Managing Isolated Files
HSS can isolate detected threat files. Files that have been isolated are displayed on a slide-out panel on the Server Alarms page. You can click Isolated Files on the upper right corner to check them, and can recover or delete isolated files anytime.
For details about events that can be isolated and killed, see Server Alarms.
Constraints
Servers that are not protected by HSS do not support alarm-related operations.
Isolation and Killing Operations
- Log in to the HSS console.
- Click
 in the upper left corner and select a region or project.
in the upper left corner and select a region or project. - In the navigation pane on the left, choose Detection & Response > Alarms and click Server Alarms.
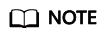
Figure 1 Server alarms
- (Optional) If you have enabled the enterprise project function, select an enterprise project from the Enterprise Project drop-down list in the upper part of the page to view its data.
- Locate an event that can be isolated and killed, click Handle in the Operation column, and select Isolate and Kill in the displayed box.
- Click OK and isolate and kill the target alarm event.
Files that have been isolated are displayed on a slide-out panel on the Server Alarms page and cannot harm your servers. You can click Isolated Files on the upper right corner to check them.
Checking Isolated Files
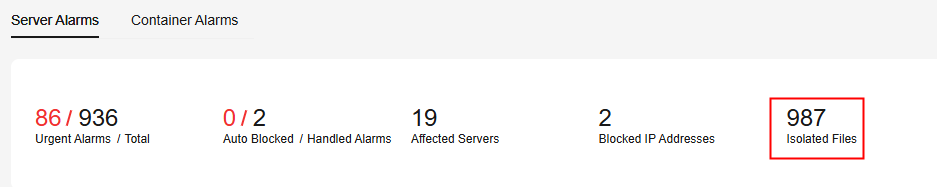
- In the alarm statistics area on the Server Alarms page, click the number above Isolated Files to check the isolated files.
Figure 2 Alarm statistics
- Check the servers, names, paths, and modification time of the isolated files.
Restoring Isolated Files
If you want to de-isolate an isolated file, you can restore it by referring to the following steps. The permissions for this file will be restored to what they were before it was isolated. Exercise caution when performing this operation.
- Click Restore in the Operation column of the list. The dialog box is displayed.
- Click OK.
Deleting Isolated Files
If you want to permanently delete an isolated file, you can perform the deletion operation by referring to the following steps.
- Click Delete in the Operation column of the list. The dialog box is displayed.
To delete isolated files in batches, select multiple isolated files and click Delete in the upper left corner of the list.
- Click OK.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot