IP Indicator Association (The IP intelligence association)
Playbook Overview
The IP intelligence association playbook automatically obtains the external source IP address information from the SecMaster Alerts page.
- If an IP address matches an indicator, the playbook automatically associates the alert with the indicator.
- If an external source IP address in an alert does not match any existing indicator, this playbook automatically queries the ThreatBook API for its reputation. It then creates a new indicator with that intelligence in the Indicators module and associates it with the alert.
You need to enable this playbook manually.
Trigger condition: A new alert is added to SecMaster, and the alert contains external source IP addresses.
Prerequisites
- Your SecMaster professional edition is available.
-
You have available quota for querying indicators in ThreatBook.
- Logs of cloud services such as WAF, HSS, and CFW have been connected to SecMaster, and the Auto Alert Conversion button has been toggled on. For details about how to connect logs to SecMaster, see Enabling Log Access.
Step 1: Configure an Operation Connection
- Log in to the SecMaster console.
- In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 1 Workspace management page

- In the navigation pane on the left, choose . On the displayed page, click the Operation Connections tab. Figure 2 Operation Connections tab

- On the Operation Connection tab, click Edit in the Operation column of the row that contains threatbook authentication token.
- On the Edit Operation Connection panel sliding out from the right, configure the token.
- freeApiKey or paidApiKey: Set either of them. The value can be obtained after you buy ThreatBook quota.
- redisHost: IP address of your Redis resources. If there are no IP addresses, leave this parameter blank.
- redisPort: Port of your Redis resources. If there are no such ports, leave this parameter blank.
- redisPassword: Passwords of your Redis resources. If there are no such passwords, leave this parameter blank.
- Click OK.
Step 2: Enable the IP Intelligence Association Playbook
- Log in to the SecMaster console.
- In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 3 Workspace management page

- In the navigation pane on the left, choose Security Orchestration > Playbooks. Figure 4 Accessing the Playbooks tab
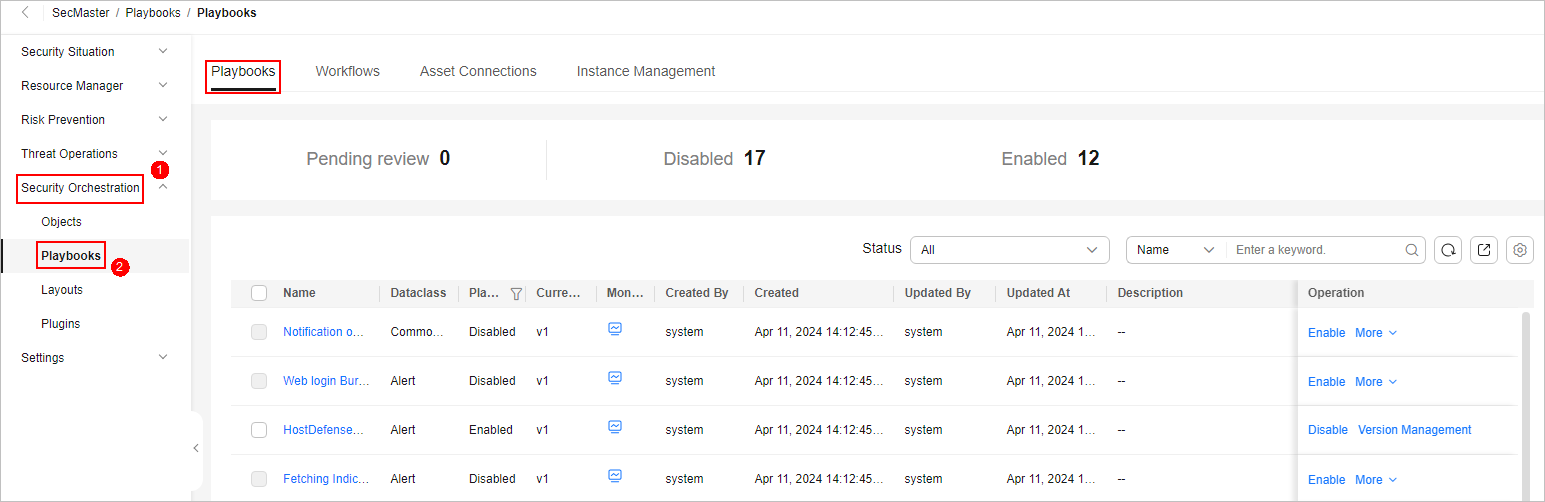
- On the Playbooks page, search for the The IP intelligence association playbook and click Enable in the Operation column of the playbook.
- In the dialog box displayed, select the initial playbook version v1 and click OK. If the Playbook Status of the The IP intelligence association playbook changes to Enabled, the playbook has been enabled successfully.
Implementation Effect
If the playbook takes effect, go to the page of the target SecMaster workspace. On the Indicators page, you can view the new indicators.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





