Scanning an Image
Scenarios
Image scans ensure the security of images throughout their lifecycle, including development, deployment, and running. They scan for system vulnerabilities, application vulnerabilities, malicious files, software information, file information, unsafe baseline settings, weak passwords, sensitive information, software compliance issues, and base image information. This helps you identify and fix risks and ensures images have passed strict checks before being deployed in the production environment. In this way, your system and applications can run stably and securely.
SWR Enterprise Edition allows you to scan all hosted images, generates vulnerability scanning reports, and provides solutions to keep your images safe. There are two types of image scans:
- Manual scans: You can manually scan an artifact.
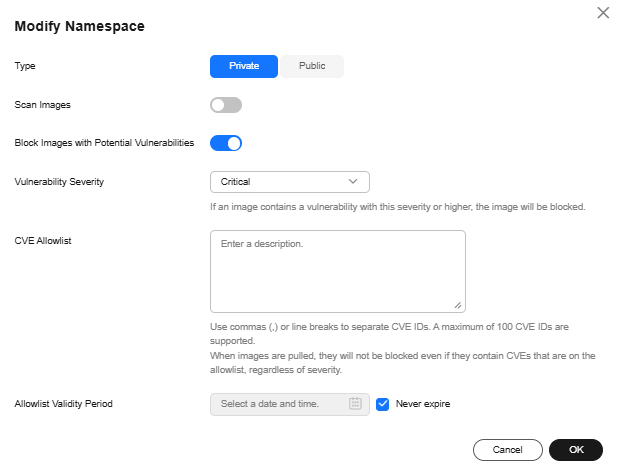
- Automatic scans: You can enable automatic scans for a namespace. After automatic scans are enabled, images uploaded to the namespace are automatically scanned. Images synchronized to the namespace are also scanned.
If an image has vulnerabilities, you can configure image download blocking for the namespace. In this way, images cannot be downloaded, which effectively reduces vulnerability risks in the production environment. If images with specific vulnerabilities still need to be downloaded, you can configure a vulnerability allowlist. If all vulnerabilities of an image are in the allowlist, the image can be downloaded.

- When all detected vulnerabilities are in the allowlist, the image download will not be blocked, which means that the images can still be downloaded.
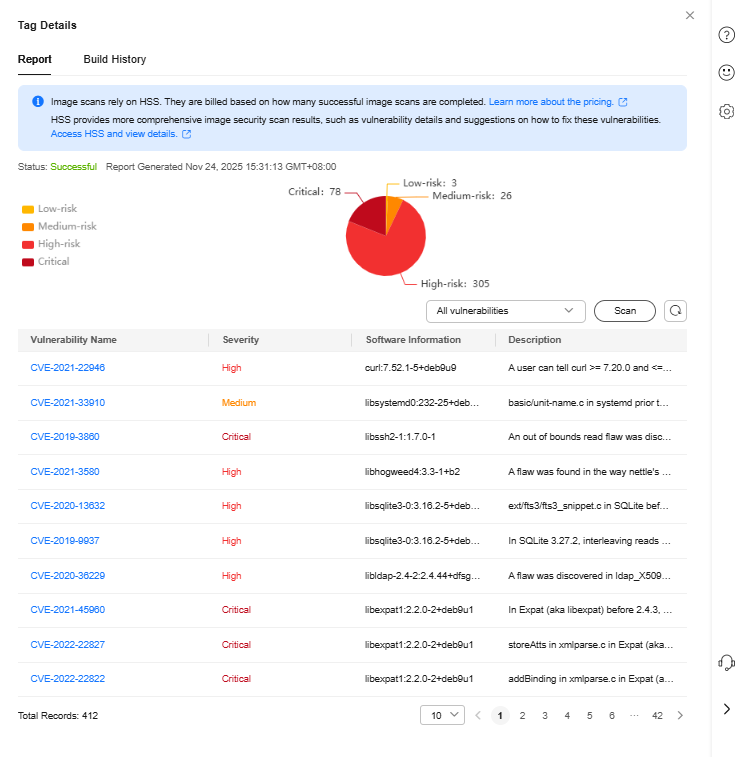
- Image scans rely on HSS. They are billed based on how many successful image scans are completed. For details, see HSS Billing Items. HSS supports scanning of specific OSs and media types. For details, see Repository Image Security Scan Items.
Constraints
- In a single SWR Enterprise Edition instance, a maximum of 10 concurrent artifact scans can be performed each time.
- Only single-architecture images can be scanned. Multi-architecture images and Helm chart packages cannot be scanned.
- The total size of images to be scanned cannot exceed 50 GB. There should be fewer than 127 image layers, and the size of each image layer cannot exceed 10 GB.
Prerequisites
- To perform image scans in SWR Enterprise Edition, you need to enable image scans on the HSS console first. For details, see Enabling Pay-per-Use Container Image Scan. Also, you need to grant HSS the permissions required for periodically synchronizing images from the repositories. Perform the authorization as prompted on the HSS console.
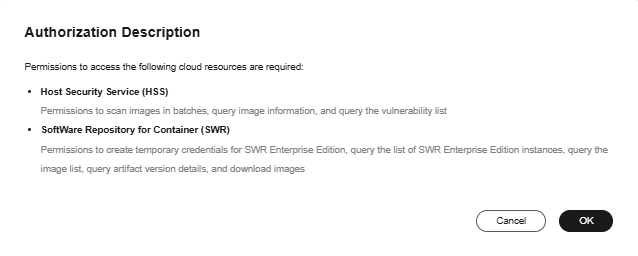
- You have completed artifact scan authorization. If the authorization has not been completed, follow the instructions on the page to complete it. For details, see Artifact scan authorization in Table 1.
Feature Gates
|
Feature Gate |
How to Enable/Disable |
Remarks |
|---|---|---|
|
Artifact scan authorization |
|
The authorization is only valid in the current region. If you switch to another region, you need to perform the authorization again.
CAUTION:
For a single tenant, this operation needs to be performed only once in each region. |
|
Automatic scans |
|
When you create a namespace, this option is disabled by default and cannot be configured. It can be only configured when you modify the namespace. |
|
Blocking images with potential vulnerabilities |
|
When you create a namespace, this option is disabled by default and cannot be configured. It can be only configured when you modify the namespace.
NOTE:
|
Manually Scanning an Image
- Log in to the SWR Enterprise Edition console and switch to the target region in the upper left corner of the page. Click the repository name.
- In the navigation pane, choose Repositories. Click the image name. On the page that is displayed, locate the image you want to scan and click Scan in the Operation column.
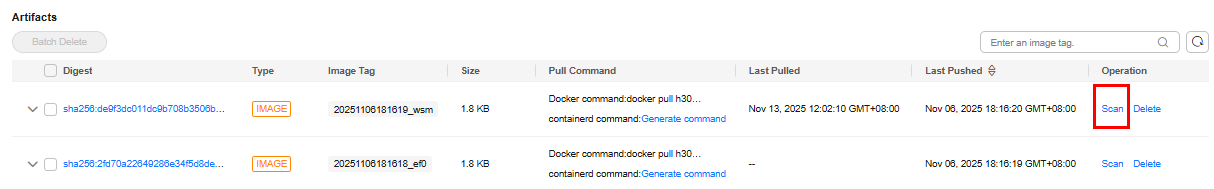

Images that are not tagged cannot be scanned.
- View the scan report that is automatically displayed.
Common Image Scan Failures
|
Cause |
Solution |
|---|---|
|
Access to SWR failed. |
Submit a service ticket to request technical support. |
|
SWR authorization has not been completed. |
Complete the authorization. For details, see Authorization Methods. |
|
The image details could not be obtained. The image was not found in the repository. |
On the Host & Container Security Service console, choose Risk Management > Container Images > in the navigation pane, click the Repository Images tab, and click Synchronize Images to update the image list and check whether the image exists. |
|
Failed to download the image. |
Submit a service ticket to request technical support. |
|
The image is oversized. |
The total image size cannot exceed 50 GB. You are advised to simplify images. |
|
The image has too many layers. |
An image can contain a maximum of 127 layers, and each layer cannot exceed 10 GB. You are advised to simplify images. |
|
Schema v1 images cannot be scanned. |
You are advised to upgrade schema v1 to schema v2. |
|
If the image scan duration exceeds 3 hours, SWR automatically stops the scan. |
You are advised to simplify images. |
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot