Creating an IAM User and Granting the LakeFormation Permissions to Users
This section describes how to use IAM to implement fine-grained permissions control for your LakeFormation instances. With IAM, you can:
- Create IAM users for employees based on your enterprise's organizational structure. Each IAM user will have their own security credentials for accessing the resources.
- Assign users only the permissions required to perform a given task based on their job responsibilities.
- Entrust an account or a cloud service to perform professional and efficient O&M on your resources.
If your cloud account does not need individual IAM users, skip this section.
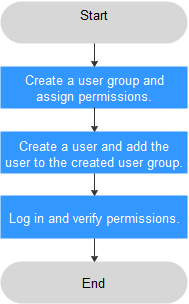
This section describes the procedure for granting permissions. See Figure 1 for details.
Prerequisites
Before assigning permissions to a user group, learn about LakeFormation permissions in LakeFormation Permissions and select them as needed.
If you need to assign permissions to other services, check all the policies supported by IAM in System-defined Permissions.
Procedure
- Creating a User Group and Assigning Permissions
Create a user group on the IAM console, and assign LakeFormation permissions to the group.
- Create an IAM user.
Create a user on the IAM console and add the user to the group created in 1.

The IAM username for operating LakeFormation instances can contain only letters, digits, and underscores (_). Otherwise, LakeFormation cannot be used.
- Log in and verify permissions.
Log in to the console as the user you created, and verify that the user has the assigned permissions.
You can perform the following operation to verify a permission:
Click the service list and choose LakeFormation. On the Overview page, click Buy Instance in the upper right corner. If the instance creation page is displayed, the lakeformation:role:create permission has already taken effect.
LakeFormation Permissions
By default, new IAM users lack permissions assigned. Add a user to one or more groups, and attach permissions policies or roles to these groups. Users inherit permissions from the groups to which they are added and can perform specified operations on cloud services.
You can grant permissions to a role or by creating a policy.
- Roles: A coarse-grained IAM authorization strategy to assign permissions based on user responsibilities. Only a limited number of service-level roles are available. Some roles depend other roles to take effect. When you assign such roles to users, remember to assign the roles they depend on. Roles are not an ideal choice for fine-grained authorization and secure access control.
- Read-only permission authorization using IAM: To assign the read-only permission of LakeFormation in an IAM project to a sub-user, create a user group for this user as a tenant administrator and add the LakeFormation ReadOnlyAccess system-defined policy to this user group.
- Enterprise project authorization: To assign all permission of LakeFormation in an enterprise project to a sub-user, create a user group for this user as a tenant administrator and add the LakeFormation CommonAccess permission to the user group and make this permission apply globally. Then, grant this permission to this enterprise project.
- Policies: A type of fine-grained authorization that defines permissions required to perform operations on specific cloud resources under certain conditions. This type of authorization is more flexible and ideal for secure access control. Most fine-grained policies split permissions by API. For details about how to customize IAM policies for LakeFormation, see Creating a LakeFormation Custom Policy.
|
Role/Policy Name |
Description |
Type |
Dependency |
|---|---|---|---|
|
LakeFormation FullAccess |
Administrator permissions for LakeFormation. Users granted these permissions can use all LakeFormation functions. |
System policy |
|
|
LakeFormation ReadOnlyAccess |
Read-only permissions for LakeFormation. Users granted these permissions can query LakeFormation data. |
System policy |
|
|
LakeFormation CommonOperations |
Basic permissions for LakeFormation, including viewing, authorizing, and canceling the LakeFormation service agreement and basic permissions for dependent services such as OBS and TMS. |
System policy |
|
|
Operation Type |
Policy |
Description |
|---|---|---|
|
Read-only |
lakeformation:access:describe |
Querying the access client |
|
Read-only |
lakeformation:agency:describe |
Querying an agency |
|
Read-only |
lakeformation:catalog:describe |
Querying catalog metadata |
|
Read-only |
lakeformation:configuration:describe |
Querying configurations |
|
Read-only |
lakeformation:credential:describe |
Obtaining authentication information |
|
Read-only |
lakeformation:database:describe |
Querying database metadata |
|
Read-only |
lakeformation:function:describe |
Query function metadata. |
|
Read-only |
lakeformation:group:describe |
Obtaining the relationship between a user group and associated roles |
|
Read-only |
lakeformation:instance:describe |
Querying an instance |
|
Read-only |
lakeformation:instanceJob:describe |
Querying an instance-level task |
|
Read-only |
lakeformation:job:describe |
Querying a task |
|
Read-only |
lakeformation:obs:describe |
Querying the list of OBS buckets |
|
Read-only |
lakeformation:policy:describe |
Obtaining a permission policy |
|
Read-only |
lakeformation:policy:export |
Obtaining permission policies in batches |
|
Read-only |
lakeformation:role:describe |
Querying a role |
|
Read-only |
lakeformation:table:describe |
Querying table metadata |
|
Read-only |
lakeformation:tag:describe |
Querying tags of a resource |
|
Read-only |
lakeformation:user:describe |
Obtaining relationship between user and associated roles |
|
Read-only |
lakeformation:dataset:describe |
Querying the metadata of a dataset |
|
Read-only |
lakeformation:dataset:describeFile |
Querying the metadata of a dataset file |
|
Read-only |
lakeformation:dataset:describeFileGroup |
Querying the metadata of a dataset file group |
|
Read-only |
lakeformation:model:describe |
Querying the metadata of a model |
|
Read-only |
lakeformation:model:describeFile |
Query the metadata of a model file. |
|
Write |
lakeformation:access:create |
Creating a client for service access |
|
Write |
lakeformation:access:delete |
Deleting the client for service access |
|
Write |
lakeformation:agency:create |
Creating an agency |
|
Write |
lakeformation:agency:drop |
Deleting an agency |
|
Write |
lakeformation:catalog:alter |
Modifying catalog metadata |
|
Write |
lakeformation:catalog:create |
Creating catalog metadata |
|
Write |
lakeformation:catalog:drop |
Deleting catalog metadata |
|
Write |
lakeformation:database:alter |
Modifying database metadata |
|
Write |
lakeformation:database:create |
Creating database metadata |
|
Write |
lakeformation:database:drop |
Deleting database metadata |
|
Write |
lakeformation:dataset:create |
Creating dataset metadata |
|
Write |
lakeformation:file:create |
Creating a file |
|
Write |
lakeformation:file:drop |
Deleting a file |
|
Write |
lakeformation:file:alter |
Modifying a file |
|
Write |
lakeformation:function:alter |
Modifying function metadata |
|
Write |
lakeformation:function:create |
Creating function metadata |
|
Write |
lakeformation:function:drop |
Deleting function metadata |
|
Write |
lakeformation:group:alter |
Modifying the relationship between a user group and associated roles |
|
Write |
lakeformation:instance:access |
Applying for service access |
|
Write |
lakeformation:instance:alter |
Modifying an instance |
|
Write |
lakeformation:instance:create |
Creating an instance |
|
Write |
lakeformation:instance:drop |
Deleting an instance |
|
Write |
lakeformation:instanceJob:alter |
Modifying an instance-level task |
|
Write |
lakeformation:instanceJob:create |
Creating an instance-level task |
|
Write |
lakeformation:instanceJob:drop |
Deleting an instance-level task |
|
Write |
lakeformation:instanceJob:exec |
Executing an instance-level task |
|
Write |
lakeformation:instance:createSubscriber |
Creating a metadata event subscriber |
|
Write |
lakeformation:instance:deleteSubscriber |
Deleting a metadata event subscriber |
|
Write |
lakeformation:job:alter |
Modifying a non-instance-level task |
|
Write |
lakeformation:job:create |
Creating a non-instance-level task |
|
Write |
lakeformation:job:drop |
Deleting a non-instance-level task |
|
Write |
lakeformation:job:exec |
Executing a non-instance-level task |
|
Write |
lakeformation:model:create |
Creating model metadata |
|
Write |
lakeformation:metadata:restore |
Restoring metadata |
|
Write |
lakeformation:part:alter |
Modifying a partition |
|
Write |
lakeformation:part:drop |
Deleting a partition |
|
Write |
lakeformation:part:create |
Creating a partition |
|
Write |
lakeformation:policy:create |
Creating a permission policy |
|
Write |
lakeformation:policy:drop |
Deleting a permission policy |
|
Write |
lakeformation:role:alter |
Modifying the relationship between a role and associated user group |
|
Write |
lakeformation:role:create |
Creating a role |
|
Write |
lakeformation:role:drop |
Deleting a role |
|
Write |
lakeformation:table:alter |
Modifying table metadata |
|
Write |
lakeformation:table:create |
Creating table metadata |
|
Write |
lakeformation:table:drop |
Deleting table metadata |
|
Write |
lakeformation:tableFile:alter |
Modifying a table file |
|
Write |
lakeformation:tableFile:create |
Creating a table file |
|
Write |
lakeformation:tableFile:drop |
Deleting a table file |
|
Write |
lakeformation:tableFileGroup:alter |
Modifying the metadata of the table file group |
|
Write |
lakeformation:tableFileGroup:create |
Creating the metadata of the table file group |
|
Write |
lakeformation:tableFileGroup:drop |
Deleting the metadata of a table file group |
|
Write |
lakeformation:transaction:operate |
Operating transactions |
|
Write |
lakeformation:user:alter |
Modifying the relationship between a user and associated roles |
|
Permission management |
lakeformation:accessService:grant |
Authorizing an access service |
|
Permission management |
lakeformation:accessTenant:grant |
Authorizing an access tenant |
|
Permission management |
lakeformation:accessAgency:describe |
Querying agency information |
|
Permission management |
lakeformation:accessService:describe |
Viewing an access service |
|
Permission management |
lakeformation:agreement:describe |
Querying a service agreement authorization |
|
Permission management |
lakeformation:agreement:cancel |
Canceling a service agreement authorization |
|
Permission management |
lakeformation:agreement:grant |
Granting a service agreement authorization |
|
Permission management |
lakeformation:instance:authorizeLocation |
Authorize an OBS path to LakeFormation |
|
Permission management |
lakeformation:instance:cancelAuthorizeLocation |
Canceling the authorization of an OBS path |
|
Permission management |
lakeformation:policy:delegate |
Delegating a permission policy to another authorization entity |
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot