Viewing Results in a Chart
SecMaster supports a wide range of chart types to display query and analysis results. You can select the one you like.
SecMaster can display query and analysis results in the following types of charts:
- Displaying Query and Analysis Results in a Table
- Displaying Query and Analysis Results in a Line Chart
- Displaying Query and Analysis Results in a Bar Chart
- Displaying Query and Analysis Results in a Pie Chart
Prerequisites
You have executed query and analysis statements. For details about security analysis, see Overview. For details about query and analysis logs, see Querying and Analyzing Logs.
Procedure for Viewing Results in a Chart
The query and analysis results can be displayed in a table, line chart, bar chart, or pie chart.
- Log in to the SecMaster console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 1 Workspace management page

- In the navigation pane on the left, choose . Figure 2 Accessing the Security Analysis tab

- In the data space navigation tree on the left, click a data space name to show the pipeline list. Click a pipeline name. On the displayed page, you can search the pipeline data. Figure 3 Pipeline data page
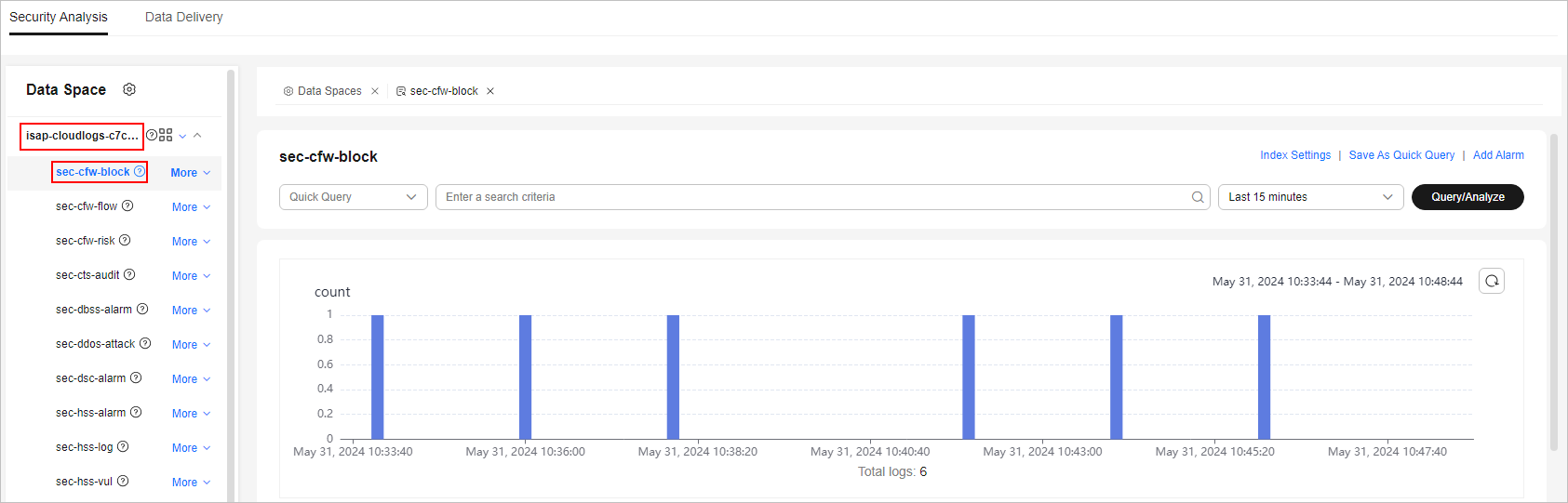
- Enter the query and analysis statement, set the time range, and click Query/Analyze.
- Select a chart type you need to display the query and analysis results.
- Displaying query and analysis results in a table
Tables are the most commonly used method to display and analyze data. In SecMaster, the data results of query and analysis statements are displayed in tables by default.
Click the Charts tab. In the Chart Type area on the right of the page, click
 .Figure 4 Table statistics
.Figure 4 Table statistics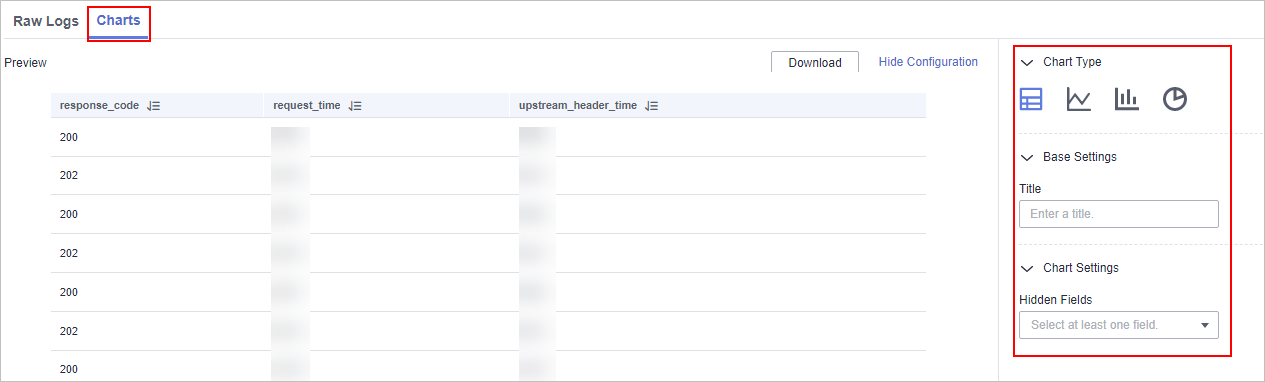
Configure table parameters.
Table 1 Table parameters Parameter Category
Parameter
Description
Base Settings
Title
Customized table title.
Chart Settings
Hidden Fields
The field you want to hide it in the table.
After the chart is configured, you can preview analysis results on the left.
- Displaying query and analysis results in a line chart
A line chart is used to display the change of a group of data in a period and show the data change trend.
Click the Charts tab. In the Chart Type area on the right of the page, click
 .Figure 5 Line chart statistics
.Figure 5 Line chart statistics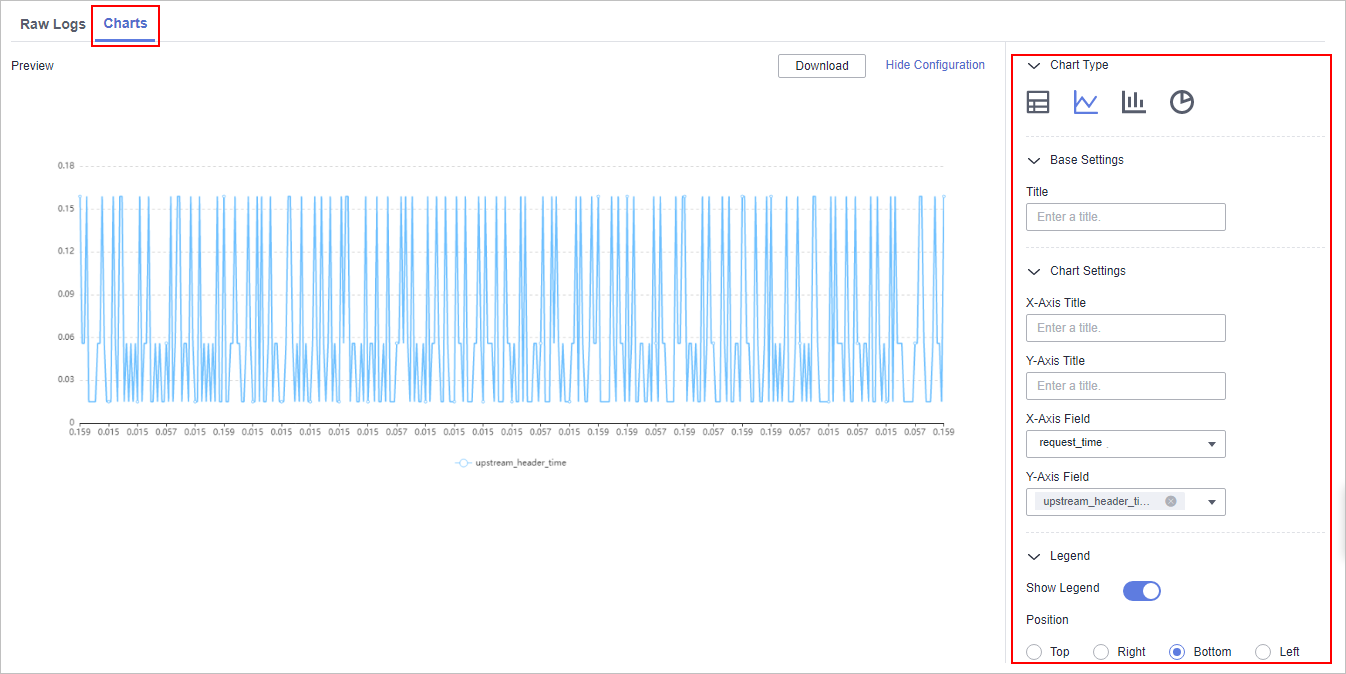
Configure line chart parameters.
Table 2 Line chart parameters Parameter Category
Parameter
Description
Base Settings
Title
Customized line chart title.
Chart Settings
X-Axis Title
Customized title of the X axis.
Y-Axis Title
Customized title of the Y axis.
X-Axis Field
Field to be displayed on the X axis.
Y-Axis Field
Field to be displayed on the Y axis.
Legend
Show Legend
Whether to display the legend.
Position
This parameter is mandatory when you choose to show the legend.
Position of the legend in the chart. The options are Top, Bottom, Left, and Right.
After the chart is configured, you can preview analysis results on the left.
- Displaying query and analysis results in a bar chart
A bar chart presents categorical data with rectangular bars. It can be used to compare data and analyze trends. In SecMaster, a bar chart uses vertical bars (the width is fixed and the height indicates the value) to display data by default.
Click the Charts tab. In the Chart Type area on the right of the page, click
 .Figure 6 Bar chart statistics
.Figure 6 Bar chart statistics
Configure bar chart parameters.
Table 3 Bar chart parameters Parameter Category
Parameter
Description
Base Settings
Title
Customized line chart title.
Chart Settings
X-Axis Title
Customized title of the X axis.
Y-Axis Title
Customized title of the Y axis.
X-Axis Field
Field to be displayed on the X axis.
Y-Axis Field
Field to be displayed on the Y axis.
Legend
Show Legend
Whether to display the legend.
Position
This parameter is mandatory when you choose to show the legend.
Position of the legend in the chart. The options are Top, Bottom, Left, and Right.
After the chart is configured, you can preview analysis results on the left.
- Displaying query and analysis results in a pie chart
A pie chart shows the proportion of different categories. Different categories are compared by radian.
Click the Charts tab. In the Chart Type area on the right of the page, click
 .Figure 7 Pie chart statistics
.Figure 7 Pie chart statistics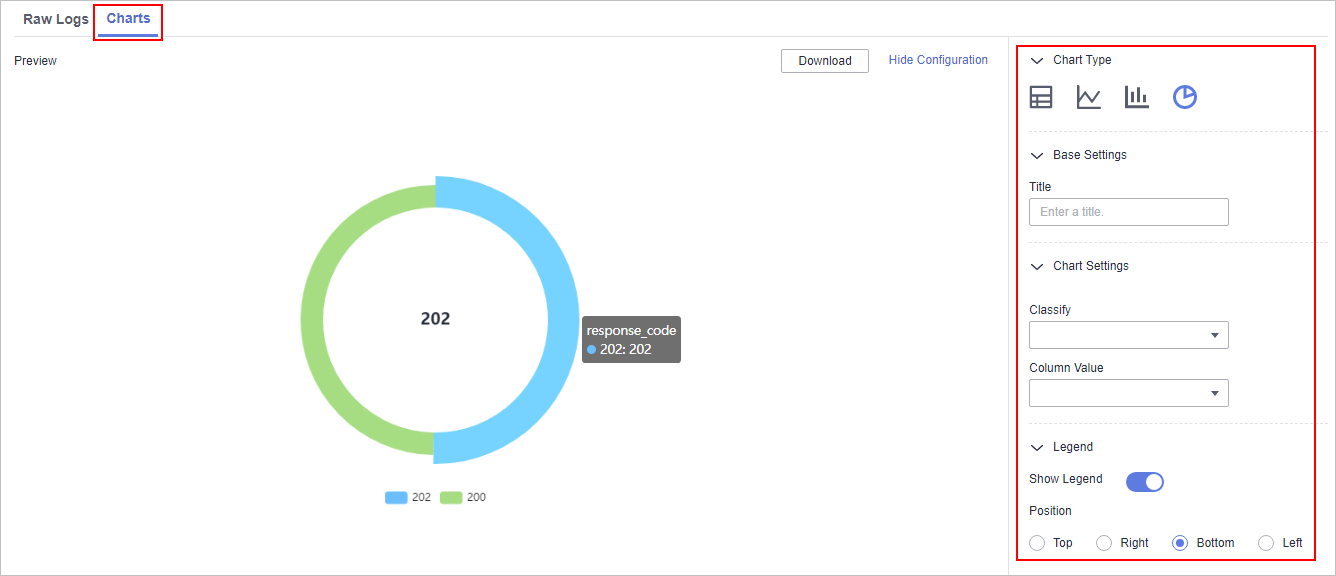
Configure pie chart parameters.
Table 4 Pie chart parameters Parameter Category
Parameter
Description
Base Settings
Title
Customized line chart title.
Chart Settings
Classify
Data classification.
Column Value
The value corresponding to the categorized data.
Legend
Show Legend
Whether to display the legend.
Position
This parameter is mandatory when you choose to show the legend.
Position of the legend in the chart. The options are Top, Bottom, Left, and Right.
After the chart is configured, you can preview the analysis result on the left.
- Displaying query and analysis results in a table
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





