How to Determine Whether an Attack Occurs?
To check whether a public IP address is attacked, perform the following operations:
- For details about how to query attack traffic information and anomaly events within 24 hours, see Method 1: Viewing Monitoring Reports.
- For details about how to query information about public IP addresses attacked within one month, see Method 2: Viewing the Security Report.
Method 1: Viewing Monitoring Reports
- Log in to the management console.
- Select a region in the upper part of the page, click
 in the upper left corner of the page, and choose . The Anti-DDoS page is displayed.
in the upper left corner of the page, and choose . The Anti-DDoS page is displayed. - Click the Public IP Addresses tab, locate the row that contains the IP address of which you want to view its monitoring report, and click View Monitoring Report.
- Check whether there are attack traffic and anomaly events.
- On the Traffic tab page, check whether there is attack traffic displayed in the corresponding time range. If there is, the public IP address is attacked.
- Check whether there are abnormal events in the event list at the bottom. If there are abnormal events, the public IP address is attacked.
Figure 1 Monitoring reports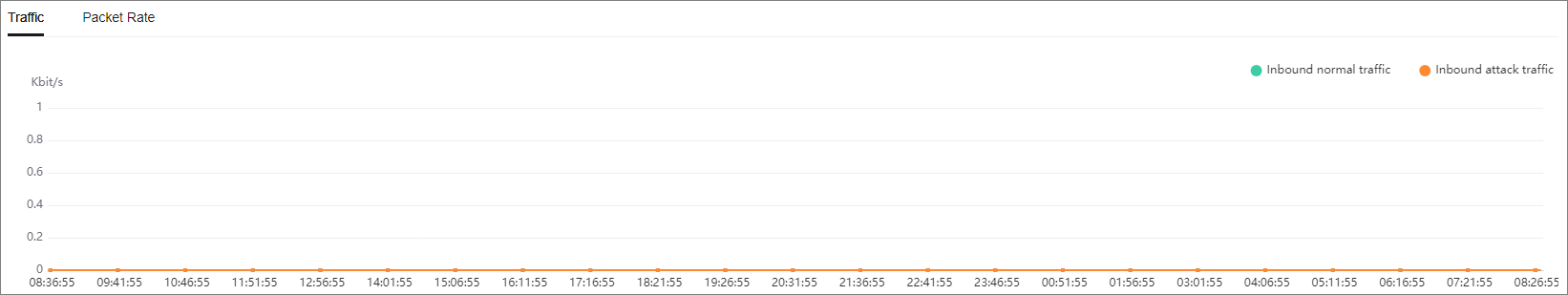
Method 2: Viewing the Security Report
- Log in to the management console.
- Select a region in the upper part of the page, click
 in the upper left corner of the page, and choose . The Anti-DDoS page is displayed.
in the upper left corner of the page, and choose . The Anti-DDoS page is displayed. - Click the Security Report tab, select a time range, and check whether the queried public IP address is in Top 10 Attacked Public IP Addresses.
If the public IP address is in Top 10 Attacked Public IP Addresses, the public IP address is attacked.
Figure 2 Security report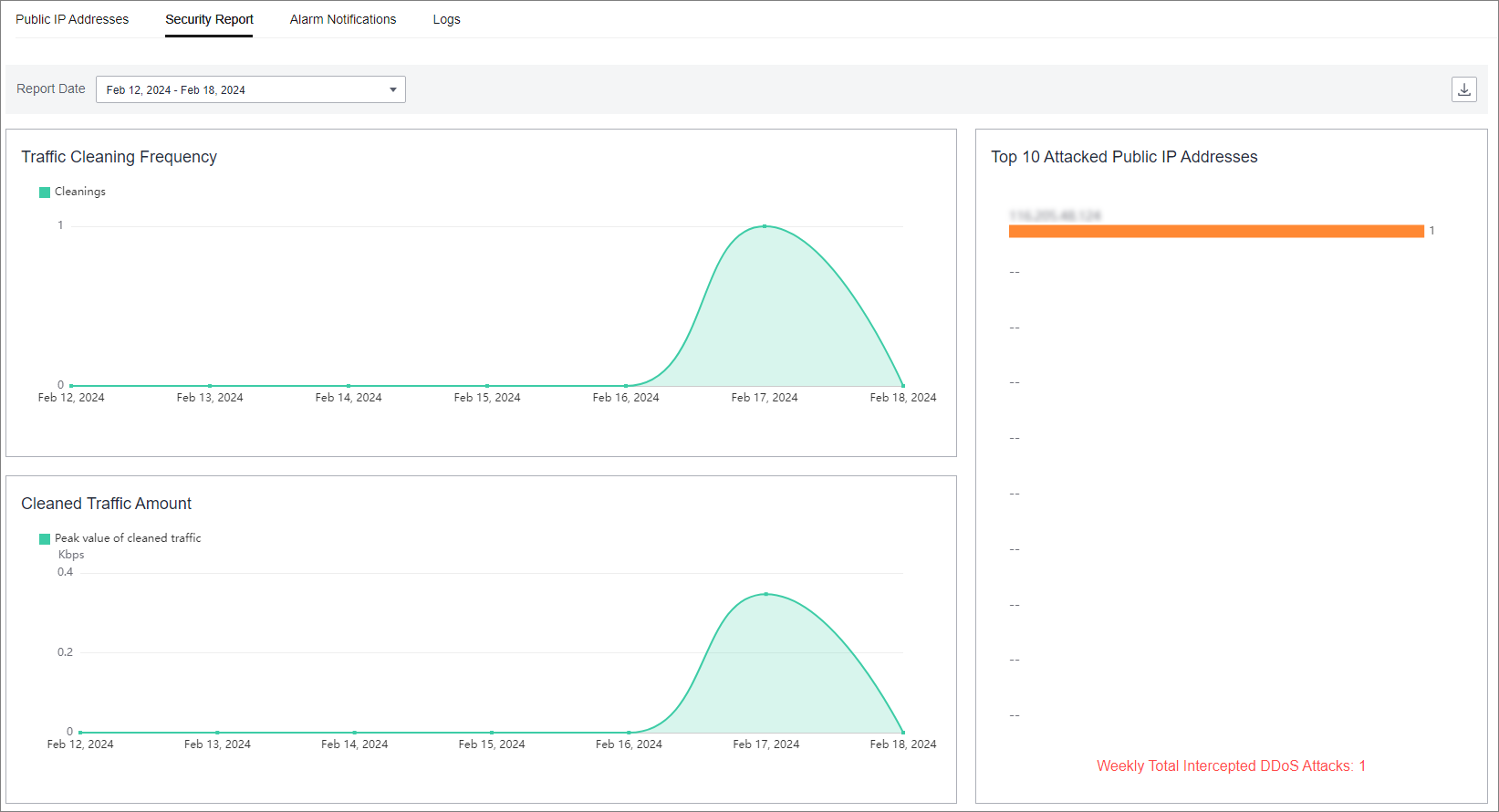
About Anti-DDoS FAQs
- What Is Anti-DDoS?
- What Are a SYN Flood Attack and an ACK Flood Attack?
- What Is a CC Attack?
- What Is a Slow HTTP Attack?
- What Are a UDP Attack and a TCP Attack?
- What Is the Million-level IP Address Blacklist Database?
- How Will Anti-DDoS Be Triggered to Scrub Traffic?
- Does Anti-DDoS Traffic Cleaning Affect Normal Services?
- How Does Anti-DDoS Scrub Traffic?
- What Are the Restrictions of Anti-DDoS?
- What Is the Protection Capacity of Anti-DDoS?
- What Data Can Be Provided by Anti-DDoS?
- In Which Regions Is Anti-DDoS Available?
- What Is the Maximum Protection Capacity Provided by HUAWEI CLOUD Anti-DDoS for Free?
- Which Services Can Use Anti-DDoS?
- Can Anti-DDoS Be Used Across Clouds?
- How to Determine Whether an Attack Occurs?
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.
more









