Why Am I Unable to Connect to a Port on an ECS?
Scenarios
A connection to an ECS on a specific port may be prevented for multiple reasons, for example, a security group is blocking traffic to the port.
This section uses port 80 as an example to describe how to troubleshoot an unreachable ECS port.
Fault Locating
If the ECS cannot provide the HTTP service, check whether the port used by the web service (TCP port 80 by default) is working properly.
- On the ECS management console, ensure that the port is permitted in the security group.
- Remotely log in to the ECS and ensure that HTTP is enabled on it.
- Ensure that the port is listened to properly. If it is not, change the listened IP address.
- Ensure that HTTP is permitted on the ECS firewall.
Windows
The following uses an ECS running Windows Server 2012 with Internet Information Services (IIS) deployed as an example.
- Ensure that port 80 is permitted in the security group.
- Log in to the management console.
- Click
 in the upper left corner and select your region and project.
in the upper left corner and select your region and project. - Under Compute, choose Elastic Cloud Server.
- On the Elastic Cloud Server page, click the name of the target ECS.
The page providing details about the ECS is displayed.
- Click the Security Groups tab and view security group rules.
- Make sure that the following security group rules have been added to the security group which the ECS belongs to.
Figure 1 Security group rules
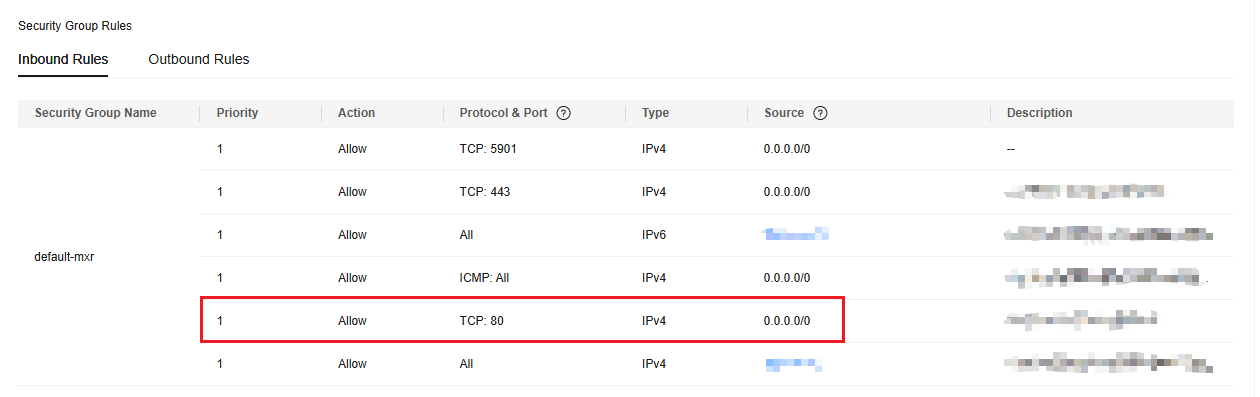
- Remotely log in to the ECS and verify that IIS is enabled on it.
- In the Server Manager window, choose Tools > Internet Information Services (IIS) Manager.
If this option is unavailable, IIS is not successfully deployed. In such a case, deploy IIS again.
- In the Internet Information Services (IIS) Manager window, check the following information:
- In the Connections navigation pane, right-click the ECS ID. If Connect is unavailable, IIS has been enabled.
- Click Sites. Then, view the website status on the right side of the page. If the website is stopped, click the website and then Start under Manage Server on the right side of the page to start the website.
- In the Server Manager window, choose Tools > Internet Information Services (IIS) Manager.
- Check whether the port is properly listened to on the ECS.
Open the cmd window and run the following command:
netstat -ano | findstr: 80
If information similar to the following is displayed, port 80 is being properly listened to on the entire network. If it is not, change the listened IP address.

- Ensure that HTTP is permitted on the firewall.
- Choose Control Panel > Windows Firewall.
- Perform operations based on the firewall status.
- If the firewall is disabled, no further action is required.
- If the firewall is enabled, perform the following operations:
- Click Advanced settings.
- In the navigation pane, click Inbound Rules.
- Select World Wide Web Services (HTTP Traffic-In). If it is disabled, enable the rule.
Linux
The following uses an ECS running CentOS 7 with Nginx deployed as an example.
- Ensure that port 80 is permitted in the security group.
- Log in to the management console.
- Click
 in the upper left corner and select your region and project.
in the upper left corner and select your region and project. - Under Compute, choose Elastic Cloud Server.
- On the Elastic Cloud Server page, click the name of the target ECS.
The page providing details about the ECS is displayed.
- Click the Security Groups tab and view security group rules.
- Make sure that the following security group rules have been added to the security group which the ECS belongs to.
Figure 2 Security group rules
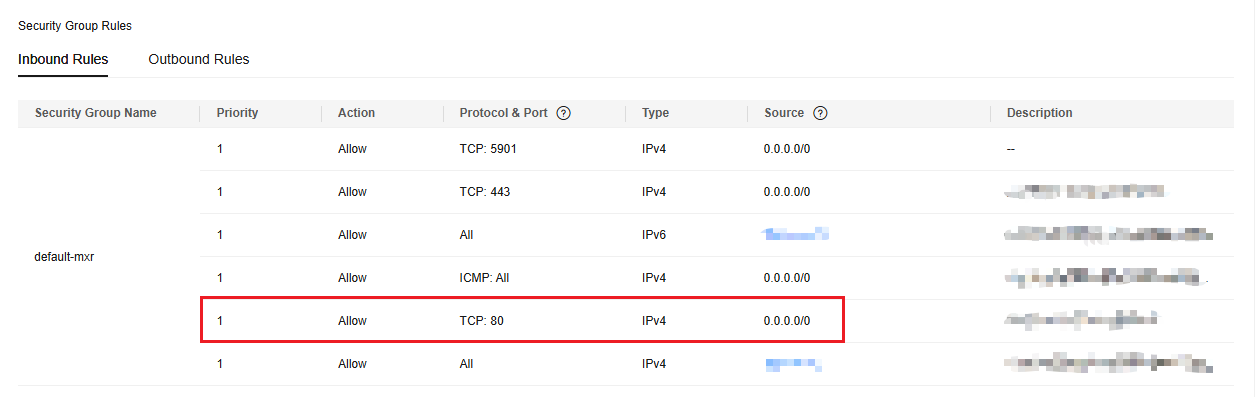
- Remotely log in to the ECS and ensure that Nginx is enabled on it.
Run the following command to check whether Nginx has been enabled:
systemctl status nginx
If the following information is displayed, Nginx has been enabled:

If Nginx has not been enabled, run the following command to enable it:
systemctl start nginx
- Run the following command to check whether the port is properly listened to on the ECS:
netstat -an | grep 80
If information similar to the following is displayed, port 80 is being properly listened to on the entire network. If it is not, change the listened IP address.
tcp 0 0 0.0.0.0:80 0.0.0.0:* LISTEN
- View the iptables rules of the ECS firewall.
- Run the following command to view the firewall status:
or
firewall-cmd --state
- If the firewall is disabled, run the following command to enable it:
If "Failed to start firewalld.service: Unit is masked." is displayed after the command is executed, run the following command and then run the preceding command to enable the firewall again:
systemctl unmask firewalld
- Run the following command to view the allowed ports:
- Run the following command to allow TCP port 80:
- Run the following command to update the firewall rules:
- Run the following command to view the firewall status:
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





