Protected Objects
Does EdgeSec Support Application Layer Protocol- and Content-Based Access Control?
EdgeSec supports access control over content at the application layer. HTTP and HTTPS are both application layer protocols.
Can EdgeSec Defend Against XOR Injection Attacks?
Yes. EdgeSec can defend against XOR injection attacks.
Does EdgeSec Support Vulnerability Detection?
EdgeSec enables anti-crawler rules to detect and block threats such as third-party security tool vulnerability attacks. If you enable the scanner item when configuring anti-crawler rules, EdgeSec detects scanners and crawlers, such as OpenVAS and Nmap.
For details, see Configuring Anti-Crawler Rules.
Can EdgeSec Check the Body I Add to a POST Request?
The built-in detection of EdgeSec checks POST data, and web shells are the files submitted in POST requests. EdgeSec checks all data, such as forms and JSON files in POST requests based on the default protection policies.
You can configure a precise protection rule to check the body added to POST requests. For details, see Configuring a Precise Protection Rule.
Can EdgeSec Limit the Access Speed of a Domain Name?
No.
However, you can customize a CC attack protection rule to restrict access to a specific URL on your website based on an IP address, mitigating CC attacks.
For details, see Configuring a CC Attack Protection Rule.
Can EdgeSec Block URL Requests That Contain Special Characters?
No. EdgeSec can detect and restrict source IP addresses.
Can EdgeSec Block Requests for Calling Other APIs from Web Pages?
There are two cases:
- If the request data for calling other APIs on the web page is included in the domain names protected by EdgeSec, the request data passes through EdgeSec. EdgeSec checks the request data and blocks it if it is an attack.
- If the request data for calling other APIs on the web page is not included in the domain names protected by EdgeSec, the request data does not pass through EdgeSec. EdgeSec cannot block the request data.
Does EdgeSec Block Customized POST Requests?
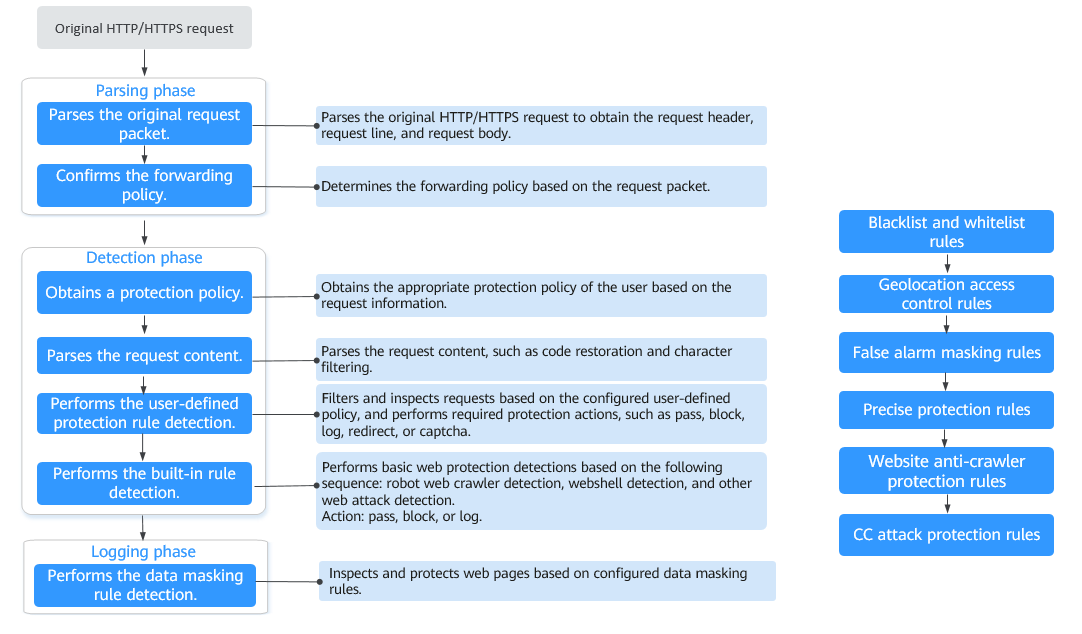
No. EdgeSec does not block user-defined POST requests. Figure 1 shows the detection process of the EdgeSec built-in protection rules for original HTTP/HTTPS requests.
For details about the EdgeSec protection process, see Configuration Guidance.
Does EdgeSec Support the CORS-Denied Policy?
No. EdgeSec does not support the configuration of a protection rule that denies Cross-Origin Resource Sharing (CORS) requests. For details about features of EdgeSec, see Functions.
Can EdgeSec Limit Access Through Domain Names?
No.
EdgeSec supports the blacklist and whitelist rules to block or log only access requests from specified IP addresses or IP address segments. For details, see Configuring an IP Address Blacklist or Whitelist Rule.
Does EdgeSec Have the IPS Module?
Unlike the traditional firewalls, EdgeSec does not have an Intrusion Prevention System (IPS). EdgeSec supports intrusion detection of only HTTP/HTTPS requests.
Is EdgeSec a Hardware Firewall or a Software Firewall?
EdgeSec is a software firewall. After purchasing EdgeSec, you only need to connect your domain name to use EdgeSec to protect your web applications.
For details, see Adding a Website.
Can EdgeSec Defend Against the Apache Struts2 Remote Code Execution Vulnerability (CVE-2021-31805)?
Yes. EdgeSec basic web protection rules can defend against the Apache Struts2 remote code execution vulnerability (CVE-2021-31805).
For details, see Configuring Basic Web Protection Rules.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot