Using CFW to Defend Against Worms
You can use CFW to defend against worm attacks.
Application Scenarios
Worms exploit network vulnerabilities and weak passwords to attack servers and spread rapidly through network connections, posing great security threats to user assets and services.
The CFW IPS rule library provides rules to effectively block attacks from worms, such as JS.FortNight.E-2 and the Lovgate worm netservices.exe.
What Is a Worm?
A worm is a type of malware that can replicate itself and spread over the network. It scans for vulnerabilities on the network and exploits these vulnerabilities to infect other servers. Worms can exist and run without depending on other programs.
Worms have the following characteristics:
- Vulnerability exploit: Worms usually exploit security vulnerabilities in OSs or applications to spread. If a system has vulnerabilities that have not been fixed by installing patches or update, the system may become a target of worms.
- Self-replication: Worms can replicate all or part of their own code and spread the replicas to other servers over the network. Self-replication is the basis for the rapid spread of worms.
- Independent transmission: Different from traditional viruses that require user interaction (for example, opening attachments) to start an attack, worms can independently search for and infect other vulnerable servers on the network without user intervention. Independent transmission makes worms more difficult to block.
Harms of Worms
Worms pose serious threats to network security, including but not limited to:
- System damage: Worms can damage system files and data, causing the system to crash or fail to work properly.
- Information theft: Worms can steal sensitive user information, such as passwords and bank account information.
- Abuse of network resources: Worms can use infected computers to launch DDoS attacks and send spam, causing network congestion and service unavailability.
- Malware spread: Worms can use infected computers to spread other malware, such as Trojans and spyware.
How to Defend Against Worms
To defend against worms, you can establish good security habits, disable or delete unnecessary services, periodically update systems and applications, use strong passwords and multiple authentication mechanisms, and periodically back up data. You can also use the CFW intrusion prevention function to block worm attacks.
- Log in to the CFW console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - (Optional) Switch to another firewall instance. Select a firewall from the drop-down list in the upper left corner of the page.
- In the navigation pane, choose .
- Click View Effective Rules under Basic Protection.
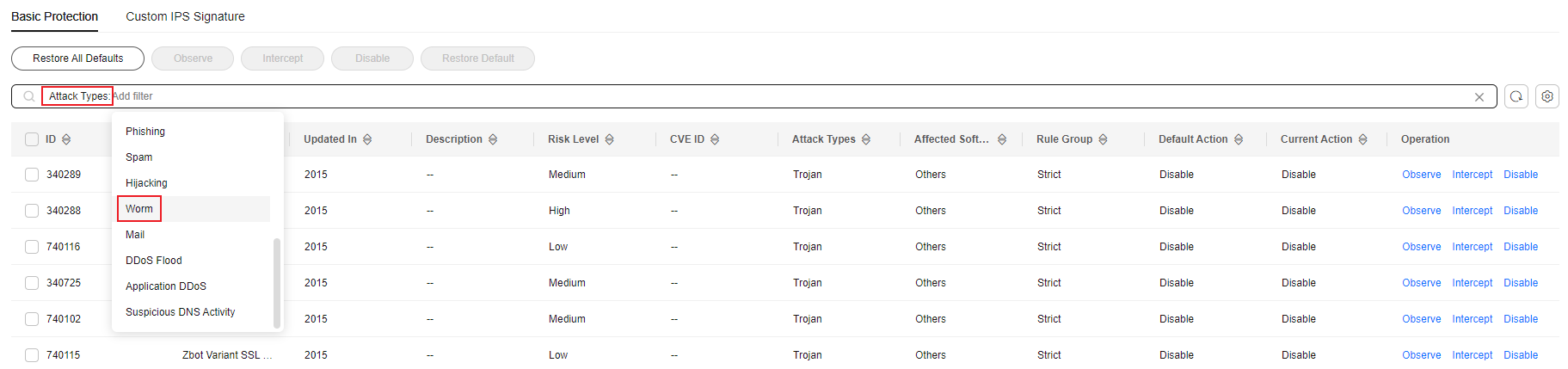
- Filter the rules for defending against worms. In the filter above the list, select Worm from the Attack Types drop-down list.
Figure 1 Worm attack
- Enable protection in batches. Select multiple rules at a time and click Intercept.
Intercept: The firewall records the traffic that matches the current rule in attack event logs and blocks the traffic.
- For details about how to view attack event logs, see Attack Event Logs.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





