Creating Identification Rule Groups
A sensitive data identification rule group has service logic and contains scattered rules. A rule group is the prerequisite for running a sensitive data discovery task.
Prerequisites
Identification rules have been created. For details, see Creating Identification Rules (Some Advanced Features).
Constraints
- During sensitive data identification, if a field matches multiple identification rules in an identification rule group, the highest security level of the identification rules is used as the security level of the field, and multiple field classifications are allowed.
- A maximum of 100 identification rule groups can be created.
- Data identification rule groups that are referenced can be deleted only if the reference is canceled.
Creating a Sensitive Data Identification Rule Group
- On the DataArts Studio console, locate a workspace and click DataArts Security.
- In the navigation pane on the left, choose Sensitive Data Identification > Data Identification Rules.
- Click the Rule Groups tab in the upper part of the displayed page. Figure 1 Creating a sensitive data identification rule group

- Click Create, set the group name and description based on Table 1, select identification rules, and click OK. Figure 2 Parameters for creating an identification rule group
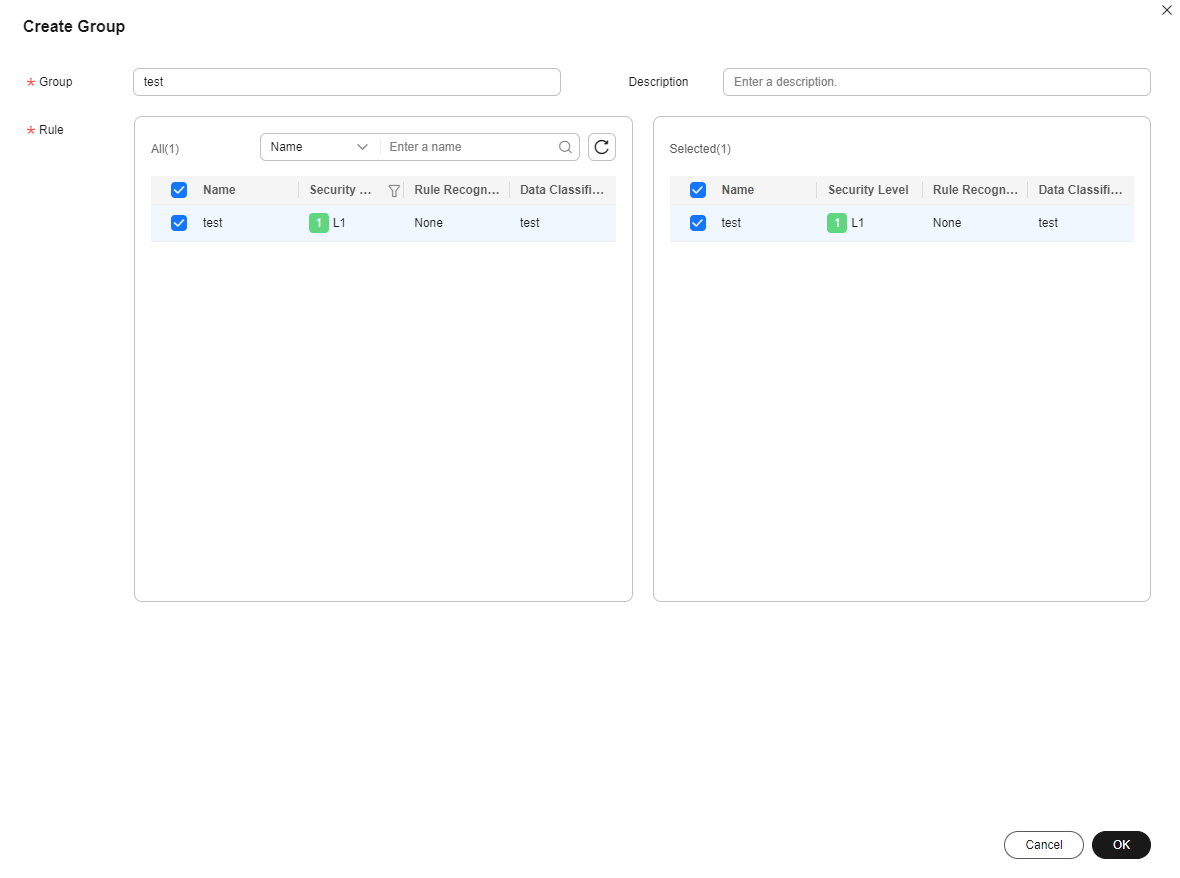
The selected rules are displayed in the list on the right. You can click to deselect the selected rules.
Table 1 Parameters Parameter
Description
*Group
Group names can include only letters, numbers, and underscores (_).
You are advised to include the rule group meaning into the name and avoid meaningless descriptions so that the rule group can be quickly located and selected.
Description
Information to better identify the group
Related Operations
- Editing a rule group: On the Rule Groups page, locate a group and click Edit in the Operation column to change the name, description, and rules of the group.
- Deleting a rule group: On the Rule Groups page, locate a group and click Delete in the Operation column. To delete rule groups in a batch, select them and click Delete above the list.

- Data identification rule groups that are referenced can be deleted only if the reference is canceled.
- The deletion operation cannot be undone. Exercise caution when performing this operation.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





