Using IAM Identity Policies to Grant Access to DSC
Identity policy-based authorization provided by Identity and Access Management (IAM) lets you control access to DSC. With IAM, you can create IAM users or user groups for employees based on the organizational structure of your enterprise. Each IAM user or user group has their own security credentials, providing access to DSC resources.
- Grant only the permissions required for users to perform a task.
- Entrust a Huawei Cloud account or a cloud service to perform professional and efficient O&M on your WAF resources.
If your Huawei Cloud account does not require individual IAM users, skip this chapter.
This section describes the policy-based authorization method. Authorization Process shows the authorization process.
Prerequisites
Before granting permissions, learn about the DSC permissions and select them as required. To grant other service permissions, learn about permissions supported by IAM by referring to System-defined Policies/Roles.
Authorization Process
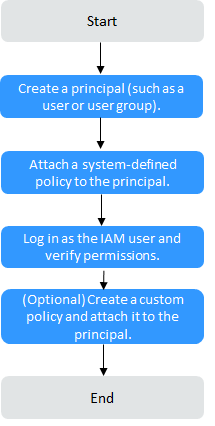
- On the IAM console, create an IAM user or create a user group.
Create a user or user group on the IAM console.
- Attach a system identity policy to a user or user group.
Grant the DSC system-defined identity policy DSCReadOnlyAccessPolicy to a user or user group, or add the policy to the user or user group.
- Log in as the IAM user and verify permissions.
Log in to the console as an authorized user and test the permissions.
- Choose Service List > Data Security Center. On the DSC console, click Buy DSC. If the purchase fails (assuming that the current policy contains only DSC ReadOnlyAccess), the DSC ReadOnlyAccess policy has already taken effect.
- Choose any other service in the Service List. If a message appears indicating insufficient permissions to access the service, the DSC ReadOnlyPolicy policy has already taken effect. (Assume that the current policy contains only DSC ReadOnlyPolicy.)
Example Custom Policies
Custom policies can be created as a supplement to the system-defined policies of DEW.
You can create custom policies in either of the following ways:
- Visual editor: Select cloud services, actions, resources, and request conditions. This does not require knowledge of policy syntax.
- JSON: Edit JSON policies from scratch or based on an existing policy.
For details, see Creating a Custom Identity Policy and Attaching It to a Principal.
When creating a custom policy, use the Resource element to specify the resources the policy applies to and use the Condition element (condition keys) to control when the policy is in effect. The following provides examples of custom WAF policies.
- Example 1: Grant a custom policy.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46
{ "Version": "5.0", "Statement": [ { "Effect": "Allow", "Action": [ "dsc:common:list", "dsc:common:operate", "dsc:authorization:grant", "dsc:asset:create", "dsc:asset:delete", "dsc:overview:list", "dsc:asset:list", "dsc:common:list", "dsc:common:operate", "dsc:maskTask:create", "dsc:maskTask:update", "dsc:maskTask:list", "dsc:maskTask:get", "dsc:maskTask:operate", "dsc:maskTask:listSubTasks", "dsc:scanTask:create", "dsc:scanTask:update", "dsc:scanTask:delete", "dsc:scanTask:operate", "dsc:scanTask:list", "dsc:scanRuleGroup:update", "dsc:scanRuleGroup:list", "dsc:scanRuleGroup:create", "dsc:scanRuleGroup:update", "dsc:scanRule:get", "dsc:scanRule:list", "dsc:scanRule:create", "dsc:scanRule:update", "dsc:scanRule:delete", "dsc:scanTask:getResults", "dsc:scanTemplate:list", "dsc:scanTemplate:create", "dsc:scanTemplate:delete", "dsc:scanTemplate:update", "dsc:watermark:embed", "dsc:watermark:extract" ] } ] }
- Example 2: Create a custom policy containing multiple actions.
A custom policy can contain the actions of multiple services. The following is an example policy containing actions of multiple services:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21
{ "Version": "5.0", "Statement": [ { "Effect": "Allow", "Action": [ "dsc:overview:list", "dsc:authorization:get" ] }, { "Effect": "Allow", "Action": [ "ecs:cloudServers:createServers", "ecs:cloudServers:listServersDetails" ] } ] }
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





