Configuring Security Group Rules
Context
A security group is a collection of access control rules for ECSs and RDS DB instances that have the same security protection requirements and are mutually trusted in a VPC.
Scenarios
First check whether the ECS and RDS DB instance are in the same security group.
- If they are in the same security group, they can communicate with each other by default. No security group rule needs to be configured. Go to Connecting to a DB Instance Using a MariaDB Client.
- If they are in different security groups, configure security group rules for them, separately.
- RDS DB instance: Configure an inbound rule for the security group with which the RDS DB instance is associated.
- ECS: The default security group rule allows all outgoing data packets. In this case, you do not need to configure a security group rule for the ECS. If not all outbound traffic is allowed in the security group, you need to configure an outbound rule for the ECS.
Constraints
The default security group rule allows all outgoing data packets. ECSs and RDS DB instances can access each other if they are in the same security group. After a security group is created, you can configure security group rules to control access from and to the DB instances in the security group.
- By default, you can create a maximum of 100 security groups in your cloud account.
- By default, you can add up to 50 security group rules to a security group.
- One RDS instance can be associated only with one security group, but one security group can be associated with multiple RDS instances.
- Too many security group rules will increase the first packet latency. You are advised to create no more than 50 rules for a security group.
- To enable access to an RDS DB instance from resources outside the security group, you need to configure an inbound rule for the security group associated with the RDS DB instance.
The default value of Source is 0.0.0.0/0, indicating that RDS DB instances in the security group can be accessed from any IP address.
Procedure
- Log in to the management console.
- Click
 in the upper left corner of the page and choose Databases > Relational Database Service.
in the upper left corner of the page and choose Databases > Relational Database Service. - On the Instances page, click the DB instance name.
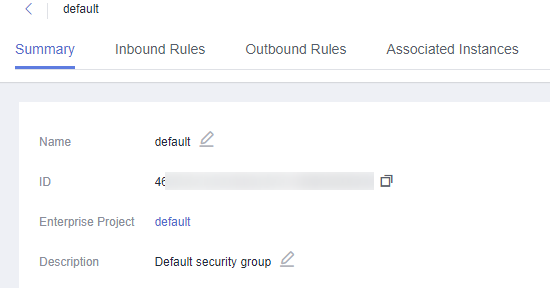
- In the navigation pane, choose Connectivity & Security. In the Security Group Rules area, click the security group name.
Figure 1 Security group rules
- On the Inbound Rules tab, click Add Rule. In the displayed dialog box, set required parameters to add an inbound rule.
To add more inbound rules, click
 .
.Table 1 Inbound rule parameter description Parameter
Description
Example Value
Priority
Security group rule priority.
Value range: 1 to 100. The default priority is 1 and has the highest priority. The security group rule with a smaller value has a higher priority.
1
Action
Security group rule action. Its value can be:
- Allow: Access from the source is allowed to DB instances in the security group over specified ports.
- Deny: Access from the source is denied to DB instances in the security group over specified ports.
Deny rules take precedence over allow rules of the same priority.
Allow
Protocol & Port
Protocol: network protocol. Available options: All, TCP, UDP, ICMP, or GRE.
Protocols/TCP (Custom ports)
Port: the port over which the traffic can reach your DB instance.
RDS for MariaDB instances can use database ports 1024 to 65535, excluding 12017 and 33071, which are reserved for RDS system use.
3306
Type
Supported source IP address type. Its value can be:
- IPv4
- IPv6
IPv4
Source
The source in an inbound rule is used to match the IP address or address range of an external request. The source can be:
- Single IP address: 192.168.10.10/32 (IPv4 address)
- IP address segment: 192.168.1.0/24 (IPv4 address segment)
- All IP addresses: 0.0.0.0/0 (any IPv4 address)
- Security group: sg-abc
- IP address group: ipGroup-test
0.0.0.0/0
Description
Supplementary information about the security group rule. This parameter is optional.
The description can contain a maximum of 255 characters and cannot contain angle brackets (<) or (>).
N/A
- Click OK.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.






