Auto Handling of HSS Rootkit Attacks (Automated handling of host Rootkit event attacks)
Playbook Overview
The Automated handling of host Rootkit event attacks playbook has been matched with the Host Isolation - Malware workflow. This playbook automatically adds the host that triggers the alert whose Alarm Type is Rootkit to a VPC security group, and SecMaster automatically blocks the outbound (access from the host to third parties) and inbound (access from third parties to the host) access and closes the alert at the same time.
Trigger condition: The alert source is HSS, and the alert type is Rootkits.
You need to enable this playbook for it to take effect.
Prerequisites
- Your SecMaster professional edition is available.
- The HSS alarm log has been connected to SecMaster, and the Auto Alert Conversion button has been toggled on. For details about how to connect logs to SecMaster, see Enabling Log Access.
- You have created a model using the built-in host rootkit event template and enabled the model. For details about how to create and enable a model, see Creating an Alert Model Using a Preconfigured Model Template and Managing Models, respectively.
Procedure
- Log in to the SecMaster console.
- In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 1 Workspace management page

- In the navigation pane on the left, choose Security Orchestration > Playbooks. Figure 2 Accessing the Playbooks tab
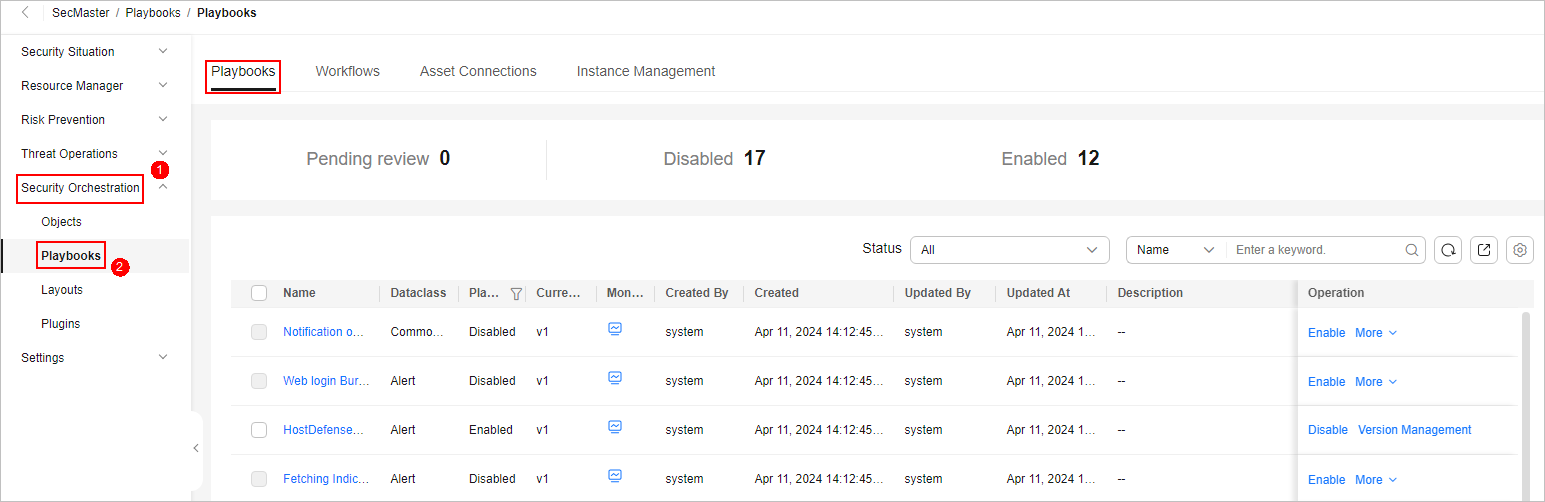
- On the Playbooks page, search for the Automated handling of host Rootkit event attacks playbook and click Enable in the Operation column of the Automated handling of host Rootkit event attacks playbook.
- In the dialog box displayed, select the initial playbook version v1 and click OK. If the Playbook Status of the Automated handling of host Rootkit event attacks playbook changes to Enabled, the playbook has been enabled successfully.
Implementation Effect
This playbook automatically adds the host that triggers the alert whose Alarm Type is Rootkit to a VPC security group, and SecMaster automatically blocks the outbound (access from the host to third parties) and inbound (access from third parties to the host) access. The playbook will automatically close the alert at the same time.
- If the playbook detects an HSS alert whose Alarm Type is Rootkit, the playbook generates a to-do task for automatically isolating the host that triggered the alert. In the navigation pane on the left of the SecMaster workspace, choose . On the To-Dos page, you can view the task whose name is Review Server Isolation and the Associated Object is Automated handling of host Rootkit event attacks.

- On the To-Dos page, locate the task whose name is Review Server Isolation and Associated Object is Automated handling of host Rootkit event attacks and click Review in the Operation column. On the Playbook - Node Review pane displayed on the right, select Continue.
- If the isolation is approved, SecMaster automatically adds the host to the VPC security group. SecMaster automatically blocks the outbound (host access to third parties) and inbound (third parties access to the host) access. You can view the security group named SecMaster_One-Click_Host_Isolation in the VPC service. For details about how to view a security group, see Viewing a Security Group. Figure 4 SecMaster_One-Click Server Isolation security group

Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





