Applying for a Private Certificate
After you create and activate a private CA, you can apply for private certificates from the private CA and use them for identity authentication, data encryption, and data decryption of internal applications.
This topic walks you through how to apply for a private certificate. You can apply for a maximum of 100,000 certificates.
Prerequisites
You have purchased and activated a private CA. For details, see Purchasing a Private CA and Activating a Private CA.
Procedure
- Log in to the CCM console.
- In the navigation pane on the left, choose .
- In the upper right corner of the private certificate list, click Apply for Certificate.
Figure 1 System generated CSR
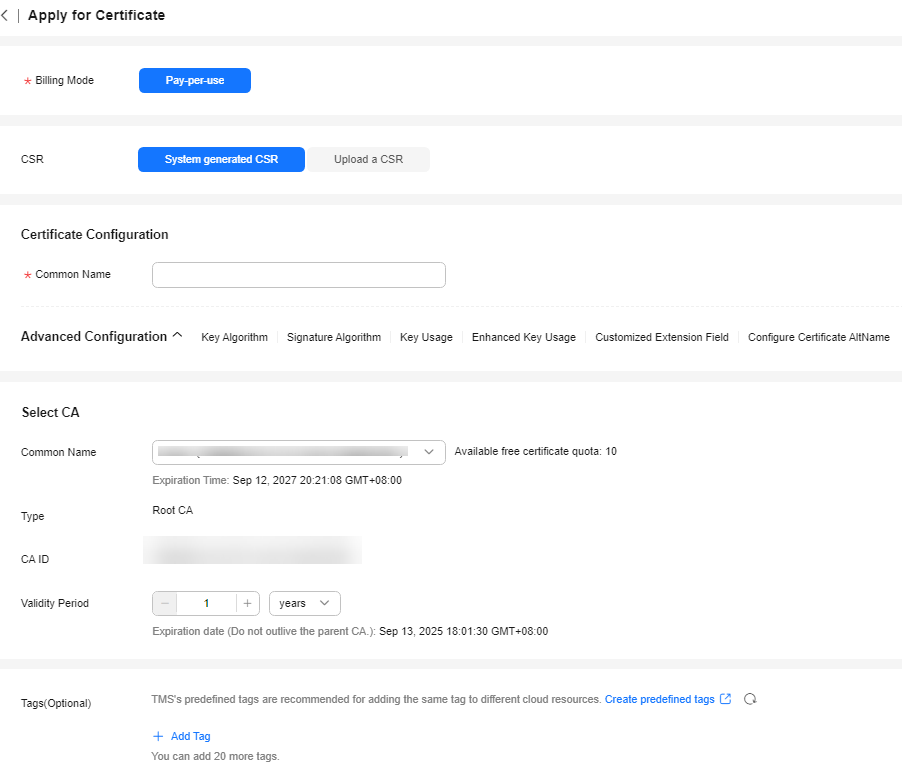 Figure 2 Upload a CSR
Figure 2 Upload a CSR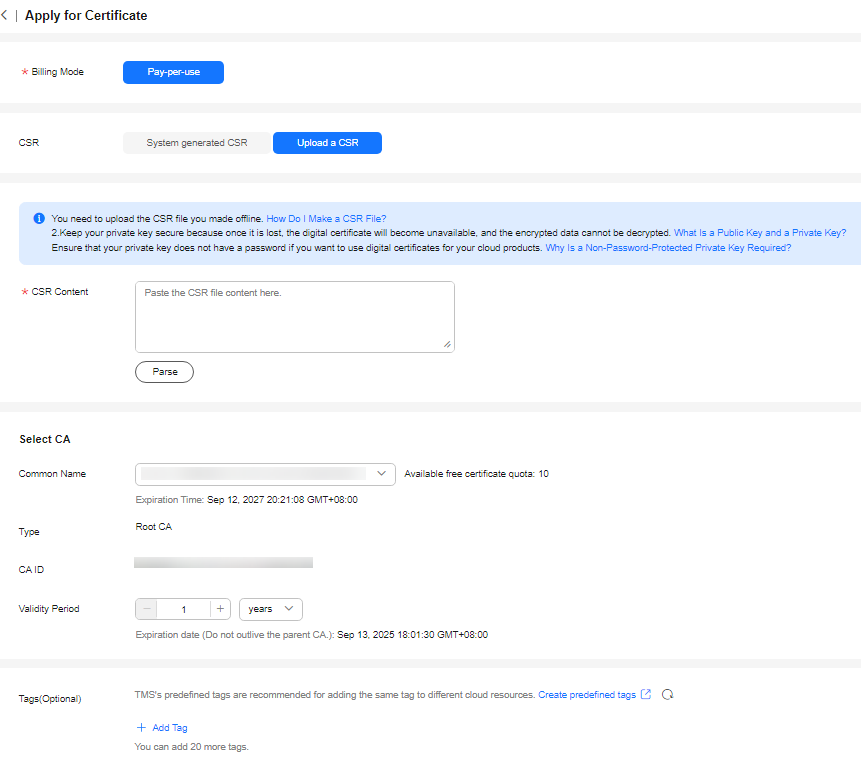
- Select the CSR file generation method.
Table 1 Certificate signing request (CSR) Parameter
Description
System generated CSR
The system automatically generates a certificate private key. Once the certificate is issued, you can download your certificate and private key on the certificate management page.
Upload a CSR
You can use an existing CSR. The procedure is as follows:
- You need to manually generate a CSR file and paste the content of the CSR file into the text box.
- Click Parse.
NOTICE:- To obtain a certificate, a CSR file needs to be submitted to the CA for review. A CSR file contains a public key and a distinguished name (DN). Typically, a CSR file is generated by a web server, and a pair of public and private keys are created along with the CSR file.
- You are advised to select System generated CSR to avoid approval failure caused by incorrect content.
- A private key file will be generated when the CSR file is generated manually. Keep and back up your private key properly. A private key maps to a certificate. If a private key is lost, the corresponding certificate becomes invalid. Huawei Cloud is not responsible for keeping your private key. You need to purchase a new certificate if the private key is lost.
- CCM has strict requirements on the key length of a CSR file. The key length must be 2,048 bits and the key type must be RSA.
- Configure certificate details.
Perform this step only when you select System generated CSR for CSR.
Common Name: You can customize the name of the private certificate.
- Click
 on the right of Advanced Configuration.
on the right of Advanced Configuration.
Perform this step only when you select System generated CSR for CSR.
Table 2 Advanced settings Parameter
Description
Example Value
Key Algorithm
Key Algorithm: Select the key algorithm and key size for the private certificate.
The value can be RSA2048, RSA4096, EC256, or EC384.
RSA2048
Signature Algorithm
Select the signature hash algorithm for the private certificate.
The value can be SHA256, SHA384, or SHA512.
SHA256
Key Usage
Select the key usage of the certificate. You can select more than one option.
- digitalSignature: The key is used as a digital signature.
- nonRepudiation: The key can be used for non-repudiation.
- keyEncipherment: The key can be used for key encryption.
- dataEncipherment: The key can be used for data encryption.
- keyAgreement: The key can be used as a key-agreement protocol.
- keyCertSign: The key can be used to issue certificates.
- cRLSign: The key can be used for signing blacklists.
- encipherOnly: The key can be used for encryption only.
- decipherOnly: The key can be used for decryption only.
digitalSignature
Enhanced Key Usage
Select the enhanced key usage for the certificate. You can select more than one option.
- Server identity authentication
- Client identity authentication
- Code signature
- Secure email
- Timestamp
- Smart card login
Server identity authentication
Customized Extension Field
Enter customized information of the certificate.
None
Configure Certificate AltName
This field is optional. If you want to use the private certificate to multiple subjects, you can add more AltName records.
You can configure IP address, DNS, Email, URI, or UPN for AltName. When you configure AltName, enter the value according to the value type you select.
- IP address: Enter an IP address.
- DNS: Enter the domain name.
- Email: Enter an email address.
- URI: Enter the network address.
- UPN: user principal name
A maximum of 20 AltName records can be configured.
None
- Select a CA.
Table 3 Parameters for selecting a CA Parameter
Description
Common Name
Select a common name of the private CA you want.
Type
The CA type is autofilled after you specify Common Name.
CA ID
The CA ID is autofilled after you specify Common Name.
Validity Period
Configure the validity period of the private certificate.
NOTE:- You can customize the validity period of a private certificate. The validity period cannot outlive the validity period of the activated private CA.
- A private CA can be valid for up to 30 years.
- Select the CSR file generation method.
- (Optional) Tags: Add a tag to the purchased certificate. For details, see Creating a Tag.
- Confirm the information and click OK.
After you submit your application, the system will return to the private certificate list page. Message "Certificate xxx applied for successfully." is displayed in the upper right corner of the page, indicating that the private certificate application is successful.
Follow-up Operations
When a private certificate is issued, you can download it and distribute it to the certificate subject for installation. For details, see Downloading a Private Certificate.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





