Data Watermarking Overview
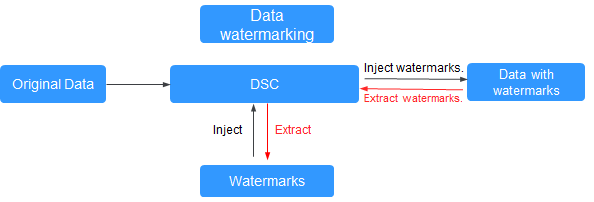
If data leakage occurs, you can use DSC to extract the watermark information. In this case, the organization or person that is accountable for the leakage problem can be easily found. Adding watermarks does not affect the distributed data usage.
|
Database Type |
Data Type |
|---|---|
|
DWS |
smallint, integer, bigint, float4, float8, varchar, text, and char |
|
MRS-HIVE |
smallint, int, long, float, double, and string |
|
Type |
Format |
|---|---|
|
Document |
pdf, pptx, docx, and xlsx |
|
JSON data (invoking data watermark APIs) |
The value can be an integer, floating-point number, or string. |
|
Type |
Format |
|---|---|
|
Images (or invoking image watermark APIs) |
jpg, jpeg, png, bmp, tiff, tif, tga, and gif |
Application Scenarios
Data watermarking is widely used in government departments, healthcare agencies, finance institutions, academic institutes, and other organizations. It is generally used for copyright protection and source tracing.
- Data copyright protection: In scenarios where digital works are downloaded or copied for use and database services (data mining and analysis) provide data to third parties, digital watermarks can be used to identify the copyright when disputes occur,
- Source tracing: Data provided for internal employees or third parties can be injected with watermarks to identify the ownership and remind them of keeping the data secure. When the data leaked, the watermarks can be used to trace the source of data leak and identify the root cause.
Advantages and Highlights
- Visible and invisible watermarks: You can inject visible or invisible watermarks into the data as needed to efficiently cope with data theft through image process tools, picture taking, or screenshots.
- Detectable and tamper-proofing: Watermarks injected into the data can be detected and will not be lost, fabricated, and tampered with.
- High robustness: Watermarks are not easily removed during transmission or use. Even if the data carrier is tampered with or damaged, there is a high probability that watermarks are extracted.
Procedure
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





