How Do I Change the Verification Method for Performing Critical Operations?
Symptom
If operation protection is enabled, users under your account can proceed with a critical operation, such as deleting a resource and creating an access key, only after the users or the specified person completes verification.
The verification is valid for 15 minutes and you do not need to be verified again when performing critical operations within the validity period.
- To change the verification method from Self-verification to Verification by another person, see Self-verification.
- To change the verification method from Verification by another person to Self-verification or to change the mobile number or email address for verification, see Verification by another person.
Procedure
- Access the Huawei Cloud management console.
Figure 1 Logging in to the management console

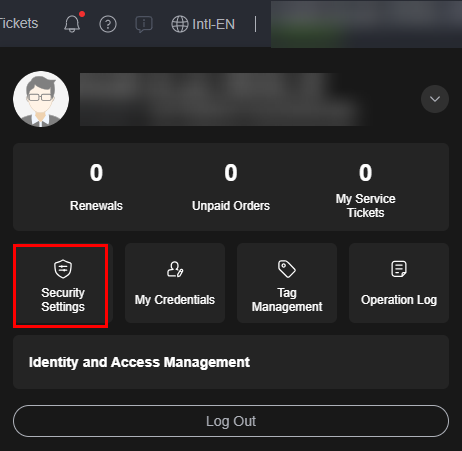
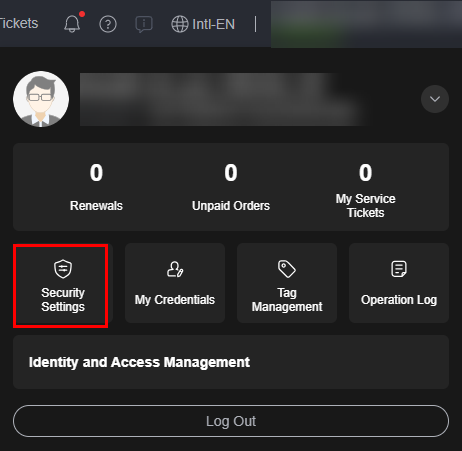
- On the management console, hover over the username in the upper right corner, and choose Security Settings from the drop-down list.
Figure 2 Security settings
- On the Security Settings page, click the Critical Operations tab, and click Change in the Operation Protection row.
Figure 3 Changing operation protection settings

- On the Operation Protection page, select Verification by another person, enter the mobile number or email address for verification, and enter the verification code.
Figure 4 Operation protection settings

- Click OK.
- Access the Huawei Cloud management console.
Figure 5 Logging in to the management console

- On the management console, hover over the username in the upper right corner, and choose Security Settings from the drop-down list.
Figure 6 Security settings
- On the Security Settings page, click the Critical Operations tab, and click Change in the Operation Protection row.
Figure 7 Changing operation protection settings

- On the Operation Protection page, select Disable and click OK. Enter the verification code and click OK.
- On the Critical Operations tab, click Enable in the Operation Protection row.
- On the Operation Protection page, select Self-verification or Verification by another person.
If you select Verification by another person, complete verification to ensure that the verification method is available.
- Self-verification: You or IAM users themselves perform verification when performing a critical operation.
- Verification by another person: The specified person performs verification when you or an IAM user performs a critical operation. Only SMS and email verification is supported. Virtual MFA devices are not supported.
- Click OK.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





