Network Isolation and Access Control
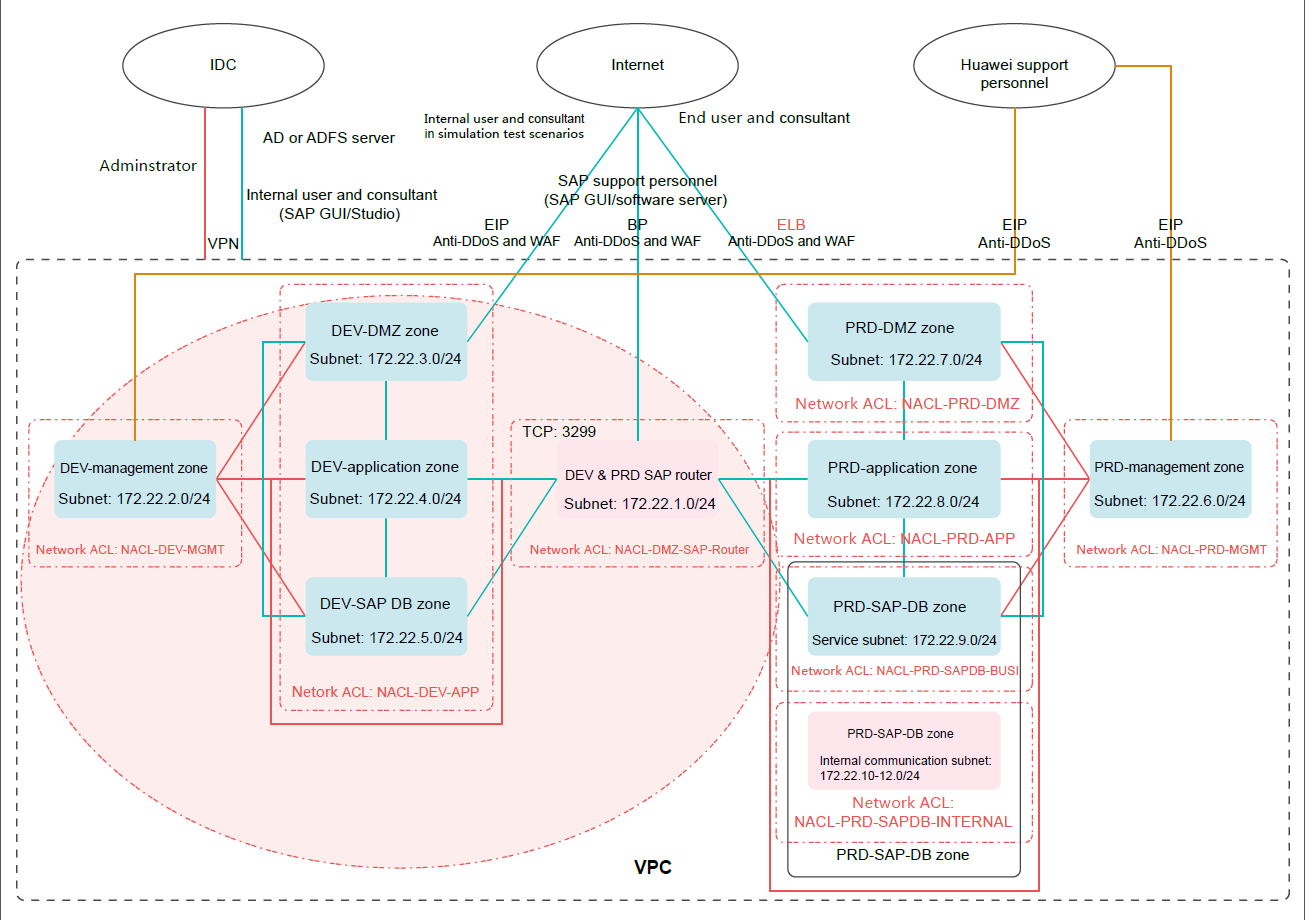
Figure 1 shows the SAP development and test environment security solution.
The development and test environment is only used for service development and tests in an enterprise. When this characteristic and enterprise security practices are taken into consideration, you can configure relatively loose network isolation and access control policies for the development and test environment, thereby ensuring network deployment flexibility.
The development and test environment has a low security level and a high security risk. Therefore, if you need to connect the development and test environment to the production environment, configure relatively tight access control policies for the border between the two environments.
In addition, configure security groups to specify open ports according to the "minimum permission" principle. Source IP address access control is performed using network ACLs instead of security groups.
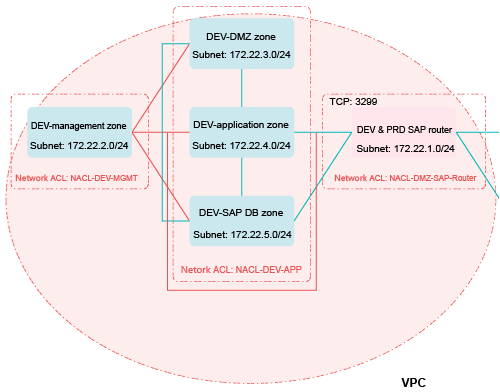
Figure 2 shows the subnet and network ACL layout in the SAP development and test environment.
Security Policies
Network ACLs for the development and test environment are NACL-DEV-MGMT, NACL-DEV-APP, and NACL-DMZ-SAP-Router. Each network ACL is associated with a subnet, as shown in Figure 3. By default, a network ACL denies all access ("deny by default"). If you need to enable communication across network ACLs, add ACL rules to allow required access ("minimum permission").
Network ACL NACL-DEV-MGMT is associated with the subnet for the DEV-management zone in the development and test environment. Configure rules of network ACL NACL-DEV-MGMT to allow access to management ports (such as port 22) of servers in other zones through the bastion host in the management zone and deny access from other zones to the bastion host in the management zone.
IP addresses and ports in this section are only used as examples. If there are other management ports, you can add ACL rules as required. This section describes only access control policies for the development and test environment.
|
Rule |
Destination IP Address |
Protocol |
Destination Port |
Allow or Deny |
Description |
|---|---|---|---|---|---|
|
For the DEV-DMZ zone |
172.22.3.0/24 |
TCP |
22 |
Allow |
Allows the bastion host in the management zone in the development and test environment to access the SSH ports of servers in the DEV-DMZ zone. |
|
For the DEV-application zone |
172.22.4.0/24 |
TCP |
22 |
Allow |
Allows the bastion host in the management zone in the development and test environment to access the SSH ports of servers in the DEV-application zone. |
|
For the DMZ-SAP-DB zone |
172.22.5.0/24 |
TCP |
22 |
Allow |
Allows the bastion host in the management zone in the development and test environment to access the SSH ports of servers in the DEV-SAP-DB zone. |
|
For the DEV&PRD SAP router |
172.22.1.0/24 |
TCP |
22 |
Allow |
Allows the bastion host in the management zone in the development and test environment to access the SSH port of the DEV&PRD-SAP-Router server. |
|
* |
0.0.0.0/0 |
Any |
Any |
Deny |
Denies all outbound traffic that is not processed based on preset rules. |
|
Rule |
Source IP Address |
Protocol |
Destination Port |
Allow or Deny |
Description |
|---|---|---|---|---|---|
|
* |
0.0.0.0/0 |
Any |
Any |
Deny |
Denies all inbound traffic that is not processed based on preset rules. |
Network ACL NACL-DEV-APP is associated with the subnets for the DEV-DMZ, DEV-application, and DEV-SAP-DB zones. Configure inbound rules of network ACL NACL-DEV-APP to allow access to management ports (such as port 22) of servers in the zones through the bastion host in the management zone and allow access to service ports of servers in the zones through the SAP router.
|
Rule |
Destination IP Address |
Protocol |
Destination Port |
Allow or Deny |
Description |
|---|---|---|---|---|---|
|
* |
0.0.0.0/0 |
Any |
Any |
Deny |
Denies all outbound traffic that is not processed based on preset rules. |
|
Rule |
Source IP Address |
Protocol |
Destination Port |
Allow or Deny |
Description |
|---|---|---|---|---|---|
|
For the DEV-management zone |
172.22.2.0/24 |
TCP |
22 |
Allow |
Allows the bastion host in the management zone in the development and test environment to access the SSH ports of servers in the zone. |
|
For the DEV&PRD SAP router |
172.22.1.0/24 |
TCP |
234 |
Allow |
Allows the SAP-Router server to access service port 234 of servers in the DEV-application zone. |
|
For the DEV&PRD SAP router |
172.22.1.0/24 |
TCP |
345 |
Allow |
Allows the SAP-Router server to access service port 345 of servers in the DEV-SAP-DB zone. |
|
* |
0.0.0.0/0 |
Any |
Any |
Deny |
Denies all inbound traffic that is not processed based on preset rules. |
Network ACL NACL-DMZ-SAP-Router is associated with the subnet for the DEV&PRD-SAP router. Configure inbound rules of network ACL NACL-DMZ-SAP-Router to allow access to management ports (such as port 22) of servers in the zone through the bastion host in the management zone. Configure outbound rules of network ACL NACL-DMZ-SAP-Router to allow access to specified service ports in the application zone and SAP-DB zone in the development and test environment through the SAP router.
|
Rule |
Destination IP Address |
Protocol |
Destination Port |
Allow or Deny |
Description |
|---|---|---|---|---|---|
|
For the DEV-application zone |
172.22.4.0/24 |
TCP |
234 |
Allow |
Allows the SAP-Router server to access service port 234 of servers in the DEV-application zone. |
|
For the DEV-SAP-DB zone |
172.22.5.0/24 |
TCP |
345 |
Allow |
Allows the SAP-Router server to access service port 345 of servers in the DEV-SAP-DB zone. |
|
* |
0.0.0.0/0 |
Any |
Any |
Deny |
Denies all inbound traffic that is not processed based on preset rules. |
|
Rule |
Source IP Address |
Protocol |
Destination Port |
Allow or Deny |
Description |
|---|---|---|---|---|---|
|
For the DEV-management zone |
172.22.2.0/24 |
TCP |
22 |
Allow |
Allows the bastion host in the management zone in the development and test environment to access the SSH ports of servers in the zone. |
|
* |
0.0.0.0/0 |
Any |
Any |
Deny |
Denies all inbound traffic that is not processed based on preset rules. |
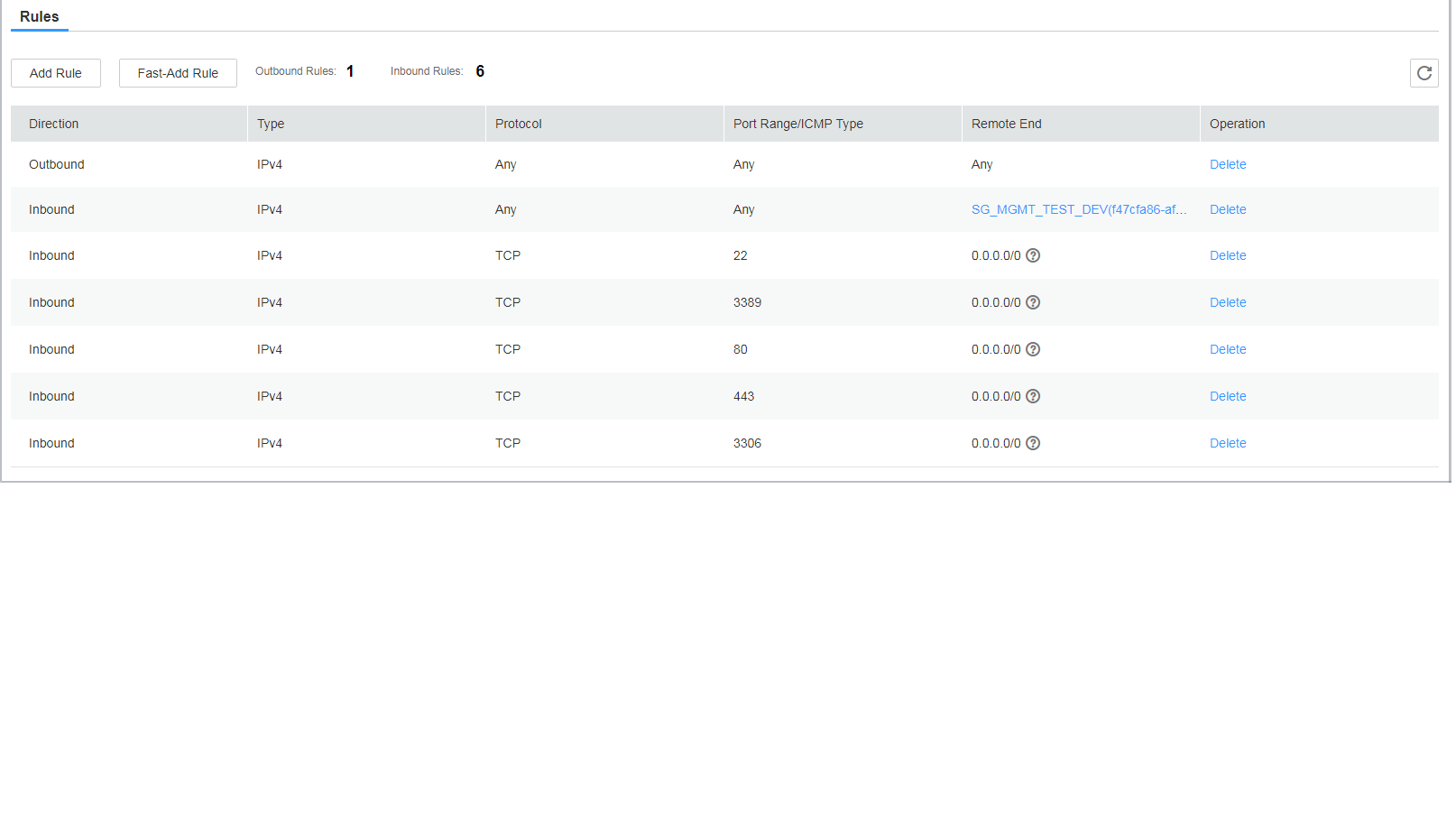
Security groups, such as SG_DEV_MGMT and SG_DEV_DB (which do not interact with the public network), are associated with ECSs in the subnets in the development and test environment. The security groups must be configured according to the "minimum permission" principle so that a minimum number of ECS ports are opened. Figure 4 shows an example for configuring the security groups. You need to configure them based on your own ports. Network ACLs are used for IP address access control. Other security groups in the development and test environment (for details, see Figure 1) that do not interact with the public network can be configured similarly.
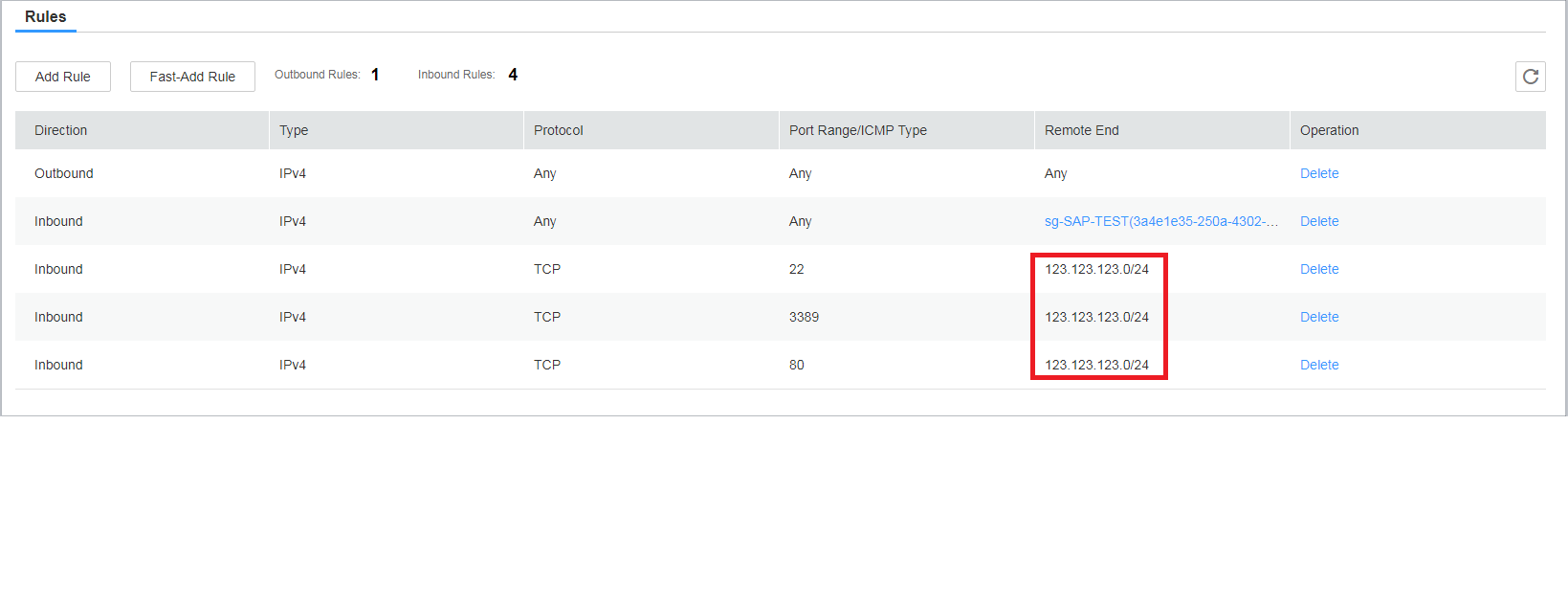
Security groups, such as SG_DEV_SRM, SG_DEV_Hybrids, and SG_SAP_ROUTER (which interact with the public network), are associated with ECSs in the subnets in the development and test environment. The security groups must be configured according to the "minimum permission" principle so that a minimum number of ECS ports and source IP addresses are opened. If the public IP address is fixed, you can refer to Figure 5 for configuring the security groups. You need to configure them based on your own ports.
If the public IP address is not fixed, you can create a security group rule to allow access from a specified public source IP address to meet your service requirements (such as the simulation test or technical support) and then delete the rule when it is not required.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot