Accessing Huawei Cloud Through a VPN (Different Regions)
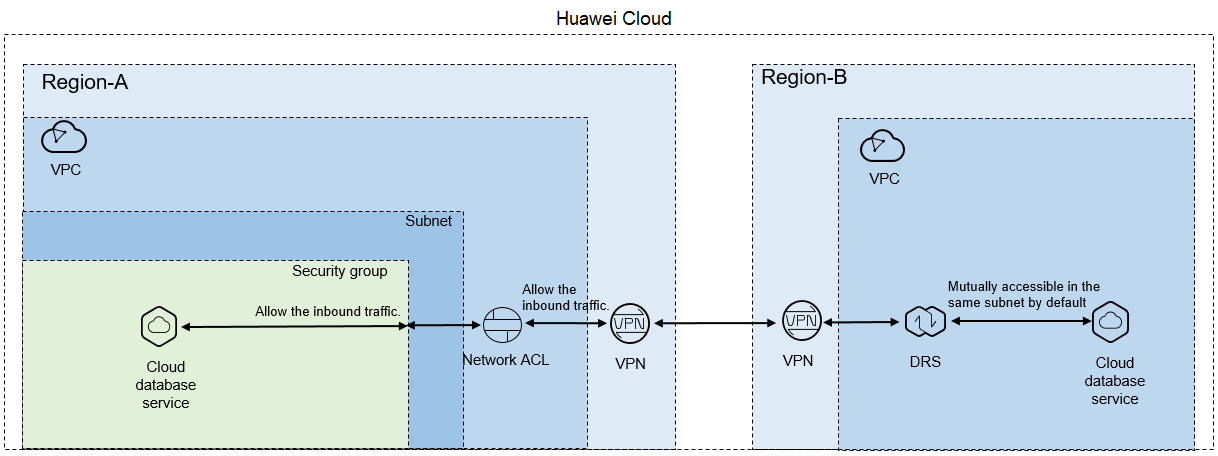
Figure 1 shows how to use DRS to migrate data across databases in different regions over a VPN network on Huawei Cloud.
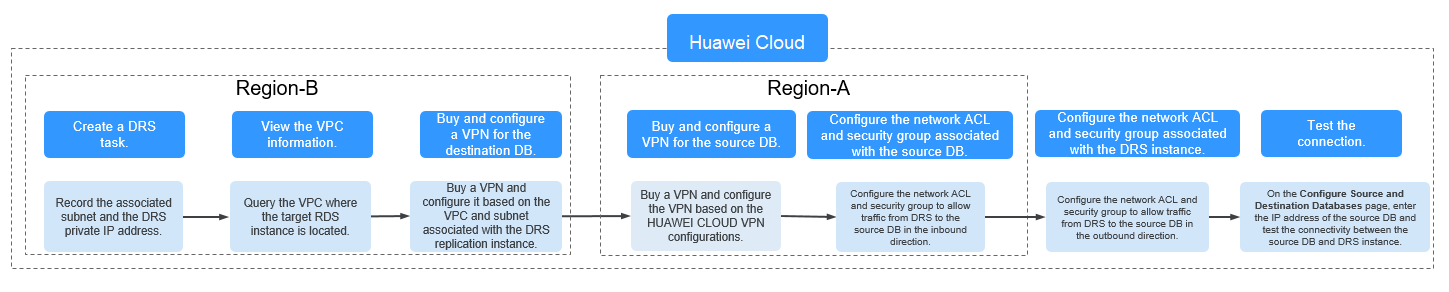
If you use DRS to access a cross-region database through a VPN, create the VPN service on Huawei Cloud in Region-B and configure the VPC and subnet associated with the DRS replication instance. In addition, create the VPN service in Region-A, configure the VPN peer device, and add inbound rules for the network ACL and security group associated with the source database in Region-A to allow traffic from the private IP address of the replication instance. Then, configure outbound rules for the network ACL and security group associated with the replication instance in Region-B to allow outbound traffic. Figure 2 shows the process.
Network Configurations
- Create a DRS instance and obtain the subnet and private IP address of the DRS instance.
By default, the DRS instance is in the same subnet as the destination database.
Figure 3 Replication instance information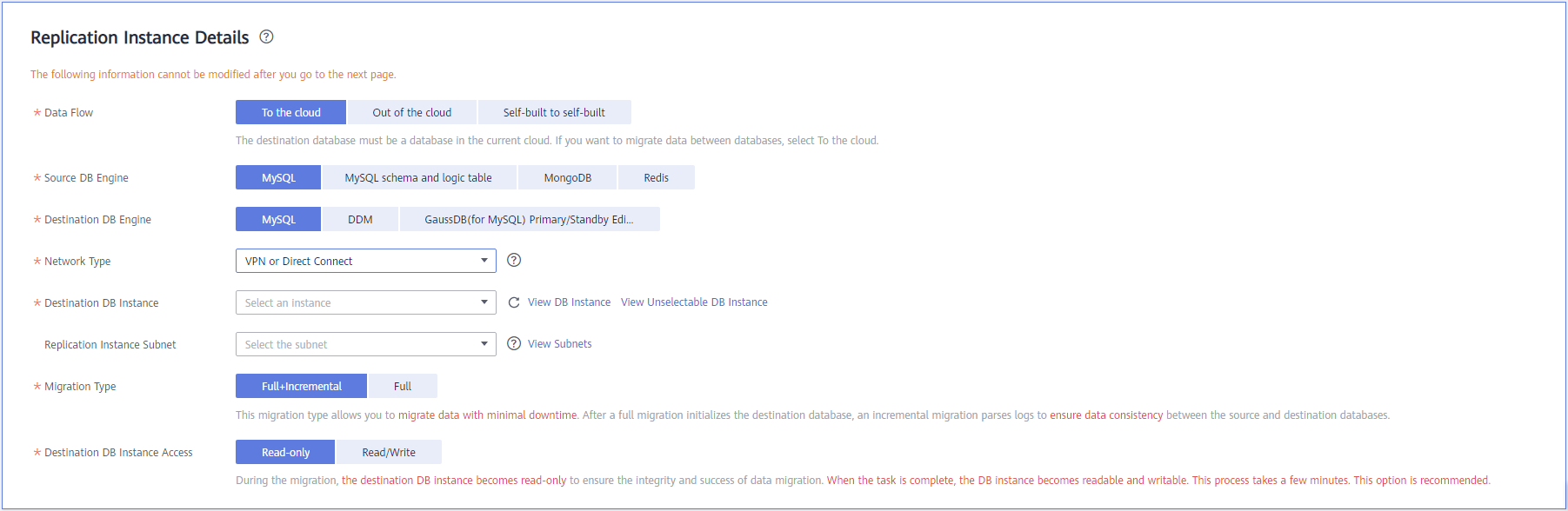
After the DRS replication instance is created, the private IP address of the replication instance is displayed.
Figure 4 Private IP address of the DRS instance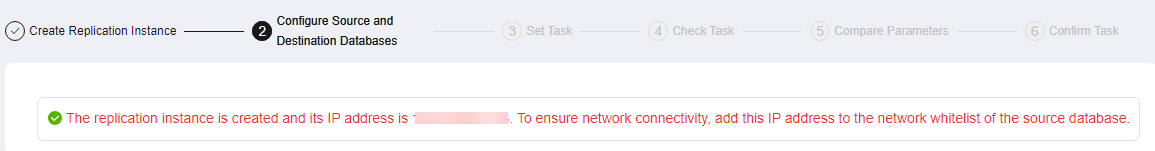
- Query the name of the VPC to which the DRS instance belongs.
By default, the DRS replication instance and the destination RDS database are created in the same VPC. You can log in to the destination RDS instance to view information about the VPC where the replication instance is located.
Figure 5 Destination database information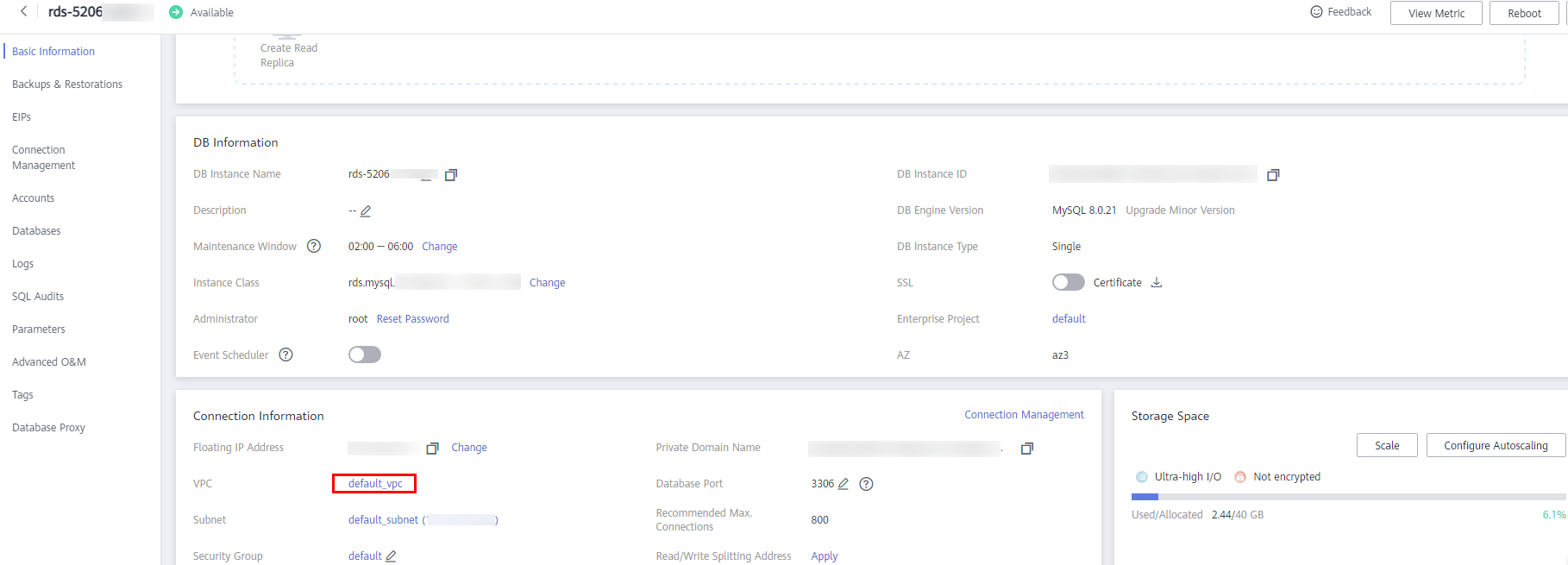
- Create a VPN in the target region and configure the VPN gateway and connection.
For details, see Getting Started with Virtual Private Network.
When you create a VPN gateway, configure the VPC by referring to the VPC information obtained in 2. When you create a VPN connection, configure the subnet associated with the replication instance by referring to the subnet information obtained in 1.
- Create a VPN in the source region and configure the VPN peer device.
For details, see "Configuring the Remote Device" in Getting Started with Virtual Private Network.
- Configure inbound rules for the network ACL and security group associated with the source database.
Security group: Add an inbound rule to allow traffic from the private IP address of the DRS replication instance to the database listening port.
Network ACL: By default, a VPC does not have a network ACL. If you have a network ACL, add an inbound rule to allow traffic from the private IP address and random port of the DRS replication instance to the IP address and listening port of the source database.
- Configure outbound rules for the network ACL and security group associated with the replication instance.
By default, a VPC does not have a network ACL, and the default security group rules allow all outbound traffic. The replication instance and destination RDS database in the same security group can communicate with each other by default, so you do not need to configure a network ACL.
If you have configured a network ACL or security group, log in to the VPC management console and check the settings:
Security group: Ensure that the outbound traffic from the security group associated with the replication instance to the IP address and listening port of the source database is allowed.
Network ACL: Ensure that the outbound traffic from the VPC where the replication instance resides and the DRS random port to the IP address and listening port of the source database is allowed.
- Test the connection.
Log in to the DRS console, locate the created DRS task, and click Edit in the Operation column. On the Configure Source and Destination Databases page, enter the IP address, port, username, and password of the source database and then click Test Connection to check whether the connection is successful.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.