Handling Vulnerabilities
Scenario
If HSS detects a vulnerability on a server, you need to handle the vulnerability in a timely manner based on its severity and your business conditions to prevent the vulnerability from being exploited by intruders.
Vulnerabilities can be handled in the following ways. For details, see Handling Vulnerabilities.
- Fixing vulnerabilities
If a vulnerability may harm your services, fix it as soon as possible. For Linux and Windows vulnerabilities, you can let HSS fix them in one-click. Web-CMS vulnerabilities, emergency vulnerabilities, and application vulnerabilities cannot be automatically fixed. Handle them by referring to the suggestions provided on the vulnerability details page.
- Ignoring vulnerabilities
Some vulnerabilities are risky only in specific conditions. For example, if a vulnerability can be exploited only through an open port, but the target server does not open any ports, the vulnerability will not harm the server. If you can confirm that a vulnerability is harmless, you can ignore it.
- Adding vulnerabilities to the whitelist
If you can confirm that a vulnerability does not affect your services and does not need to be fixed, you can add it to the whitelist. After a vulnerability is added to the whitelist, its status will change to Ignored in the vulnerability list, and it will not be reported in later scans.
Constraints
- For details about vulnerability handling operations supported by each HSS version, see Types of Vulnerabilities That Can Be Scanned and Fixed by HSS.
- CentOS 7, CentOS 8, Debian 9 and 10, Windows 2012 R2, and Ubuntu 14.04 and earlier have reached EOL and cannot be fixed because no official patches are available. You are advised to change to the OSs in active support.
- Ubuntu 16.04 to Ubuntu 22.04 do not support certain free patch updates. You need to subscribe to Ubuntu Pro to install upgrade packages. If Ubuntu Pro is not configured, vulnerabilities will fail to be fixed. For details about the vulnerabilities that need to be fixed by subscribing to Ubuntu Pro, see Do I Need to Subscribe to Ubuntu Pro to Fix Ubuntu Vulnerabilities?
- For paid channels of Oracle Enterprise Linux 8 and 9, you need to register an Unbreakable Linux Network (ULN) and subscribe to related channels to support automatic vulnerability fix.
- Fixing kernel vulnerabilities may cause servers to be unavailable. Therefore, HSS supports automatic fixing only for part of CCE kernel vulnerabilities. MRS, BMS, and most CCE kernel vulnerabilities cannot be automatically fixed. HSS filters out these types of vulnerabilities when batch fixing vulnerabilities.
- To handle vulnerabilities on a server, ensure the server is in the Running state, its agent status is Online, and its protection status is Protected.
- A maximum of 2000 vulnerabilities can be added to the whitelist.
Precautions
- Vulnerability fixing operations cannot be rolled back. If a vulnerability fails to be fixed, services will probably be interrupted, and incompatibility issues will probably occur in middleware or upper layer applications. To prevent unexpected consequences, you are advised to use CBR to back up ECSs. For details, see Purchasing a Server Backup Vault. Then, use idle servers to simulate the production environment and test-fix the vulnerability. If the test-fix succeeds, fix the vulnerability on servers running in the production environment.
- Servers need to access the Internet and use external image sources to fix vulnerabilities.
- Linux OS: If your servers cannot access the Internet, or the external image sources cannot provide stable services, you can use the image source provided by Huawei Cloud to fix vulnerabilities. Before fixing vulnerabilities online, configure the Huawei Cloud image sources that match your server OSs. For details, see Image Source Management.
- Windows OS: If your servers cannot access the Internet, ensure you have set up a patch server.
Vulnerability Fix Priority
The vulnerability fix priority is weighted based on the CVSS score, release time, and the importance of the assets affected by the vulnerability. It reflects the urgency of the fix.
By default, the importance of an asset is General. You can also change it. For details, see Servers Importance Management.
Vulnerabilities are classified into four priority levels: critical, high, medium, and low. You can refer to the priorities to fix the vulnerabilities that have significant impact on your server first.
- Critical: This vulnerability must be fixed immediately. Attackers may exploit this vulnerability to cause great damage to the server.
- High: This vulnerability must be fixed as soon as possible. Attackers may exploit this vulnerability to damage the server.
- Medium: You are advised to fix the vulnerability to enhance your server security.
- Low: This vulnerability has a small threat to server security. You can choose to fix or ignore it.
Vulnerability Display
Detected vulnerabilities will be displayed in the vulnerability list for seven days, regardless of whether you have handled them.
Handling Vulnerabilities
You can handle the vulnerability in following ways: After a vulnerability is handled, its status changes to Handled. You can select Handled or Unhandled above the list to view vulnerabilities or servers in the corresponding status.
You can only fix Linux and Windows vulnerabilities with one-click on the console. A maximum of 1,000 server vulnerabilities can be fixed at a time. If there are more than 1,000 vulnerabilities, fix them in batches.
- Log in to the HSS console.
- Click
 in the upper left corner and select a region or project.
in the upper left corner and select a region or project. - In the navigation pane, choose Risk Management > Vulnerabilities.
- Fix Linux and Windows vulnerabilities.
- Fixing a single vulnerability
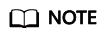
In the Operation column of a vulnerability, click Fix to fix all affected servers.
Figure 1 Fixing a single vulnerability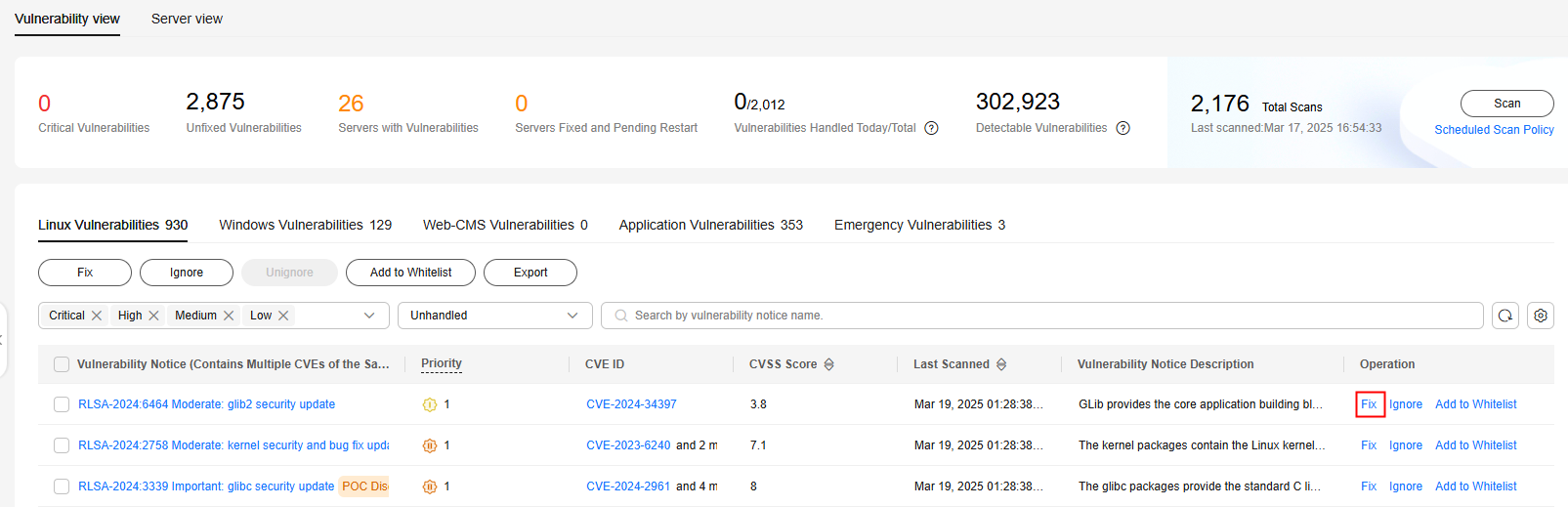
- Fixing multiple vulnerabilities
Select all target vulnerabilities and click Fix in the upper left corner of the vulnerability list to fix all affected servers.
Figure 2 Fixing multiple vulnerabilities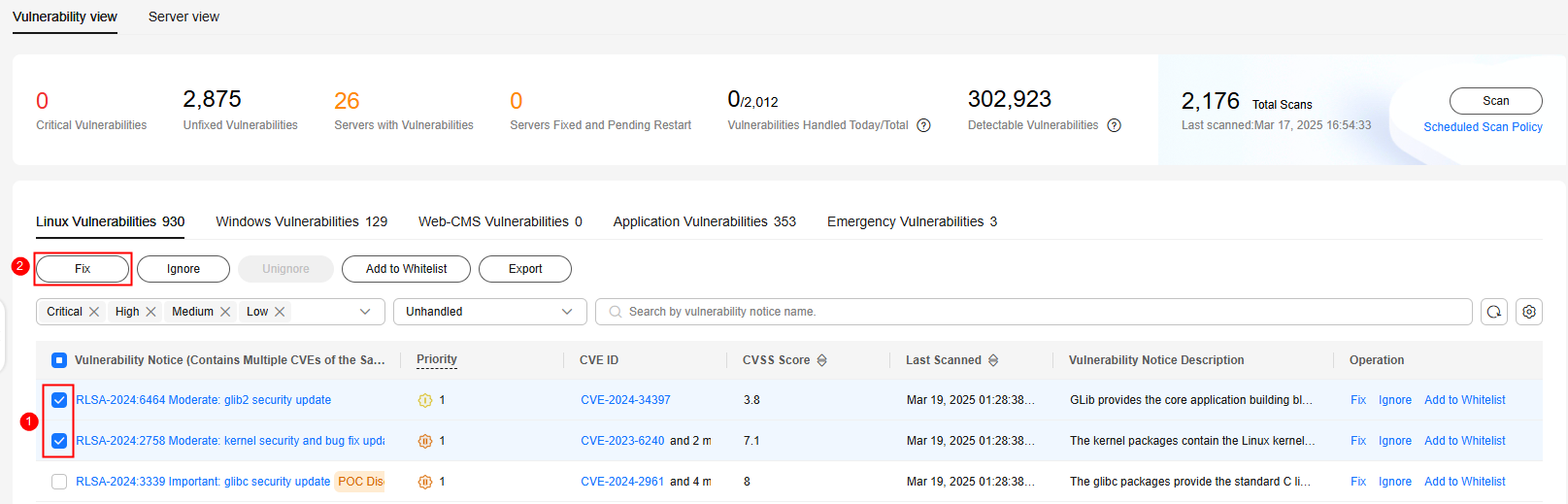
- Fix all vulnerabilities.
Click Fix in the upper left corner of the vulnerability list to fix all affected servers.
Figure 3 Fixing all vulnerabilities
- Fix one or more servers affected by a vulnerability.
- Click a vulnerability name.
- On the vulnerability details slide-out panel displayed, click the Affected tab, locate the row containing the target server, and click Fix in the Operation column.
You can also select all target servers and click Fix above the server list to fix vulnerabilities for the servers in batches.
Figure 4 Fix a server affected by a vulnerability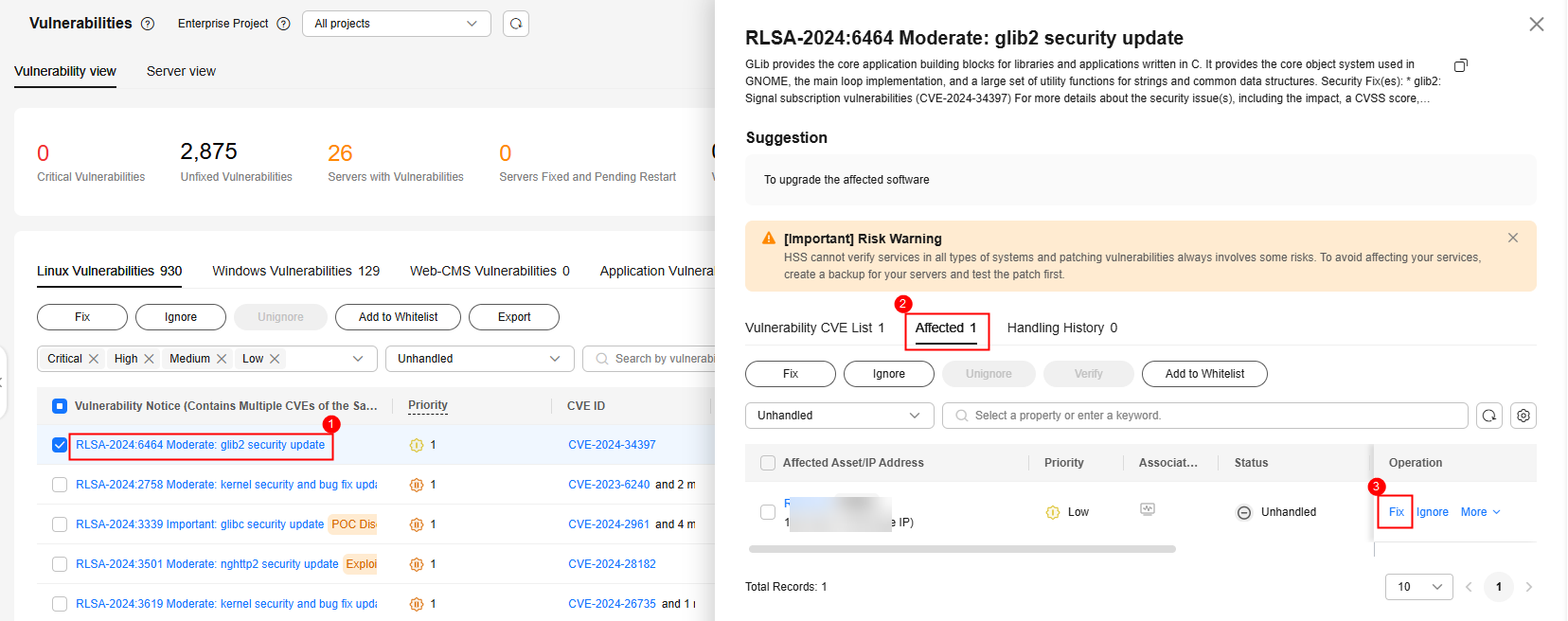
- Fixing a single vulnerability
- In the displayed dialog box, confirm the number of vulnerabilities to be fixed and the number of affected assets.
For Linux vulnerabilities, you can click View details in the Fix dialog box to view the name of the component to be fixed.
- (Optional) Back up servers.
Before fixing vulnerabilities, use HSS to back up servers, so that you can restore their data if it is affected by the fix. If you do not need to back up data, skip this step.
- In the Fix dialog box, click
 to enable backup.
to enable backup.
- After backup is enabled, the number of servers that can be backed up will be displayed below the toggle switch. Only the servers associated with backup vaults can be backed up. For more information, see Associating a Resource with the Vault.
- If backup is enabled in a vulnerability fix task, vulnerabilities can be fixed only on the servers that can be backed up in this task. For servers that fail to be backed up, start another vulnerability fix task for them.
Figure 5 Creating a backup
- Choose Select Server to Scan. The backup creation dialog box is displayed.
- In the Create Backup dialog box, set a backup file name, and click OK.
- In the Fix dialog box, click
- In the Fix dialog box displayed, select I am aware that if I have not backed up my ECSs before fixing vulnerabilities, services may be interrupted and fail to be rolled back during maintenance. and click Auto Fix.
If you have manually fixed the vulnerability, click Manual handling in the Fix dialog box. After the vulnerability is manually handled, its status changes to Fixed. If the vulnerability is not successfully fixed, it will still be displayed in the vulnerability list after the next vulnerability scan completes.
- Click a vulnerability name.
- Click the Handling History tab to view the fix status of the target vulnerability in the Status column. Table 1 describes vulnerability fix statuses.
Restart the system after you fixed a Windows OS or Linux kernel vulnerability, or HSS will probably continue to warn you of this vulnerability.
Table 1 Vulnerability fix statuses Status
Description
Unhandled
The vulnerability is not fixed.
Ignored
The vulnerability does not affect your services. You have ignored it or added it to the whitelist.
Verifying
HSS is verifying whether a fixed vulnerability is successfully fixed.
Fixing
HSS is fixing the vulnerability.
Fixed
The vulnerability has been successfully fixed.
Restart required
The vulnerability has been successfully fixed. You need to restart the server as soon as possible.
Failed
The vulnerability fails to be fixed. The possible cause is that the vulnerability does not exist or has been changed.
Restart the server and try again
This status is displayed only for vulnerabilities that exist on Windows servers.
The vulnerability has not been fixed on the Windows server for a long time. As a result, the latest patch cannot be installed. You need to install an earlier patch, restart the server, and then install the latest patch.
You can only fix Linux and Windows vulnerabilities with one-click on the console.
- Log in to the HSS console.
- Click
 in the upper left corner and select a region or project.
in the upper left corner and select a region or project. - In the navigation pane, choose Risk Management > Vulnerabilities.
- In the upper left corner of the page, select Server View.
- Fix Linux and Windows vulnerabilities.
- Fixing all Linux or Windows vulnerabilities on a server
- Locate the row containing a target server and click Fix in the Operation column.
You can also select multiple servers and click Fix above the list. If you want to fix vulnerabilities on all servers, do not select any server and click Fix.
Figure 6 Fixing all the Linux or Windows vulnerabilities on a server
- In the displayed dialog box, confirm the number of vulnerabilities to be fixed and the number of affected assets.
For Linux vulnerabilities, you can view fix commands in the dialog box to view the name of the component to be fixed.
- (Optional) Back up servers.
Before fixing vulnerabilities, use HSS to back up servers, so that you can restore their data if it is affected by the fix. If you do not need to back up data, skip this step.
- In the Fix dialog box, click
 to enable backup.
to enable backup.
- After backup is enabled, the number of servers that can be backed up will be displayed below the toggle switch. Only the servers associated with backup vaults can be backed up. For more information, see Associating a Resource with the Vault.
- If backup is enabled in a vulnerability fix task, vulnerabilities can be fixed only on the servers that can be backed up in this task. For servers that fail to be backed up, start another vulnerability fix task for them.
Figure 7 Creating a configuration backup
- Choose Select Server to Scan. The backup creation dialog box is displayed.
- In the Create Backup dialog box, set a backup file name, and click OK.
- In the Fix dialog box, click
- In the Fix dialog box displayed, select the type of the vulnerability to be fixed, select I am aware that if I have not backed up my ECSs before fixing vulnerabilities, services may be interrupted and fail to be rolled back during maintenance, and click OK.
Only Linux and Windows vulnerabilities can be automatically fixed with one-click. Web-CMS and application vulnerabilities need to be manually fixed by logging in to the server.
- Click the server name. On the server details slide-out panel displayed, view the vulnerability fix status. Table 2 describes vulnerability fix statuses.
Restart the system after you fixed a Windows OS or Linux kernel vulnerability, or HSS will probably continue to warn you of this vulnerability.
- Locate the row containing a target server and click Fix in the Operation column.
- Fixing one or more vulnerabilities on a server
- Click the name of a target server. The server details slide-out panel is displayed.
- Locate the row containing a target vulnerability and click Fix in the Operation column.
Alternatively, you can select all target vulnerabilities and click Fix above the vulnerability list to fix vulnerabilities in batches. To fix all vulnerabilities, click Fix with no need of selecting any servers.
Figure 8 Fixing a vulnerability on a server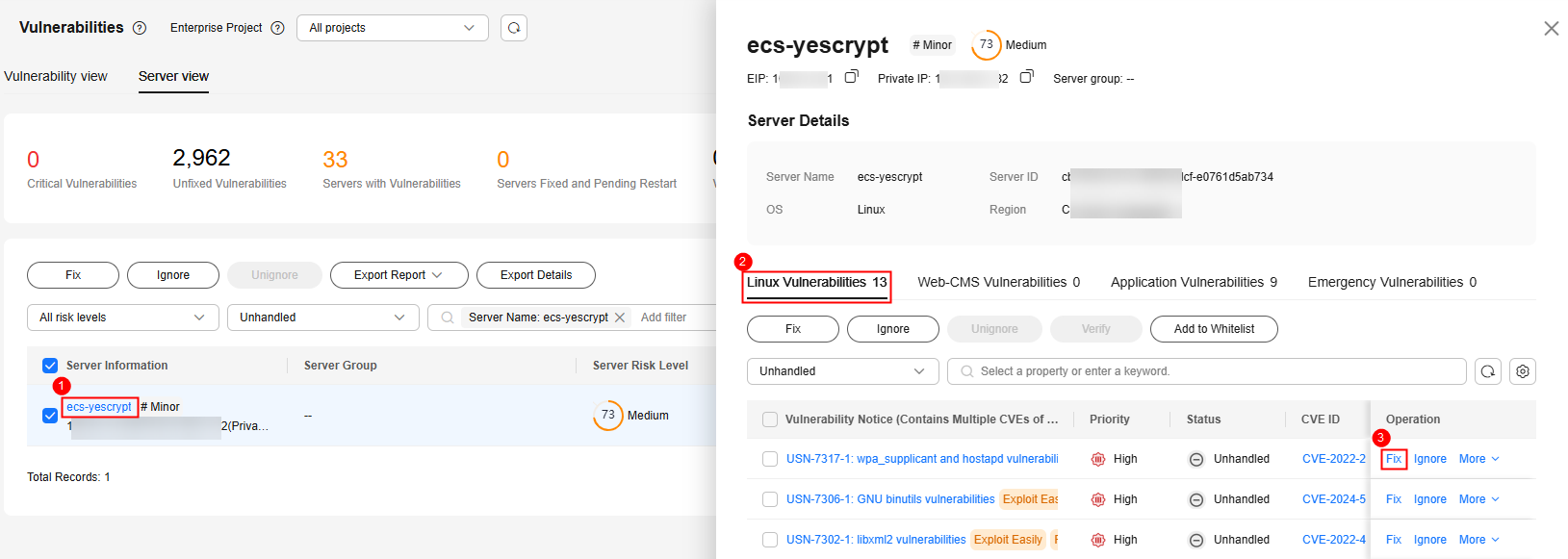
- In the displayed dialog box, confirm the number of vulnerabilities to be fixed and the number of affected assets.
For Linux vulnerabilities, you can view fix commands in the dialog box to view the name of the component to be fixed.
- (Optional) Back up servers.
Before fixing vulnerabilities, you can use HSS to back up servers, so that you can restore their data if it is affected by the fix. If you do not need to back up data, skip this step.
- In the Fix dialog box, click
 to enable backup.
to enable backup.
- After backup is enabled, the number of servers that can be backed up will be displayed below the toggle switch. Only the servers associated with backup vaults can be backed up. For more information, see Associating a Resource with the Vault.
- If backup is enabled in a vulnerability fix task, vulnerabilities can be fixed only on the servers that can be backed up in this task. For servers that fail to be backed up, start another vulnerability fix task for them.
Figure 9 Creating a backup
- Choose Select Server to Scan. The backup creation dialog box is displayed.
- In the Create Backup dialog box, set a backup file name, and click OK.
- In the Fix dialog box, click
- In the Fix dialog box displayed, select I am aware that if I have not backed up my ECSs before fixing vulnerabilities, services may be interrupted and fail to be rolled back during maintenance, and click Auto Fix.
If you have manually fixed the vulnerability, click Manual handling in the Fix dialog box. After the vulnerability is manually handled, its status changes to Fixed. If the vulnerability is not successfully fixed, it will still be displayed in the vulnerability list after the next vulnerability scan completes.
- In the Status column of the target vulnerability, view the fix status of the vulnerability. Table 2 describes vulnerability fix statuses.
Restart the system after you fixed a Windows OS or Linux kernel vulnerability, or HSS will probably continue to warn you of this vulnerability.
Table 2 Vulnerability fix statuses Status
Description
Unhandled
The vulnerability is not fixed.
Ignored
The vulnerability does not affect your services. You have ignored it or added it to the whitelist.
Verifying
HSS is verifying whether a fixed vulnerability is successfully fixed.
Fixing
HSS is fixing the vulnerability.
Fixed
The vulnerability has been successfully fixed.
Restart required
The vulnerability has been successfully fixed. You need to restart the server as soon as possible.
Failed
The vulnerability fails to be fixed. The possible cause is that the vulnerability does not exist or has been changed.
Restart the server and try again
This status is displayed only for vulnerabilities that exist on Windows servers.
The vulnerability has not been fixed on the Windows server for a long time. As a result, the latest patch cannot be installed. You need to install an earlier patch, restart the server, and then install the latest patch.
- Fixing all Linux or Windows vulnerabilities on a server
One-click automatic fix of Web-CMS, application, or application vulnerabilities is not supported by HSS. You can log in to the server and fix them manually by referring to the fix suggestions on the corresponding vulnerability details page.
- Restart the system after you fixed a Windows OS or Linux kernel vulnerability, or HSS will probably continue to warn you of this vulnerability.
- Fix the vulnerabilities in sequence based on the suggestions.
- If multiple software packages on the same server have the same vulnerability, you only need to fix the vulnerability once.
Viewing vulnerability fix suggestions
- Log in to the HSS console.
- Click
 in the upper left corner and select a region or project.
in the upper left corner and select a region or project. - In the navigation pane, choose Risk Management > Vulnerabilities.
- Click the name of a target vulnerability to access the vulnerability details slide-out panel and view the fix suggestions.
Fixing vulnerabilities by referring to vulnerability fix suggestions
Vulnerability fix may affect service stability. You are advised to use either of the following methods to avoid such impact:
- Method 1: Create a new VM to fix the vulnerability.
Use this method if you are fixing a vulnerability for the first time and cannot estimate impact on services. You are advised to choose the pay-per-use billing mode for the newly created ECS. After the service switchover, you can change the billing mode to yearly/monthly. In this way, you can release the ECS at any time to save costs if the vulnerability fails to be fixed.
- Create an image for the ECS to be fixed. For details, see Creating a Full-ECS Image Using an ECS.
- Use the image to create an ECS. For details, see Creating ECSs Using an Image.
- Fix the vulnerability on the new ECS and verify the result.
- Switch services over to the new ECS and verify they are stably running.
- Release the original ECS. If a fault occurs after the service switchover and cannot be rectified, you can switch services back to the original ECS.
- Method 2: Fix the vulnerability on the target server.
Use this method if you have fixed the vulnerability on similar servers before.
- Create a backup for the ECS whose vulnerabilities need to be fixed. For details, see Creating a CSBS Backup.
- Fix vulnerabilities on the current server.
- If services become unavailable after the vulnerability is fixed and cannot be recovered in a timely manner, use the backup to restore the server. For details, see Using Backups to Restore Servers.
Some vulnerabilities are risky only in specific conditions. For example, if a vulnerability can be exploited only through an open port, but the target server does not open any ports, the vulnerability will not harm the server. Such vulnerabilities can be ignored. HSS will not generate alarms for ignored vulnerabilities.
- Log in to the HSS console.
- Click
 in the upper left corner and select a region or project.
in the upper left corner and select a region or project. - In the navigation pane, choose Risk Management > Vulnerabilities.
- Locate the row containing a target vulnerability and click Ignore in the Operation column.
- In the dialog box displayed, click OK.
If you evaluate that some vulnerabilities do not affect your services and do not want to view the vulnerabilities in the vulnerability list, you can whitelist the vulnerabilities. After they are whitelisted, the vulnerabilities will be ignored. The vulnerabilities will not be scanned and the vulnerability information will not be displayed when the next vulnerability scan task is executed.
- Log in to the HSS console.
- Click
 in the upper left corner and select a region or project.
in the upper left corner and select a region or project. - In the navigation pane, choose Risk Management > Vulnerabilities.
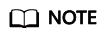
- Whitelisting all servers that are affected by a vulnerability
HSS will ignore the vulnerability when scanning for vulnerabilities on all servers.
- In the Operation column of a vulnerability, , click Add to Whitelist.
You can also select multiple vulnerabilities and click Add to Whitelist above the vulnerability list.
Figure 10 Whitelisting all servers that are affected by a vulnerability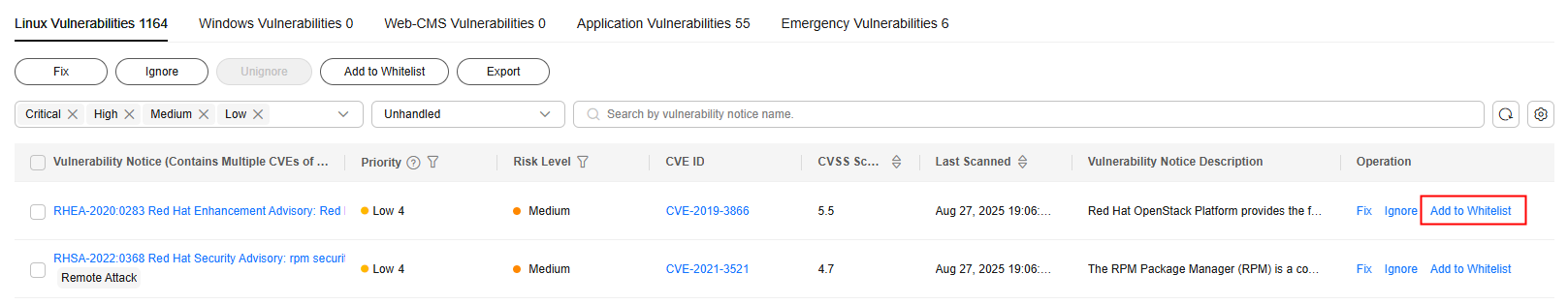
- In the dialog box displayed, click OK.
- In the Operation column of a vulnerability, , click Add to Whitelist.
- Whitelisting one or more servers that are affected by a vulnerability
HSS will ignore the vulnerability when scanning for vulnerabilities on these servers.
- Click a target vulnerability name.
- On the slide-out panel displayed, click the Affected tab.
- In the Operation column of the row containing the target server, click More and select Add to Whitelist.
You can also select multiple servers and click Add to Whitelist above the server list.
Figure 11 Whitelisting a single server that is affected by a vulnerability
- In the dialog box displayed, click OK.
- Whitelisting vulnerabilities using whitelist rules
- In the upper right corner of the Vulnerabilities page, click Vulnerability Whitelist.
- In the Vulnerability Whitelist area, click Add Rule.
- Configure a whitelist rule according to Table 3.
Figure 12 Configuring a whitelist rule

Table 3 Vulnerability whitelist rule parameters Parameter
Description
Type
Select the type of vulnerabilities to be whitelisted. Possible values are as follows:
- Linux Vulnerabilities
- Windows Vulnerabilities
- Web-CMS Vulnerabilities
- Application Vulnerabilities
Vulnerability
Select one or more vulnerabilities to be whitelisted.
Rule Scope
Select the servers affected by the vulnerabilities. Possible values are as follows:
- All servers
HSS will ignore the vulnerability when scanning for vulnerabilities on all servers.
- Selected servers
Select one or more target servers. HSS will ignore the vulnerabilities when scanning for vulnerabilities on these servers.
You can search for a target server by server name, ID, EIP, or private IP address.
Remarks (Optional)
Enter the remarks.
- Click OK.
- Whitelisting all servers that are affected by a vulnerability
Verifying the Vulnerability Fix
- Method 1: On the Affected tab page of the vulnerability details page, choose to verify the vulnerability fix. This method has the following restrictions:
- The fix of emergency vulnerabilities cannot be verified.
- Only the fix of the application vulnerabilities of the JAR package can be verified. The application vulnerabilities of non-JAR packages are automatically filtered out and not verified.
- Method 2: Ensure the software has been upgraded to the latest version. The following table provides the commands to check the software upgrade result.
Table 4 Verification commands OS
Command
CentOS/Fedora /Euler/Red Hat/Oracle
rpm -qa | grep Software_name
Debian/Ubuntu
dpkg -l | grep Software_name
Gentoo
emerge --search Software_name
- Method 3: Manually check for vulnerabilities and view the vulnerability fixing results.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





