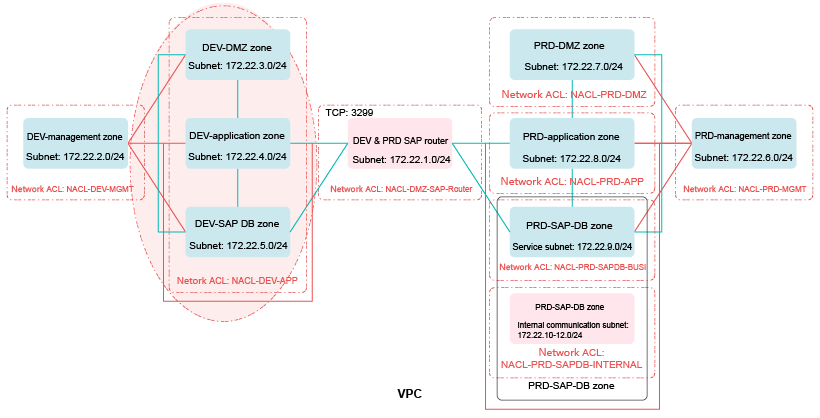
Border Between the Development and Test Environment and the Production Environment
The development and test environment has a low security level and a high security risk. If you need to connect the development and test environment to the production environment, configure strict access control policies for this border. Use the access control policies to strictly control ("deny by default") access from the development and test environment to the production environment, allowing access to only required IP addresses and ports ("minimum permission") in the production environment. You can configure relatively loose access control policies for the access from the production environment to the development and test environment.
Security Policies
As shown in Figure 1, network ACL NACL-DEV-APP is associated with the subnet for the DEV-application zone. Configure outbound rules of network ACL NACL-DEV-APP to strictly control access to the production environment according to the "minimum permission" principle, allowing access to only specified IP addresses and ports in the production environment. You can configure relatively loose inbound rules for access from the production environment.
Stronger, securer, and complexer ACL rules mean higher deployment and configuration and O&M costs. You can use looser ACL rules based on your actual enterprise requirements.
Access control policies for the border between the development and test environment and the production environment are mainly those for communication with the PRD-DMZ, PRD-application, and PRD-DB zones in the production environment. For details, see Table 1 and Table 2.
IP addresses and ports in this section are only used as examples. If there are other services, you can add ACL rules as required. This section describes only access control policies for the border between the development and test environment and the production environment.
|
Rule |
Destination IP Address |
Protocol |
Destination Port |
Allow or Deny |
Description |
|---|---|---|---|---|---|
|
For the PRD-DMZ zone |
172.22.7.0/24 |
TCP |
1433 |
Allow |
Allows VMs in the subnet in the development and test environment to access port 1433 of servers in the PRD-DMZ zone in the production environment for software and codes update pushing. |
|
For the PRD-application zone |
172.22.8.0/24 |
TCP |
2433 |
Allow |
Allows VMs in the subnet in the development and test environment to access port 2433 of servers in the PRD-application zone in the production environment for software and codes update pushing. |
|
For the PRD-DB zone |
172.22.9.0/24 |
TCP |
3443 |
Allow |
Allows VMs in the subnet in the development and test environment to access port 3443 of servers in the PRD-DB zone in the production environment for software and codes update pushing. |
|
* |
0.0.0.0/0 |
Any |
Any |
Deny |
Denies all Outbound traffic that is not processed based on preset rules. |
|
Rule |
Source IP Address |
Protocol |
Destination Port |
Allow or Deny |
Description |
|---|---|---|---|---|---|
|
For the PRD-DMZ zone |
172.22.7.0/24 |
TCP |
Any |
Allow |
Allows VMs in the PRD-DMZ zone in the production environment to access any TCP port of servers in the DEV-DMZ, DEV-application, and DEV-SAP-DB zones. |
|
For the PRD-application zone |
172.22.8.0/24 |
TCP |
Any |
Allow |
Allows VMs in the PRD-application zone in the production environment to access any TCP port of servers in the DEV-DMZ, DEV-application, and DEV-SAP-DB zones. |
|
For the PRD-DB zone |
172.22.9.0/24 |
TCP |
Any |
Allow |
Allows VMs in the PRD-DB zone in the production environment to access any TCP port of servers in the DEV-DMZ, DEV-application, and DEV-SAP-DB zones. |
|
* |
0.0.0.0/0 |
Any |
Any |
Deny |
Denies all outbound traffic that is not processed using preset fixed rules. |
For security group rule configuration, see the related content in Network Isolation and Access Control.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot