Step 4: Whitelist WAF Back-to-Source IP Addresses
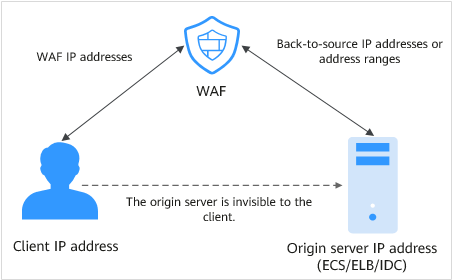
In cloud CNAME access mode, to let WAF take effect, configure ACL rules on the origin server to trust only the back-to-source IP addresses of all your cloud WAF instances. This prevents hackers from attacking the origin server through the server IP addresses.

ACL rules must be configured on the origin server to whitelist WAF back-to-source IP addresses. Otherwise, your website visitors will frequently receive 502 or 504 error code when your website is connected to WAF.
What Are Back-to-Source IP Addresses?
From the perspective of a server, all web requests originate from WAF. The IP addresses used by WAF forwarding are back-to-source IP addresses of WAF. The real client IP address is written into the X-Forwarded-For (XFF) HTTP header field.

- There will be more WAF IP addresses due to scale-out or new clusters. For your legacy domain names, WAF IP addresses usually fall into several class C IP addresses (192.0.0.0 to 223.255.255.255) of two to four clusters.
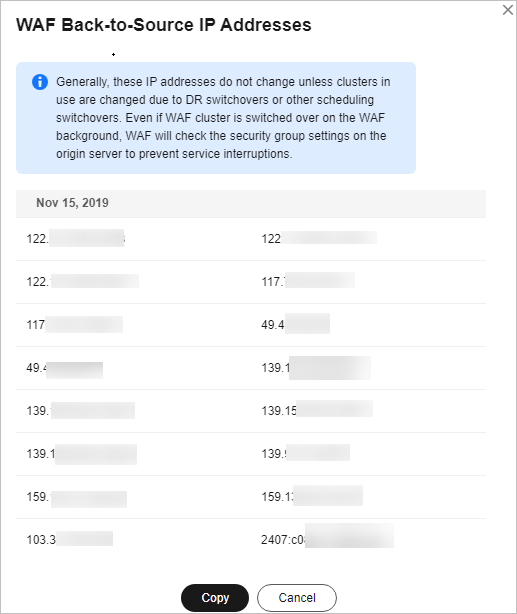
- Generally, these IP addresses do not change unless clusters in use are changed due to DR switchovers or other scheduling switchovers. Even when WAF cluster is switched over on the WAF background, WAF will check the security group configuration on the origin server to prevent service interruptions.
WAF Back-to-Source IP Address Check Mechanism
A back-to-source IP address, or WAF IP address, is randomly allocated from the back-to-source IP address range. When WAF forwards requests to the origin server, WAF will check the IP address status. If the IP address is abnormal, WAF will remove it and randomly allocate a normal one to receive or send requests.
Why Do I Need to Whitelist the WAF IP Address Ranges?
All web requests originate from a limited quantity of WAF IP addresses. The security software on the origin server may most likely regard these IP addresses as malicious and block them. Once WAF IP addresses are blocked, the website may fail to be accessed or it opens extremely slowly. To fix this, add the WAF IP addresses to the whitelist of the security software.

After you connect your website to WAF, uninstall other security software from the origin server or allow only the requests from WAF to access your origin server. This ensures normal access and protects the origin server from hacking.
Procedure
- Log in to the management console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - Click
 in the upper left corner and choose Web Application Firewall under Security & Compliance.
in the upper left corner and choose Web Application Firewall under Security & Compliance. - In the navigation pane, choose Website Settings.
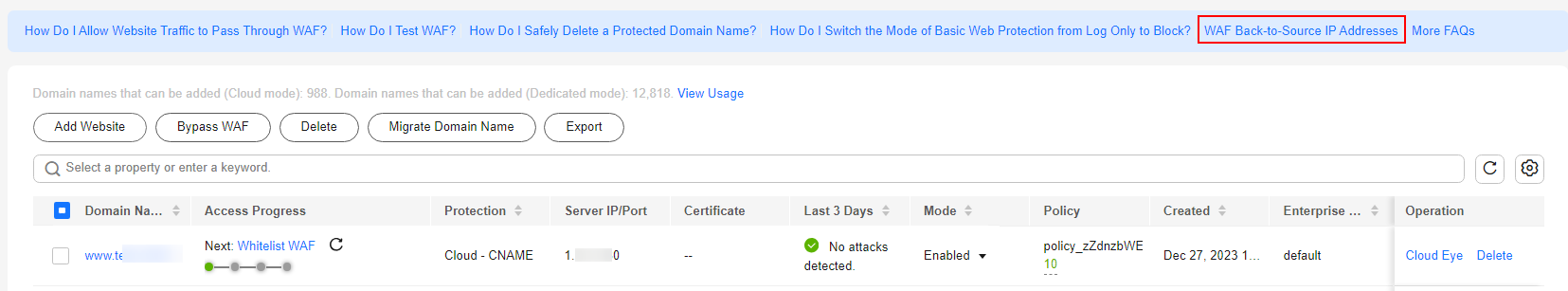
- Above the website list, click WAF Back-to-Source IP Addresses.
Figure 2 WAF Back-to-Source IP Addresses
- In the displayed dialog box, click Copy to copy all the addresses.
Figure 3 WAF Back-to-Source IP Addresses dialog box
- Open the security software on the origin server and add the copied IP addresses to the whitelist.
- If your origin servers are deployed on the Huawei Cloud ECSs, see Whitelisting WAF IP Addresses on Origin Servers That Are Deployed on ECSs.
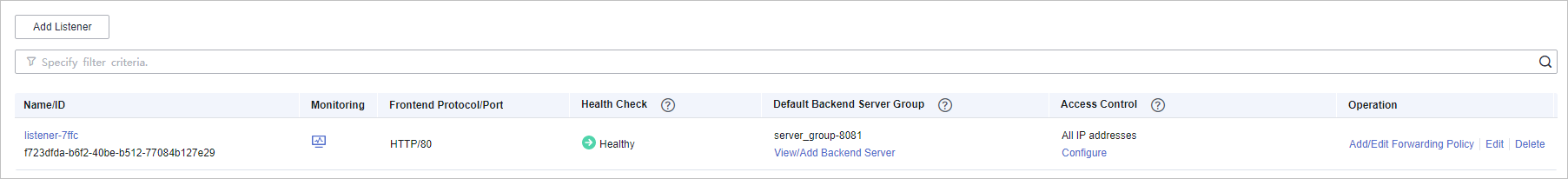
- If your origin servers use Huawei Cloud ELB, see Whitelisting WAF IP Addresses on Origin Servers That Use Huawei Cloud ELB.
- If you also use Cloud Firewall (CFW) on Huawei Cloud, refer to Adding a Protection Rule.
- If your website is deployed on servers on other cloud vendors, whitelist the WAF IP addresses in the corresponding security group and access control rules.
- If only the personal antivirus software is installed on the origin server, the software does not have the interface for whitelisting IP addresses. If the origin server provides external web services, install the enterprise security software on or use Huawei Cloud Host Security Service (HSS) for the server. These products identify the sockets of some IP addresses with a large number of requests and occasionally disconnect the connections. Generally, the IP addresses of WAF are not blocked.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot