Activating a Dedicated HSM Instance
You need to activate a Dedicated HSM instance before using it. The yearly or monthly package will be charged during activation.
This section describes how to activate a Dedicated HSM instance through the management console.
Prerequisites
The status of the Dedicated HSM instance is To be activated.
Constraints
- The instance name can contain only letters, digits, underscores (_), and hyphens (-).
- Two nodes are created as the background resource pool for a Dedicated HSM instance. To ensure high availability of the nodes, a floating IP address is assigned to the instance.
- If the instance fails to be created, you can locate the target instance and click Delete. Then apply for a refund by submitting a service ticket.
- After a Dedicated HSM instance is successfully created, it cannot be changed to another type. To use a Dedicated HSM instance of another type, you need to buy another one.
Procedure
- Log in to the DEW console.
- Click
 in the upper left corner and select a region or project.
in the upper left corner and select a region or project. - In the navigation pane on the left, choose Dedicated HSM > Instances.
- Locate the target instance and click Activate in the Operation column.
- Select an AZ. Figure 1 Selecting an AZ

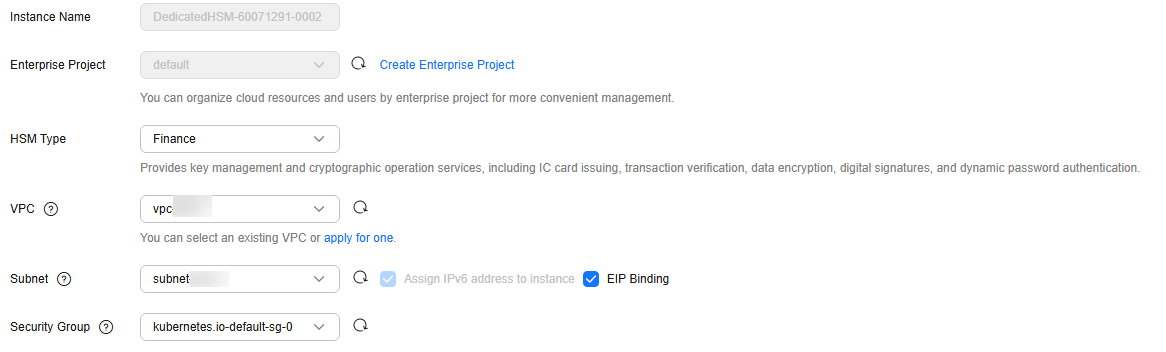
- Enter activation information, as shown in Figure 2. Table 1 describes the parameters.
Table 1 Parameter description Parameter
Description
Example Value
Instance Name
Name of a Dedicated HSM instance
NOTE:The instance name can contain only letters, digits, underscores (_), and hyphens (-).
DedicatedHSM-3c98-0002
Enterprise Project
Enterprise project that the dedicated HSM is to be bound to
default
HSM Type
Available HSM types include Finance, Server, and Signature server.
- Finance: Provides key management and encryption computing services, including IC card issuing, transaction verification, data encryption, digital signatures, and dynamic password authentication.
- Server: Provides secure, complete key management services and high-performance concurrent cryptographic operations, such as data signatures, signature verification, and data encryption/decryption.
- Signature server: Guarantees the integrity, confidentiality, anti-repudiation, and post-event traceability of user data by using digital signatures, digital envelopes, and digital digests.
Finance
VPC
You can select an existing Virtual Private Cloud (VPC), or click Apply for VPC to create one.
For more information about VPC, see the Virtual Private Cloud User Guide.
vpc-test-dhsm
Subnet
All available subnets are displayed on the page. The system automatically assigns three IP address to the instance. For more information about subnets, see the Virtual Private Cloud User Guide.
NOTE:Two nodes are created as the background resource pool for a Dedicated HSM instance. To ensure high availability of the nodes, a floating IP address is assigned to the instance.
subnet-test-dhsm (192.168.0.0/24)
EIP Binding
After this parameter is enabled, you can bind an EIP to the Dedicated HSM instance to enable public access to the instance.
-
Security Group
The security group configured for the instance is displayed on the page. Once a security group is selected for an instance, the instance is protected by the security group access rules.
For more information about security groups, see the Virtual Private Cloud User Guide.
WorkspaceUserSecurityGroup
- If you have purchased a Dedicated HSM instance in standard edition:
Click Create Now to return to the Dedicated HSM instance list. You can view information about the activated instance.
If the status of the Dedicated HSM instance is Creating, the instance is successfully activated.
- If you have purchased a Dedicated HSM instance in platinum edition:
- Set the required duration.
The required duration ranges from one month to one year.
The Auto-renew option enables the system to renew your service by the purchased period when the service is about to expire.
- Confirm the configuration and click Next.
For any doubt about the pricing, click Pricing details.
- On the Order Details page, confirm the order details, read and select I have read and agree to the Privacy Policy Statement.
- Click Pay Now to pay for the yearly or monthly package.
- On the Pay page, select a payment method to pay for your order.
After successful payment, you can view the information about the HSM instance on the HSM instance list page.
If the Status of the instance is Creating, the instance has been activated and is being allocated to you. It will be available in 5 to 10 minutes.
Creating: The system is allocating an instance to you. This process usually lasts for 5 to 10 minutes.
After the assignment, the instance status may change to either of the following:- Creation failed: An instance fails to be created due to insufficient resources or network faults.
If the instance fails to be created, you can locate the instance, and click Delete. Then apply for a refund by submitting a service ticket.
- Running: An instance has been successfully assigned to you and is running properly.
After a Dedicated HSM instance is successfully created, it can neither be changed to another type nor be refunded. To use a Dedicated HSM instance of another type, you need to buy another one.
- Creation failed: An instance fails to be created due to insufficient resources or network faults.
- Set the required duration.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot