Enabling a Workflow
A workflow determines how a playbook responds to threats when it is triggered. SecMaster provides some preconfigured workflows, such as WAF one-click unblocking, HSS alert synchronization, and alert metric extraction. The initial version (V1) of a workflow is automatically enabled. You can edit existing workflow versions to create custom workflows.
This topic describes how to configure and enable custom workflows. The procedure is as follows:
- Copy a workflow version.
- Editing and Submitting a Workflow Version
- Review the workflow version.
- Enable the workflow.
Prerequisites
The workflow must have an activated version. For details, see Managing Workflow Versions.
Copying a Workflow Version
- Log in to the management console.
- Click
 in the upper part of the page and choose Security > SecMaster.
in the upper part of the page and choose Security > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace.
Figure 1 Workspace management page

- In the navigation pane on the left, choose Security Orchestration > Playbooks. On the displayed page, select the Workflows tab.
Figure 2 Workflows tab

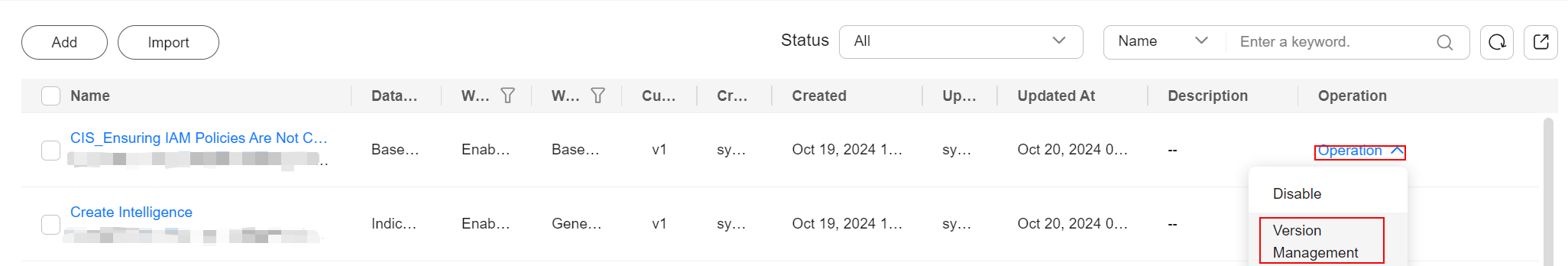
- In the Operation column of the target workflow, click More and select Version Management.
Figure 3 Version Management page
- On the Version Management slide-out panel for the workflow, in the Version Information area, locate the row containing the target workflow version, and click Clone in the Operation column.
- In the displayed dialog box, click OK.
Editing and Submitting a Workflow Version
- Log in to the management console.
- Click
 in the upper part of the page and choose Security > SecMaster.
in the upper part of the page and choose Security > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace.
Figure 4 Workspace management page

- In the navigation pane on the left, choose Security Orchestration > Playbooks. On the displayed page, select the Workflows tab.
Figure 5 Workflows tab

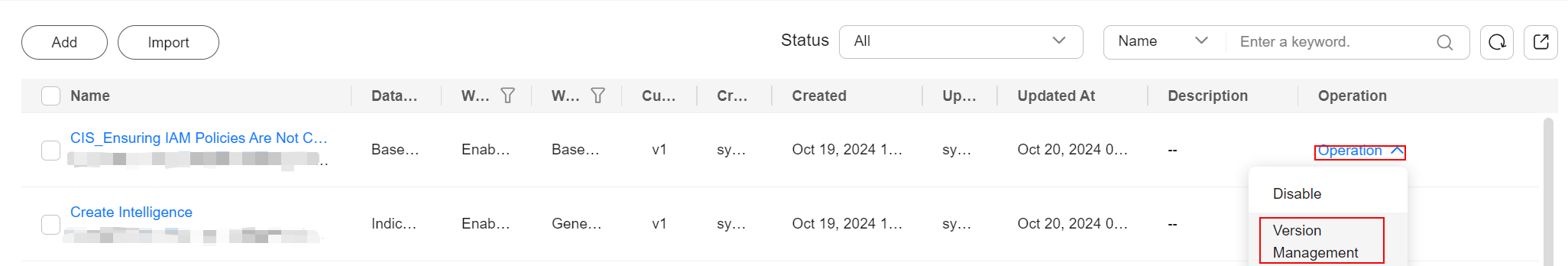
- In the Operation column of the target workflow, click More and select Version Management.
Figure 6 Version Management page
- On the Version Management slide-out panel for the workflow, in the Version Information area, locate the row containing the target workflow version, and click Edit in the Operation column.
- On the workflow canvas, drag basic, workflow, and plug-in nodes from Resource Libraries on the left to the canvas on the right.
Table 1 Resource Libraries parameters Parameter
Description
Basic
Basic Node
StartEvent
The start of the workflow. Each workflow can have only one start node. The entire workflow starts from the start node.
EndEvent
The end of the workflow. Each workflow can have multiple end nodes, but the workflow must end with an end node.
UserTask
When the workflow execution reaches this node, the workflow is suspended and a to-do task is generated.
The subsequent nodes in the workflow continue to be executed only after the user task is completed.
Table 2 describes the manual review parameters.
SubProcess
Another workflow added in the workflow. It is equivalent to the loop body in the workflow.
System Gateway
ExclusiveGateway
For an exclusive, diverging gateway, the workflow chooses only the path that matches the conditional expression to proceed.
For an exclusive, converging gateway, the workflow chooses the path arrives the gateway first to proceed.
ParallelGateway
For a parallel, diverging gateway, the workflow executes all paths arrive the gateway.
For a parallel, converging gateway, the workflow executes the subsequent node only when all paths arrive the gateway. (If one path fails, the entire workflow fails.)
InclusiveGateway
For an inclusive, diverging gateway, the workflow executes all paths that match conditional expressions.
For an inclusive, converging gateway, the workflow executes the subsequent node only when all paths executed during diverging arrive the gateway. (If one path fails, the entire workflow fails.)
Workflows
You can select all released workflows in the current workspace.
Plug-ins
You can select all plug-ins in the current workspace.
Table 2 UserTask parameters Parameter
Description
Primary key ID
A primary key ID is generated by the system. You can change it if needed.
Name
Name of the manual review node.
Valid Till
Time the manual review node expires.
Description
Description of the manual review node.
View Parameters
Click
 . On the Select Context pane displayed, select a parameter. To add a parameter, click Add Parameter.
. On the Select Context pane displayed, select a parameter. To add a parameter, click Add Parameter.Manual Processing Parameters
Input Parameter Key. To add a parameter, click Add Parameter.
- After the design is complete, click Save and Submit in the upper right corner. In the automatic workflow verification dialog box displayed, click OK.
If the workflow verification fails, check the workflow based on the failure message.
Reviewing a Workflow Version
- Log in to the management console.
- Click
 in the upper part of the page and choose Security > SecMaster.
in the upper part of the page and choose Security > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace.
Figure 7 Workspace management page

- In the navigation pane on the left, choose Security Orchestration > Playbooks. On the displayed page, select the Workflows tab.
Figure 8 Workflows tab

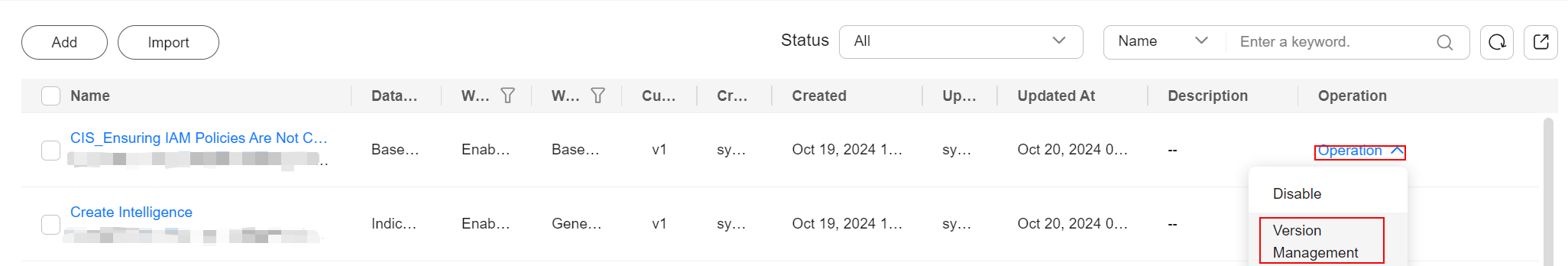
- In the Operation column of the target workflow, click More and select Version Management.
Figure 9 Version Management page
- On the Version Management slide-out panel, click Review in the Operation column of the target workflow.
- Set Comment. Table 3 describes the parameters.
Table 3 Workflow review parameters Parameter
Description
Comment
Select the review conclusion.
- Passed: If the workflow version is approved, the status of the workflow version changes to Activated.
- Reject. If the workflow version is rejected, the status of the workflow version changes to Rejected. You can edit the workflow version and submit it again.
Reason for Rejection
Enter the review comment. This parameter is mandatory when Reject is selected for Comment.
- You can edit a rejected workflow version. For details, see Managing Workflow Versions.
- Workflow version status change:
If the current workflow has only one workflow version, the status of the approved workflow version Status is Activated by default.
- Click OK to complete the workflow version review.
Enabling a Workflow
- Log in to the management console.
- Click
 in the upper part of the page and choose Security > SecMaster.
in the upper part of the page and choose Security > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace.
Figure 10 Workspace management page

- In the navigation pane on the left, choose Security Orchestration > Playbooks. On the displayed page, select the Workflows tab.
Figure 11 Workflows tab

- In the row containing the target workflow, click Enable in the Operation column.
- In the slide-out panel that is displayed, select the workflow version to be enabled and click OK.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





