COA Plugin
Function Description
The COA plugin is built in SecMaster. It can call CloudTIC, Huawei Cloud built-in intelligence center, to verify threat indicators. Each built-in plugin has a corresponding operation connection.
Viewing COA Plugin Details and Operation Connections
- Log in to the SecMaster console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 1 Workspace management page

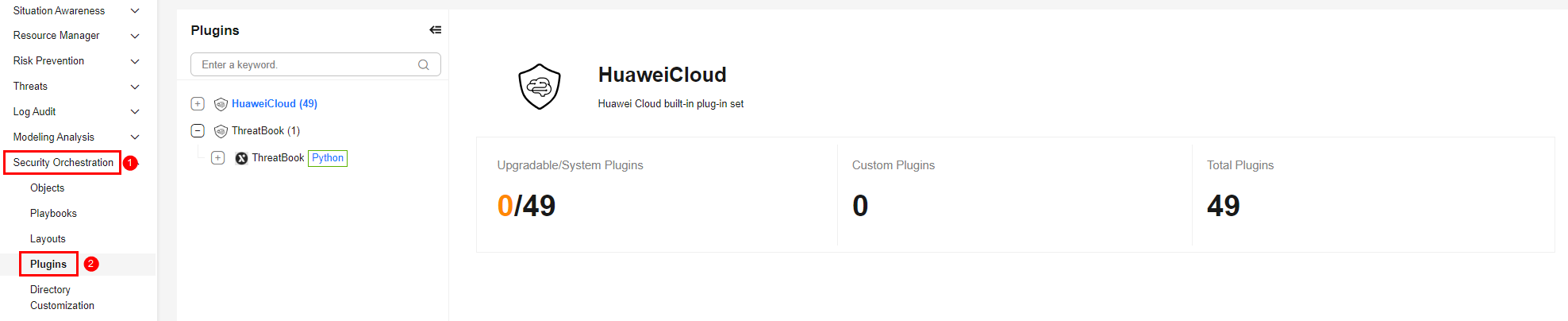
- In the navigation pane on the left, choose . Figure 2 Plugins page
- On the Plugins page, select the COA plugin under the Huawei Cloud catalog. The Details tab is displayed by default. The Details tab displays the login credential information of the operation connection associated with the plugin.
- Click the Operation Connections tab of the COA plugin. On the displayed page, you can view information about the operation connections associated with the COA plugin.
- For details about how to edit or delete an operation connection, see Editing an Operation Connection and Deleting an Operation Connection. For details about how to add an operation connection for the COA plugin, see Creating an Operation Connection. A plugin can have multiple operation connections.
Parameter intelligence of the Plug-in Execution Function
Function: Calls CloudTIC to verify threat indicators.
| Parameter | Parameter Type | Parameter Description | Mandatory |
|---|---|---|---|
| type | String | Data type of the threat indicator object. Value range: Only ip, domain, url, and file are supported. Uppercase letters and other values are not supported. | Yes |
| data | String | Value of the query object, which corresponds to type.
| Yes |
| exclude | String | You can exclude specified parameters from the returned threat intelligence query result based on the actual application scenario. If multiple parameters need to be excluded, separate them with commas (,). No space is allowed. | No |
| field | String | This parameter takes effect only when type is set to file. This parameter specifies the file field to be queried. | No |
| language | String | Response language of the query result. The value can be zh or en. Uppercase letters and other values are not supported. zh indicates that the query result is displayed in simplified Chinese. en indicates that the query result is displayed in English. | No |
| Parameter | Parameter Type | Parameter Description |
|---|---|---|
| header | Object | Header of the response returned after threat intelligence information is queried, including basic information about the request and response, such as the request time, response service, and request ID. |
| code | Int | Status code, which indicates whether the request is successful. code value description:
|
| body | Object | Detailed information about the indicator, which is returned by the interface. |
Output Example of the intelligence Function
{
"headers": {
"Transfer-Encoding": "chunked",
"X-Frame-Options": "SAMEORIGIN",
"Strict-Transport-Security": "max-age=31536000; includeSubdomains;",
"Cache-Control": "no-cache, no-store, max-age=0, must-revalidate",
"Server": "api-gateway",
"X-Request-Id": "9262f8cb6bc542583288f9da5c486b68",
"X-Content-Type-Options": "nosniff",
"Connection": "keep-alive",
"X-Download-Options": "noopen",
"X-XSS-Protection": "1; mode=block;",
"Date": "Sun, 04 Jan 2026 06:40:17 GMT",
"Content-Type": "application/json"
},
"code": 200,
"body": {
"indicator": {
"severity": "info",
"pattern_type": "STIX",
"created": "2025-12-09T06:17:42+08:00",
"confidence": 75,
"pattern": "[ipv4-addr:value = '8.8.8.8']",
"pattern_version": "2.1",
"description": "",
"valid_from": null,
"source": "ThreatBook Labs",
"revoked": false,
"labels": ["Gateway", "Whitelist", "CDN", "GoogleCloud"],
"extensions": "",
"valid_until": null,
"verdict": "white",
"defanged": false,
"name": "8.8.8.8",
"modified": "2025-12-30T05:49:44+08:00",
"kill_chain_phases": [],
"suggested_of_coa": "",
"value": "",
"external_references": []
},
"rdns_list": [{
"severity": null,
"update_time": "2023-11-22 00:00:00",
"first_time": "2023-11-22 00:00:00",
"domain": "dns.google",
"labels": null
}],
"ip": "8.8.8.8",
"r_dns_count": 1,
"ports": [],
"certs": [],
"samples": [{
"severity": "",
"sha256": "766c9a7d7dda6fadde2b6a53e799e684a7fa6ca4283211bb82ee6d9186b8e1d6",
"size": -1,
"file_type": "",
"scan_time": "2021-12-16 05:25:33",
"malware_type": "Exploit",
"ratio": "17/26",
"labels": [],
"malware_family": "RpcDcom"
}, {
"severity": "",
"sha256": "f4c11cd3f6839a2dcc0116096ddc0e4b88663d77cc01cc6950346229feaec19a",
"size": -1,
"file_type": "",
"scan_time": "2021-12-16 05:01:43",
"malware_type": "Exploit",
"ratio": "15/26",
"labels": [],
"malware_family": "RpcDcom"
}, {
"severity": "",
"sha256": "fead0503da6a6e4485145934796477fad833c5d5b09931820f2409f765131262",
"size": -1,
"file_type": "",
"scan_time": "2021-12-15 21:57:14",
"malware_type": "Exploit",
"ratio": "15/26",
"labels": [],
"malware_family": "RpcDcom"
}, {
"severity": "",
"sha256": "640ce798beefff6623b30c249dd326f8c2b610617dd8899e7413a5cf89c417e9",
"size": -1,
"file_type": "",
"scan_time": "2021-12-15 20:40:59",
"malware_type": "Trojan",
"ratio": "7/26",
"labels": [],
"malware_family": "ArkeiStealer"
}, {
"severity": "",
"sha256": "113731e6949d9073227f3e90634fe990f2e6c65bb365d7d8d573f9b8a0aa7c41",
"size": -1,
"file_type": "",
"scan_time": "2021-12-15 15:45:50",
"malware_type": "TrojanDownloader",
"ratio": "12/26",
"labels": [],
"malware_family": "Upatre"
}, {
"severity": "",
"sha256": "efc3fd87e545269899893e663a3238489cf1420cfb468725fb8f9258218a1d8b",
"size": -1,
"file_type": "",
"scan_time": "2021-12-15 15:21:41",
"malware_type": "Exploit",
"ratio": "18/26",
"labels": [],
"malware_family": "RpcDcom"
}, {
"severity": "",
"sha256": "fc3e34af64170a6014390ae1f79b2b908ce3bd193c3961830dbca0abb50d721a",
"size": -1,
"file_type": "",
"scan_time": "2021-12-15 13:35:32",
"malware_type": "Exploit",
"ratio": "17/26",
"labels": [],
"malware_family": "RpcDcom"
}, {
"severity": "",
"sha256": "710bb81b2788e3b27ed3da4d267aca39c03aceedeb94bfb936554ae4c05d0fc3",
"size": -1,
"file_type": "",
"scan_time": "2021-12-15 12:24:59",
"malware_type": "Virus",
"ratio": "13/26",
"labels": [],
"malware_family": "Nabucur"
}, {
"severity": "",
"sha256": "773e1d44eb73384586f914b721a2477bf680015cb348ff2509c1e6f703aad0c7",
"size": -1,
"file_type": "",
"scan_time": "2021-12-15 07:04:24",
"malware_type": "Exploit",
"ratio": "13/26",
"labels": [],
"malware_family": "RpcDcom"
}, {
"severity": "",
"sha256": "ebf64359a67e9a5cc03a4e043be229d5f7592ecd73fecfbf84b37420871daee8",
"size": -1,
"file_type": "",
"scan_time": "2021-12-15 05:48:09",
"malware_type": "Trojan",
"ratio": "7/26",
"labels": [],
"malware_family": "Kryptik"
}, {
"severity": "",
"sha256": "4844e668a5365f661cb9d31108607d79aa3293ef7ba5809d86c0f25144f216e9",
"size": -1,
"file_type": "",
"scan_time": "2021-12-15 03:12:20",
"malware_type": "",
"ratio": "0/26",
"labels": [],
"malware_family": ""
}, {
"severity": "",
"sha256": "40be281fc46b001a18bc803e060cdfad6205af17f2d9159b1cd447b5548c4c54",
"size": -1,
"file_type": "",
"scan_time": "2021-12-15 00:10:12",
"malware_type": "Worm",
"ratio": "13/26",
"labels": [],
"malware_family": "Cambot"
}, {
"severity": "",
"sha256": "a82e711c4ac0b7c3623d6e051df24974d0da6d0c160900e45fdae72f6a324922",
"size": -1,
"file_type": "",
"scan_time": "2021-12-14 23:54:08",
"malware_type": "Exploit",
"ratio": "15/26",
"labels": [],
"malware_family": "RpcDcom"
}, {
"severity": "",
"sha256": "eff05ab783988a91d98193913f414dd4db67d6d0c00251316f6304922af3e956",
"size": -1,
"file_type": "",
"scan_time": "2021-12-14 23:43:57",
"malware_type": "Worm",
"ratio": "18/26",
"labels": [],
"malware_family": "Brontok"
}, {
"severity": "",
"sha256": "b56c8a9cedd802e7e7a2d2d3755884925c1ee83899dce4ca2f4f09fd45a770bc",
"size": -1,
"file_type": "",
"scan_time": "2019-03-08 00:24:07",
"malware_type": "Backdoor",
"ratio": "17/26",
"labels": [],
"malware_family": "Zegost"
}, {
"severity": "",
"sha256": "219f6a9e24bc885b6e7a1b36fb19c194e0c5f3f71130133058af90d178ee28e3",
"size": -1,
"file_type": "",
"scan_time": "2018-08-13 13:15:59",
"malware_type": "Backdoor",
"ratio": "19/26",
"labels": [],
"malware_family": "PcClient"
}, {
"severity": "",
"sha256": "bc07c1c35f4515705677abbe787e6d7b0c2413a147a4a02bc914d969ba7fd984",
"size": -1,
"file_type": "",
"scan_time": "2015-09-29 03:00:56",
"malware_type": "",
"ratio": "0/26",
"labels": [],
"malware_family": ""
}, {
"severity": "",
"sha256": "28f730de9f9aa6db670206c04e5b49135fab8d4d7a0577dfc345d6f7cdcddfb8",
"size": -1,
"file_type": "",
"scan_time": "2015-09-25 03:07:10",
"malware_type": "",
"ratio": "7/26",
"labels": [],
"malware_family": ""
}, {
"severity": "",
"sha256": "2a2309ae0b6205d00b00958ae57494d3bf17643e4565df5d4ef9738bfe0b9037",
"size": -1,
"file_type": "",
"scan_time": "2015-09-25 03:00:06",
"malware_type": "",
"ratio": "7/26",
"labels": [],
"malware_family": ""
}, {
"severity": "",
"sha256": "8e000438703c8d66d02ef8009c0ac4a787381d9ad3b72ef58eb8151adc9c6473",
"size": -1,
"file_type": "",
"scan_time": "2015-09-25 01:33:38",
"malware_type": "",
"ratio": "5/26",
"labels": [],
"malware_family": ""
}],
"incident_count": -1,
"p_dns_count": -1,
"hardware_platforms": "",
"location": {
"country": "United States",
"street_address": "",
"city": "",
"latitude": 39.765053,
"precision": 0,
"administrative_area": "",
"region": "",
"postal_code": "",
"longitude": -101.40791
},
"pdns_list": [],
"asn": {
"number": 15169,
"isp": "Google LLC",
"name": "GOOGLE",
"rank": "4",
"rir": ""
}
}
} Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





