Network Policies
Network policies are designed by Kubernetes to restrict pod access. Like a firewall at the application layer, network policies enhance network security. The capabilities of network policies are determined by the network add-ons available in the cluster.
By default, if a namespace does not have any policies configured, pods in the namespace accept traffic from any ingress sources and send traffic to any egress destinations.
There are three kinds of selectors available for network policies:
- namespaceSelector: selects particular namespaces for which all pods should be allowed as ingress sources or egress destinations.
- podSelector: selects particular pods in the same namespace as the network policy which should be allowed as ingress sources or egress destinations.
- ipBlock: selects particular IP address ranges that are allowed as ingress sources or egress destinations.
Using Ingress Rules Through YAML
- Scenario 1: Controlled by a preset network policy, a pod can only be accessed by pods with specific labels. Figure 1 podSelector
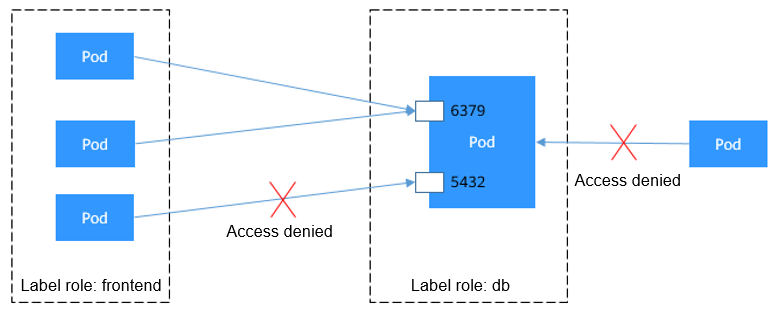
The pod labeled with role=db only permits access to its port 6379 from pods labeled with role=frontend. To achieve this, take the following steps:
- Create the access-demo1.yaml file.
vim access-demo1.yaml
File content:
apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: access-demo1 namespace: default spec: podSelector: # The rule takes effect for pods with the role=db label. matchLabels: role: db ingress: # This is an ingress rule. - from: - podSelector: # Only allows the access of the pods labeled with role=frontend. matchLabels: role: frontend ports: # Only TCP can be used to access port 6379. - protocol: TCP port: 6379 - Run the following command to create the network policy defined in the access-demo1.yaml file:
kubectl apply -f access-demo1.yaml
Expected output:
networkpolicy.networking.k8s.io/access-demo1 created
- Create the access-demo1.yaml file.
- Scenario 2: Controlled by a preset network policy, a pod can only be accessed by pods in a specific namespace. Figure 2 namespaceSelector
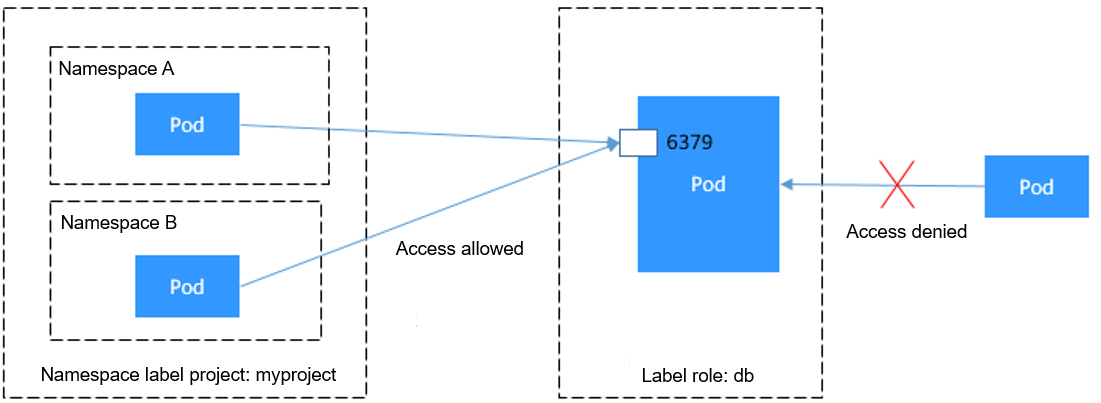
The pod labeled with role=db only permits access to its port 6379 from pods in the namespace labeled with project=myproject. To achieve this, take the following steps:
- Create the access-demo2.yaml file.
vim access-demo2.yaml
File content:
apiVersion: networking.k8s.io/v1 kind: NetworkPolicy metadata: name: access-demo2 spec: podSelector: # The rule takes effect for pods with the role=db label. matchLabels: role: db ingress: # This is an ingress rule. - from: - namespaceSelector: # Only allows the access of the pods in the namespace labeled with project=myproject. matchLabels: project: myproject ports: # Only TCP can be used to access port 6379. - protocol: TCP port: 6379 - Run the following command to create the network policy defined in the access-demo2.yaml file:
kubectl apply -f access-demo2.yaml
Expected output:
networkpolicy.networking.k8s.io/access-demo2 created
- Create the access-demo2.yaml file.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.






