Viewing and Handling Ransomware Prevention Events
Scenarios
After ransomware protection is enabled, if a ransomware attack event occurs on the server, the event will be recorded and displayed in the ransomware event list. You can handle the events based on your service requirements.
Constraints
After ransomware protection is enabled, you need to handle ransomware alarms and fix the vulnerabilities in your systems and middleware in a timely manner.
Viewing and Handling Ransomware Prevention Events
- Log in to the HSS console.Log in to the management console.
- Click
 in the upper left corner and select a region or project.
in the upper left corner and select a region or project. - Choose Server Protection > Ransomware Prevention.
- (Optional) If you have enabled the enterprise project function, select an enterprise project from the Enterprise Project drop-down list in the upper part of the page to view its data.
- Click the Events tab and check events.
To check alarm details, click an alarm name.
- After confirming the severity of an event, click Handle in the Operation column of the target event to handle the event.
You can also select multiple events and click Batch Handle above the list to handle events in batches.
- In the Handle Event dialog box, select an action. For details, see Table 1. Figure 1 Selecting an action
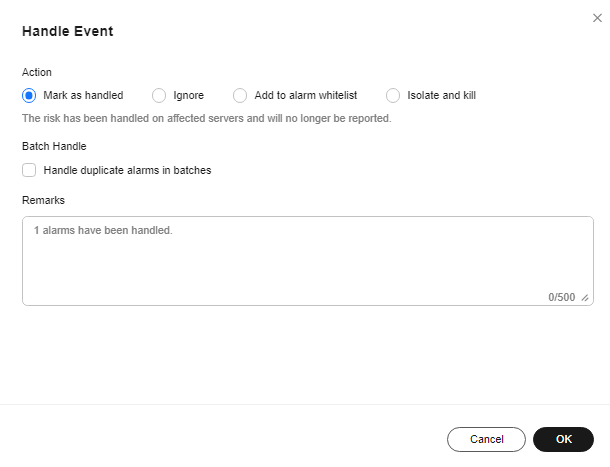
Table 1 Alarm handling methods Parameter
Description
Action
- Mark as handled
For a manually handled event, you can add remarks to record the details about the event.
- Ignore
Ignore the current alarm. Any new alarms of the same type will still be reported by HSS.
- Add to alarm whitelist
Add false alarmed items to the login whitelist.
HSS will no longer report alarm on the whitelisted items. A whitelisted alarm will not trigger alarms.
After adding an alarm to the alarm whitelist, you can customize a whitelist rule. The custom rule types vary depending on the alarm types, including the file path, process path, process command line, remote IP address, and user name. By default, HSS automatically fills in the rule based on the alarm summary. You can modify the rule as required. If a detected alarm event hit the rule you specified, HSS does not generate an alarm.
- Isolate and kill
If a program is isolated and killed, its executable file status will change to read-only, and the program will be terminated immediately. To avoid impact on services, exercise caution when performing this operation. Isolated source files of programs or processes are displayed on the Isolated Files slide-out panel and cannot harm your servers.
You can click Isolated Files in the upper right corner to check the files. For details, see Managing Isolated Files.
Batch Handle
If this option is selected, the same alarms triggered at different time are handled in batches. If no duplicate alarm is displayed after you select it, it indicates no duplicate alarms have been generated.
Remarks
You can add remarks for convenient backtracking.
- Mark as handled
- Click OK.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.






