Why Was I Prompted to Grant Security Administrator Permissions When I Create a Rule or Set Resource File Storage?
This is because the Identity and Access Management (IAM) user that you are using is not granted with the required management permissions. Use the administrator account to perform one of the following methods to grant permissions to the IAM user.
Method 1 (recommended): Create a custom policy (that allows agency creation, role query, and more) and attach it to the user group to which the IAM user belongs.
- Log in to the IAM console, choose Permissions > Policies/Roles in the navigation pane, and click Create Custom Policy in the upper right corner.

- Policy Name: Enter a policy name.
- Policy View: Select JSON.
- Policy Content: Set this parameter as follows:
{ "Version": "1.1", "Statement": [ { "Action": [ "iam:agencies:createAgency", "iam:agencies:listAgencies", "iam:agencies:getAgency", "iam:permissions:listRolesForAgencyOnDomain", "iam:permissions:listRolesForAgencyOnProject", "iam:permissions:grantRoleToAgencyOnProject", "iam:permissions:revokeRoleFromAgencyOnProject", "iam:permissions:grantRoleToAgencyOnDomain", "iam:permissions:revokeRoleFromAgencyOnDomain", "iam:permissions:checkRoleForAgencyOnProject", "iam:permissions:checkRoleForAgencyOnDomain", "iam:roles:createRole", "iam:roles:listRoles", "iam:roles:getRole" ], "Effect": "Allow" } ] }
- Click OK. The custom policy is created.
- Choose User Groups in the navigation pane and click the target user group.
- Click the Permissions tab and click Authorize.

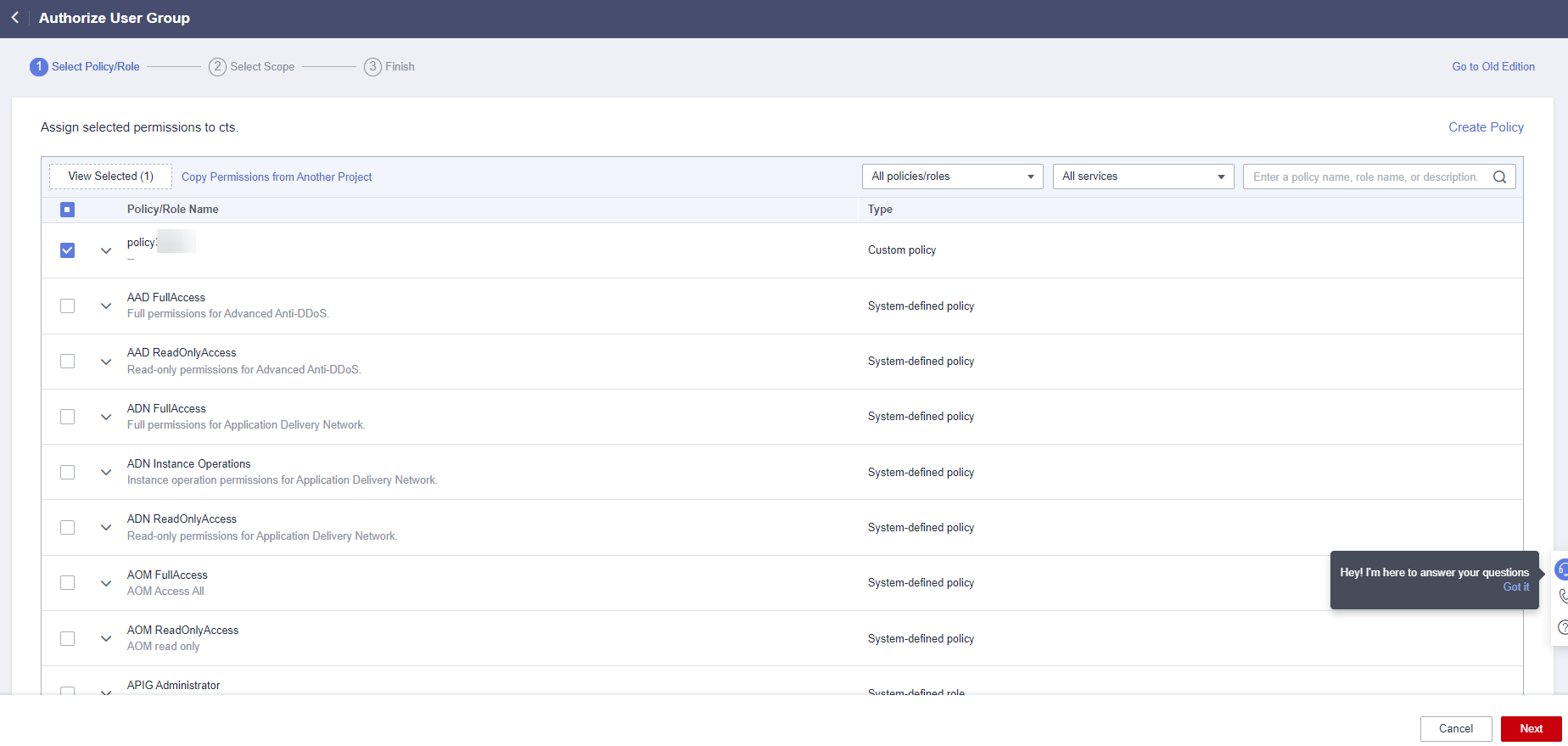
- On the Select Policy/Role page, select the policy created in 1, and click Next.
- On the Select Scope page, select All Resources, and click OK.
Method 2: Grant the Security Administrator permissions to the user group to which the IAM user belongs.
- Log in to the IAM console, choose User Groups in the navigation pane, and click the target user group.
- Click the Permissions tab, search for Security Administrator, select Security Administrator, and click Next.
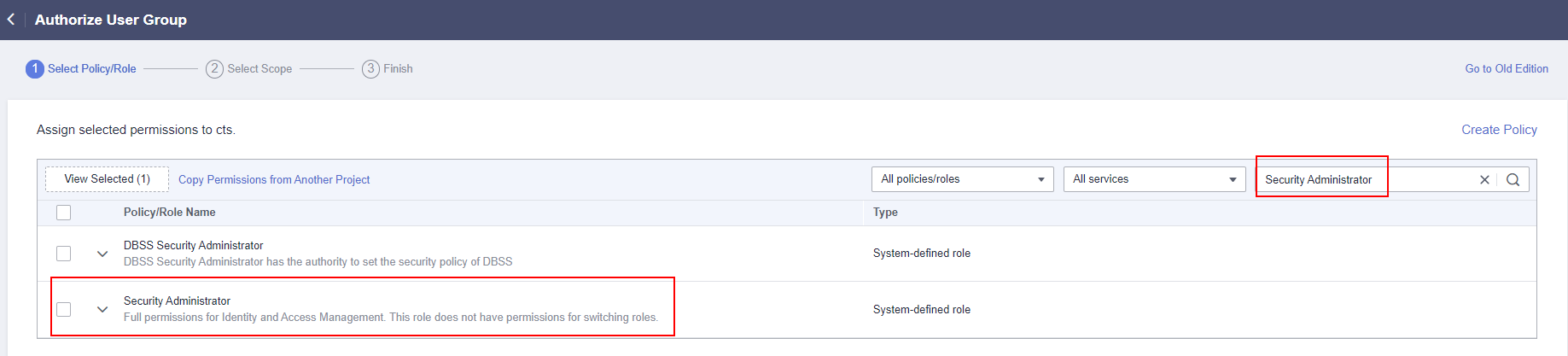
Note: Users with the Security Administrator permissions can perform all actions such as agency, role, and user management. Exercise caution when assigning the permissions.
- On the Select Scope page, select All Resources, and click OK.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





