Configuring Playbooks
Scenarios
The following describes how to enable this playbook and use it to handle malware and ransomware alerts.
You need to enable this playbook manually.
Prerequisites
You have enabled access to HSS alerts and toggled on the automatic conversion of logs into alerts function on the page in the current workspace. For details, see Enabling Log Access.
Configuring and Enabling a Playbook
In SecMaster, the initial version (V1) of the HSS isolation and killing of malware workflow is enabled by default. You do not need to manually enable it. The initial version (V1) of the HSS isolation and killing of malware playbook is also activated by default. To use it, you only need to enable it.
- Log in to the SecMaster console.
- In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 1 Workspace management page

- In the navigation pane on the left, choose Security Orchestration > Playbooks. Figure 2 Accessing the Playbooks tab
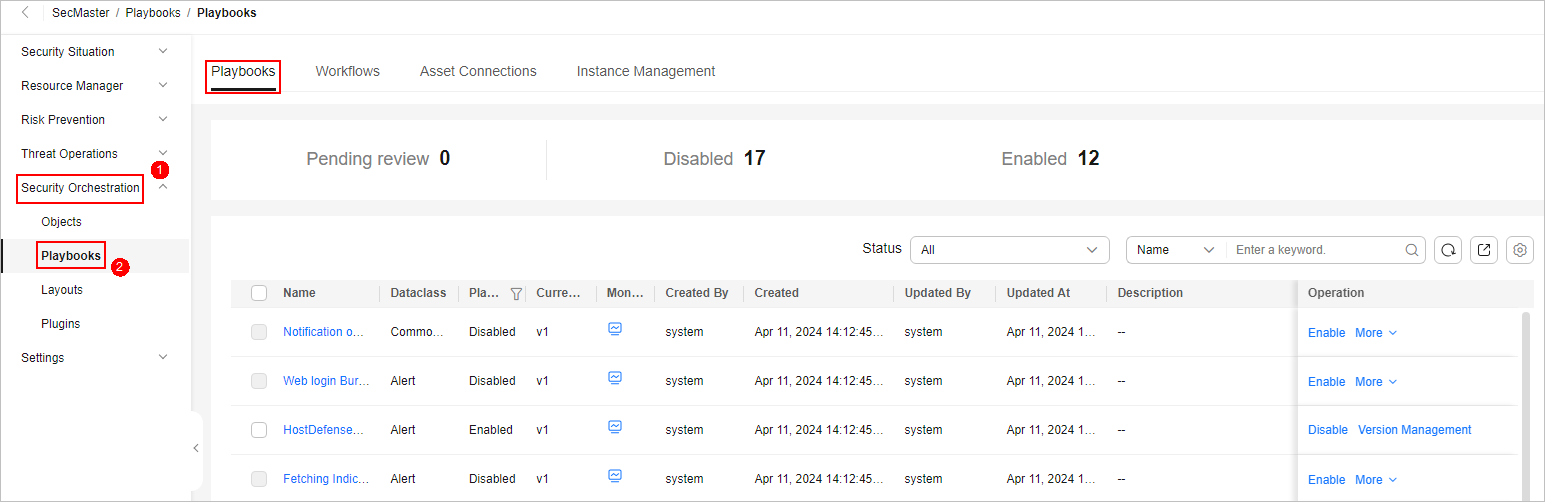
- On the Playbooks page, locate the row that contains the HSS isolation and killing of malware playbook and click Enable in the Operation column.
- In the dialog box displayed, select the initial playbook version v1 and click OK.
Implementation Effect
- The malware has been killed and the alert is closed automatically. Figure 3 Alerts automatically closed

If the isolation and killing actions are successful, choose page, click the alert name, and check the comment on the alert details page. You will find that files have been isolated and killed.
- If the isolation and killing actions fail, choose page, click the alert name, and check the comment on the alert details page. You need to manually handle the alert.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





