What Is Access Control?
- A security group protects the instances in it.
- A network ACL protects associated subnets and all the resources in the subnets.
Figure 1 shows how security groups and network ACLs are used. Security groups A and B protect the network security of ECSs. Network ACLs A and B add an additional layer of defense to subnets 1 and 2.
Differences Between Security Groups and Network ACLs
Item |
Security Group |
Network ACL |
|---|---|---|
Protection Scope |
Protects instances in a security group, such as ECSs, databases, and containers. |
Protects subnets and all the instances in the subnets. |
Mandatory |
Mandatory. Instance must be added to at least one security group. |
Optional. You can determine whether to associate a subnet with a network ACL based on service requirements. |
Rules |
Supports both Allow and Deny rules.
|
Supports both Allow and Deny rules.
|
Matching Order |
If an instance is associated with multiple security groups that have multiple rules:
|
A subnet can only have one network ACL. If there are multiple rules, the rules are processed based on their priorities. A smaller value indicates a higher priority. |
Usage |
|
Selecting a network ACL is not allowed when you create a subnet. You must create a network ACL, add inbound and outbound rules, associate subnets with it, and enable network ACL. The network ACL then protects the associated subnets and instances in the subnets. |
Packets |
Packet filtering based on the 3-tuple (protocol, port, and source/destination) is supported. |
Packet filtering based on the 5-tuple (protocol, source port, destination port, and source/destination) is supported. |
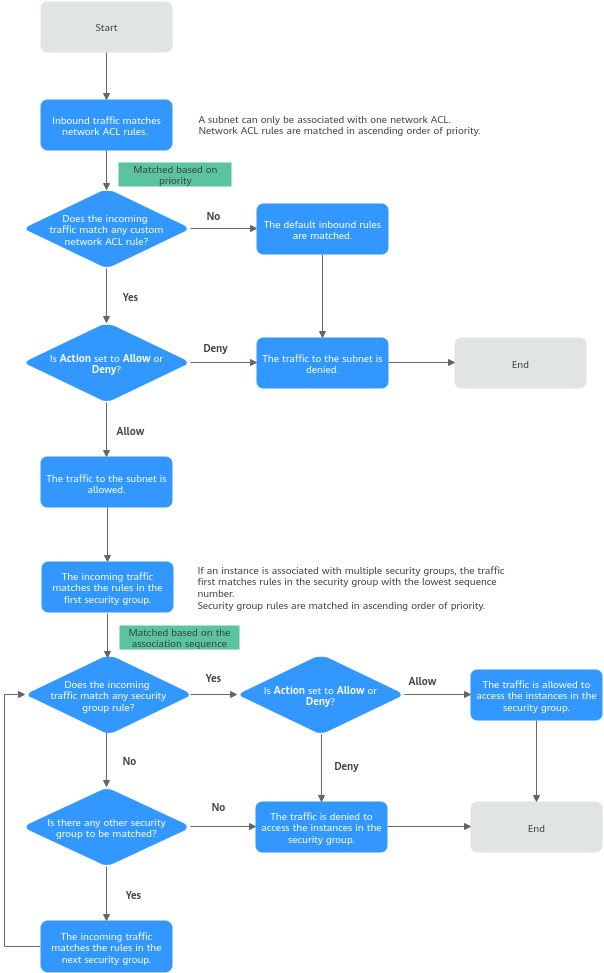
How Traffic Matches Security Group and Network ACL Rules
If both security group and network ACL rules are configured, traffic matches network ACL rules first and then security group rules. Figure 2 describes how inbound traffic matches security group and network ACL rules.
- Traffic first matches network ACL rules.
- If the traffic does not match any rule, the default rule is applied, and traffic to the subnet is denied.
- If the traffic matches a rule, the rule is applied, which determines where the traffic will go.
- If Action is set to Deny, the traffic to the subnet is denied.
- If Action is set to Allow, the traffic to the subnet is allowed.
- The traffic continues to match the security group rules.
- If an instance is associated with multiple security groups, the traffic first matches rules in the security group with the lowest sequence number.
- If the traffic does not match any rule, it is denied to access the instance.
- If the traffic matches a rule, the rule determines where the traffic will go.
- If Action is set to Deny, the traffic is denied to access the instance.
- If Action is set to Allow, the traffic is allowed to access the instance.
- If the traffic fails to match the rules in the first security group, it continues to match the rules in the second security group.
- If the traffic does not match the rules of all security groups, the traffic is denied.
- If an instance is associated with multiple security groups, the traffic first matches rules in the security group with the lowest sequence number.
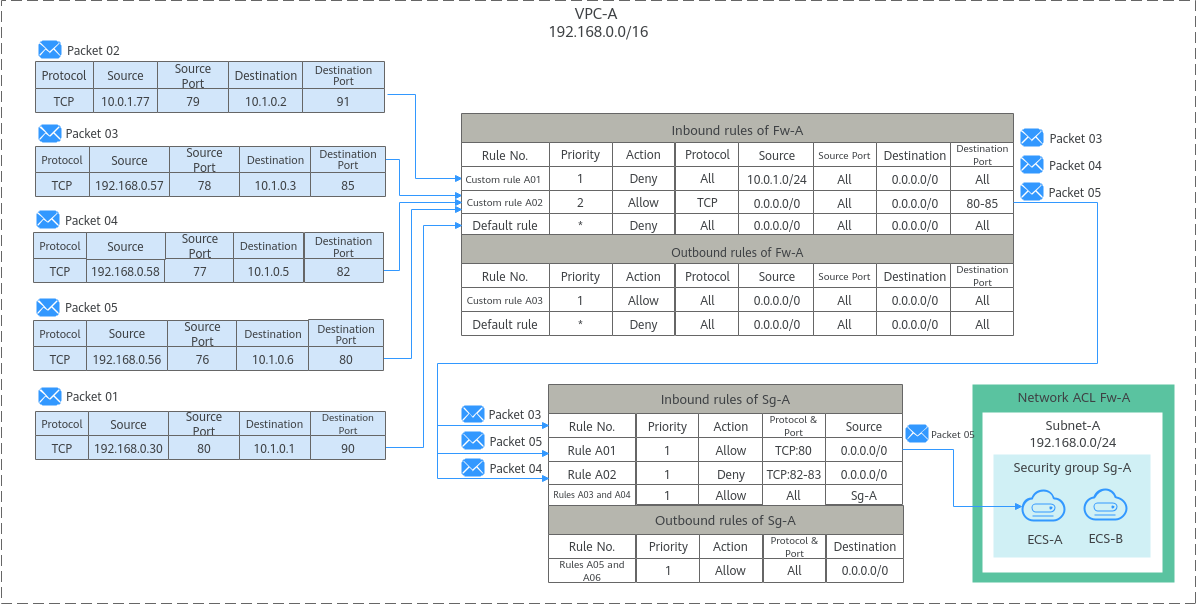
- Associate a network ACL (Fw-A) with Subnet-A. The default rules in Fw-A cannot be deleted. Traffic preferentially matches the rules you have configured. Table 2 shows some example rules.
- Create a security group Sg-A to protect the ECSs. When creating security group Sg-A, you can select an existing template. The template comes with some default rules. You can modify or delete default rules, or add rules. For details about security group rules, see Table 3.
Direction |
Priority |
Type |
Action |
Protocol |
Source |
Source Port Range |
Destination |
Destination Port Range |
Description |
|---|---|---|---|---|---|---|---|---|---|
Inbound |
1 |
IPv4 |
Deny |
All |
10.0.1.0/24 |
All |
0.0.0.0/0 |
All |
Custom rule A01: denies traffic from 10.0.1.0/24 to the subnet. |
Inbound |
2 |
IPv4 |
Allow |
TCP |
0.0.0.0/0 |
All |
0.0.0.0/0 |
80-85 |
Custom rule A02: allows all TCP traffic to the ECS in the subnet over ports 80 to 85. |
Inbound |
* |
-- |
Deny |
All |
0.0.0.0/0 |
All |
0.0.0.0/0 |
All |
Default rule: denies all inbound traffic. |
Outbound |
1 |
IPv4 |
Allow |
All |
0.0.0.0/0 |
All |
0.0.0.0/0 |
All |
Custom rule A03: allows all outbound traffic. |
Outbound |
* |
-- |
Deny |
All |
0.0.0.0/0 |
All |
0.0.0.0/0 |
All |
Default rule: denies all outbound traffic. |
Direction |
Priority |
Action |
Type |
Protocol & Port |
Source/Destination |
Description |
|---|---|---|---|---|---|---|
Inbound |
1 |
Allow |
IPv4 |
TCP: 80 |
Source: 0.0.0.0/0 |
Rule A01: allows all IPv4 traffic to the ECS over port 80. |
Inbound |
1 |
Deny |
IPv4 |
TCP: 82-83 |
Source: 0.0.0.0/0 |
Rule A02: denies all IPv4 traffic to the ECS over ports 82 and 83. |
Inbound |
1 |
Allow |
IPv4 |
All |
Source: current security group (Sg-A) |
Rule A03: allows all IPv4 traffic in the security group so the ECS can communicate with other instances in the security group. |
Inbound |
1 |
Allow |
IPv6 |
All |
Source: current security group (Sg-A) |
Rule A04: allows all IPv6 traffic in the security group so the ECS can communicate with other instances in the security group. |
Outbound |
1 |
Allow |
IPv4 |
All |
Destination: 0.0.0.0/0 |
Rule A05: allows all traffic from the ECS in the security group to any IPv4 address. |
Outbound |
1 |
Allow |
IPv6 |
All |
Destination: ::/0 |
Rule A06: allows all traffic from the ECS in the security group to any IPv6 address. |
Based on the preceding scenarios, different inbound packets match rules as follows:
- Packet 01: If no custom rules in Fw-A are matched, the default rule is applied, denying packet 01 to the subnet.
- Packet 02: If custom rule A01 in Fw-A is matched, this rule is applied, denying packet 02 to the subnet.
- Packet 03: If custom rule A02 in Fw-A is matched, this rule is applied, allowing packet 03 to the subnet. Packet 03 continues to match the security group rules. If it does not match any inbound rule in Sg-A, packet 03 is denied.
- Packet 04: If custom rule A02 in Fw-A is matched, this rule is applied, allowing packet 04 to the subnet. Packet 04 continues to match the security group rules. If it matches rule A02 in Sg-A, packet 04 is denied.
- Packet 05: If custom rule A02 in Fw-A is matched, this rule is applied, allowing packet 05 to the subnet. Packet 05 continues to match the security group rules. If it matches rule A01 in Sg-A, packet 05 is allowed.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot