Otherwise, the connectivity verification may fail.
Creating an Agency for a Host
- Log in to the Huawei Cloud console.
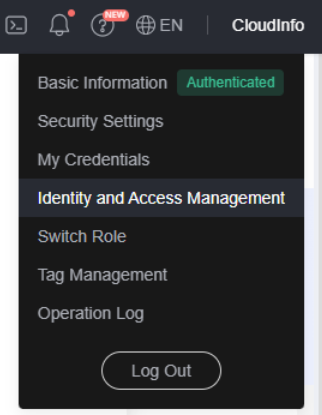
- Hover over the username in the upper right corner, as shown in the following figure, and click Identity and Access Management.
- Click Agencies in the navigation pane on the left. The Agencies page is displayed.
- Click Create Agency in the upper right corner. The Create Agency page is displayed.
- Set the parameters for creating an agency by referring to Table 7.
Table 7 Agency parameters Name
Description
Example
Agency Name
Mandatory. Name of the agency.
aom_ecm_trust
Agency Type
Select Cloud service.
-
Cloud Service
Select Elastic Cloud Server (ECS) and Bare Metal Server (BMS) from the drop-down list.
-
Validity Period
Select Unlimited.
-
Description
Optional. Provide supplementary information about the agency.
-
- Click OK. The Authorize Agency page is displayed.
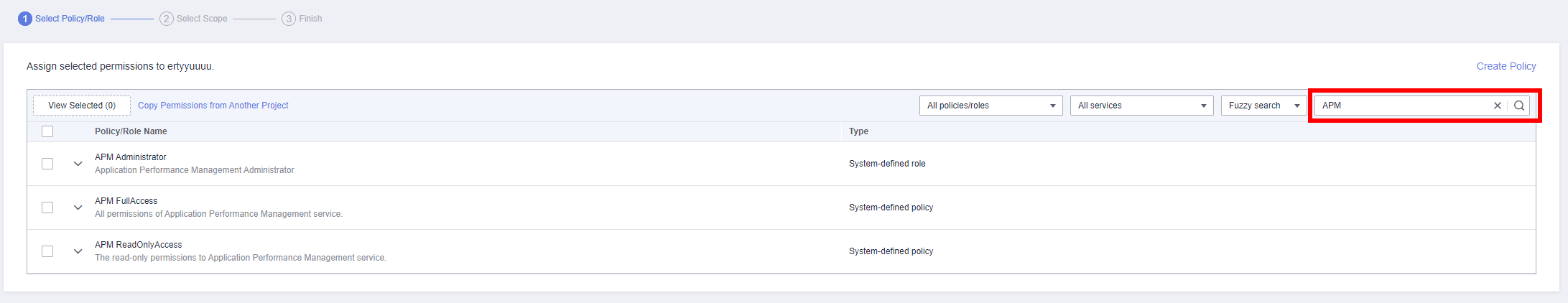
- Enter APM in the search box in the upper right corner and select APM Administrator in the search result.
- Click OK. The agency is successfully created.
Selecting an Agency
- In the navigation pane, choose Services List > Elastic Cloud Server.
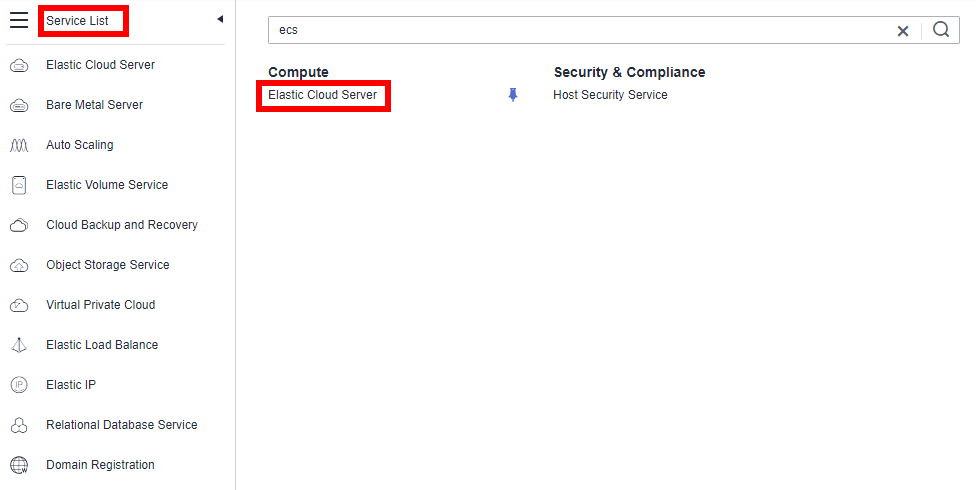
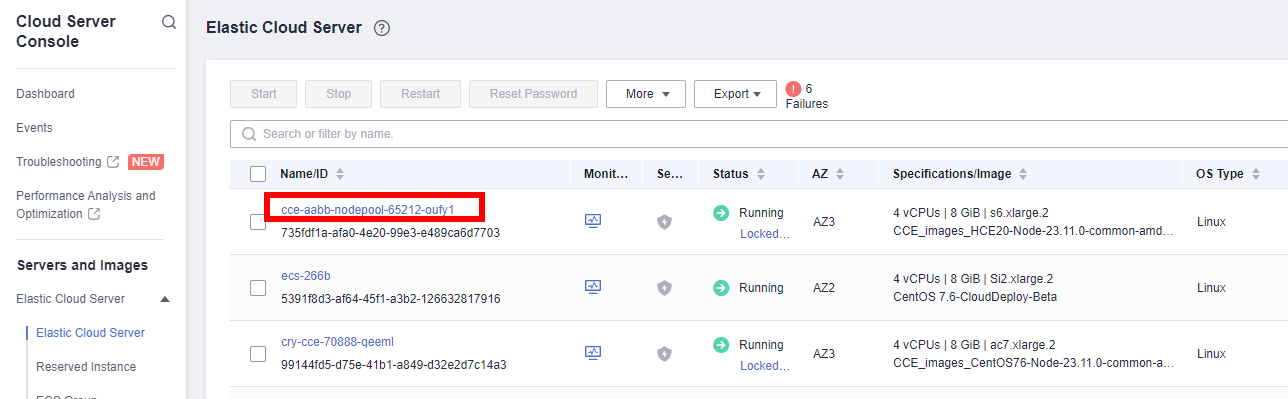
- Click the name of the ECS for which AOM monitoring is to be enabled. The ECS parameter configuration page is displayed, as shown in the following figure. By default, the search box searches for and filters data by name.
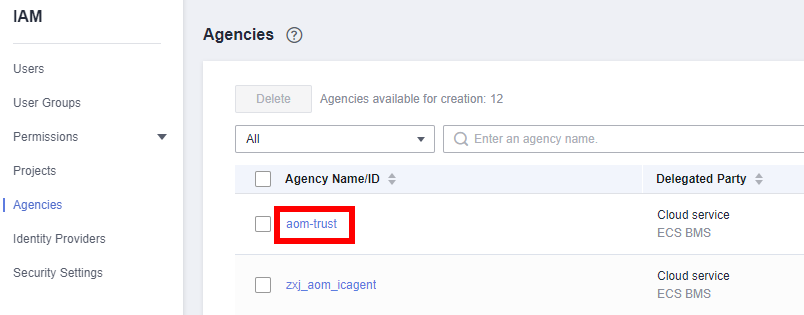
- Click the ID of the agency to be delegated, as shown in the following figure.
- Click
 . The configuration takes effect after confirmation, as shown in the following figure.
. The configuration takes effect after confirmation, as shown in the following figure.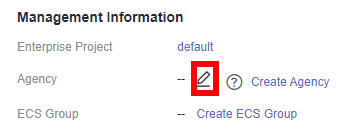
Helpful Links
- For details about APIs related to host clusters, see Managing Hosts.
- For details about connectivity verification, see Host Management.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot