(New) Managing Host Groups
Host groups allow you to configure host data ingestion efficiently. You can add multiple hosts to a host group and associate the host group with ingestion configurations. The ingestion configurations will then be applied to all the hosts in the host group. When there is a new host, simply add it to a host group and the host will automatically inherit the log ingestion configurations associated with the host group.
You can create host groups of the IP address and custom identifier types.
- Host Group Type set to IP: Select hosts of the IP address type and add them to the host group.
- Host Group Type set to Custom Identifier: You need to create identifiers for each host group and host. Hosts with an identifier will automatically be included in the corresponding host group sharing that identifier.
Constraints
To use the new host group management function, switch to the new access center. To go to the old host group management page, choose Access Center > Access Center in the navigation pane on the left and then click Back to Old Version in the upper right corner. The host group function (new) is not generally available. To use it, submit a service ticket.
Creating a Host Group (IP Address)
- Log in to the AOM 2.0 console.
- In the navigation pane, choose Settings > Global Settings.
- On the Global Settings page, choose Collection Settings > Host Groups and click Create Host Group in the upper left corner.
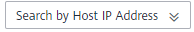
- On the displayed page, set the host group parameters.
Table 1 Parameters Parameter
Description
Example
Host Group
Name of a host group. Enter 1 to 64 characters. Do not start with a period (.) or underscore (_) or end with a period. Only letters, digits, hyphens (-), underscores, and periods are allowed.
IPHostGroup1
Host Group Type
Type of the host group. Options: IP and Custom Identifier. In this example, select IP.
IP
Host Type
Host type. Default: Linux.
Linux
Remark
Host group remarks. Enter up to 1,024 characters.
-
Figure 1 Creating an IP address host group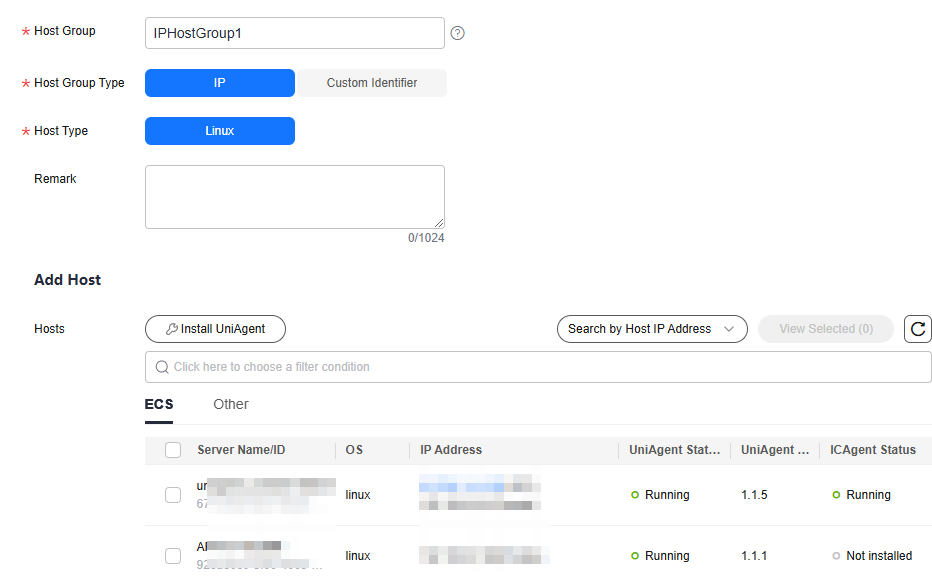
- In the host list, select one or more hosts to add to the group and click OK.
- You can filter hosts by host name/ID or private IP address. You can also click
 and enter multiple host IP addresses in the displayed search box to search.
and enter multiple host IP addresses in the displayed search box to search. - If your desired hosts are not in the list, click Install UniAgent. On the displayed page, install UniAgents on the hosts as prompted. For details, see (New) Installing UniAgents.
- When the selected hosts do not have UniAgent installed but have an earlier version of ICAgent installed, an upgrade prompt appears. To enable automatic UniAgent installation later, click Upgrade to first upgrade ICAgent to the latest version.
- If the selected hosts do not have both UniAgent and ICAgent installed (either UniAgent or ICAgent is in the Not installed state), click OK. A dialog box will pop up, indicating the missing UniAgent or ICAgent and the number of hosts without UniAgent or ICAgent installed.
- When selecting an ECS, click OK in the dialog box. The system will then issue a task for automatically installing either UniAgent or ICAgent. Otherwise, the host cannot be added to the host group.
- When selecting a host of the Other type, manually install UniAgent and ICAgent first. Otherwise, the host cannot be added to the host group. For details, see (New) Installing UniAgents.
- Click
 in the upper right corner of the host list to manually refresh the list.
in the upper right corner of the host list to manually refresh the list.
- You can filter hosts by host name/ID or private IP address. You can also click
Creating a Host Group (Custom Identifier)
- Log in to the AOM 2.0 console.
- In the navigation pane on the left, choose Settings > Global Settings. On the displayed page, choose Collection Settings > Host Groups and click Create Host Group in the upper left corner.
- On the displayed page, set the host group parameters.
Table 2 Parameters Parameter
Description
Example
Host Group
Name of a host group. Enter 1 to 64 characters. Do not start with a period (.) or underscore (_) or end with a period. Only letters, digits, hyphens (-), underscores, and periods are allowed.
HostGroup
Host Group Type
Type of the host group. Options: IP and Custom Identifier. In this example, select Custom Identifier.
Custom Identifier
Host Type
Host type. Default: Linux.
Linux
Remark
Host group remarks. Enter up to 1,024 characters.
-
Custom Identifier
Click Add to add a custom identifier. Max.: 128 characters. Only letters, digits, underscores (_), and hyphens (-) are allowed. Up to 10 custom identifiers can be added.
aom
Figure 2 Creating a custom identifier host group
- Click OK. After the host group is created, add hosts to it by referring to 5.
- Log in to the host and perform the following operations as the root user to create the custom_tag file for storing host tags.
- Run the cd /opt/cloud command.
- If the /opt/cloud directory already exists, navigate to it and run the mkdir lts command to create the lts directory in it.
- If the /opt/cloud directory does not exist, run the mkdir /opt/cloud/ command to create it and enter it, and then run the mkdir lts command to create the lts directory.
- Run the chmod 750 lts command to modify the permission on the lts directory.
- Run the touch custom_tag command in the lts directory to create the custom_tag file.
- Run the chmod 640 custom_tag;vi custom_tag command to modify the custom_tag file permission and open the file.
- Press i to enter the insert mode, enter a custom identifier, press Esc, enter :wq!, save the modification and exit.
- Use either of the following methods to add a host to the custom identifier host group:
- Run the cd /opt/cloud command.
Other Operations
You can change a created host group, add hosts to or remove hosts from a host group, or associate a host group with log ingestion configurations.
|
Operation |
Procedure |
|---|---|
|
Changing a host group |
|
|
Adding hosts to a host group |
This operation is not supported for hosts in a custom identifier host group. To add hosts to a custom identifier host group, refer to 5. |
|
Removing a host from a host group |
This operation is not supported for hosts in a custom identifier host group. |
|
Removing hosts in batches |
This operation is not supported for hosts in a custom identifier host group. |
|
Viewing log ingestion rules |
For how to configure log ingestion rules for the host group, see Managing Metric and Log Ingestion. |
|
Viewing metric access rules |
|
|
Associating a host group with an ingestion configuration |
|
|
Disassociating a host group from an ingestion configuration |
|
|
Disassociating a host group from multiple ingestion configurations |
|
|
Copying host group information |
Hover your cursor over a host group name to copy a host group ID. |
|
Deleting a host group |
|
|
Deleting host groups in batches |
|
|
Managing tags |
Tag log groups as required.
Precautions:
|
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot