What Is NAT Gateway?
NAT Gateway is a network address translation (NAT) service. It can be a public NAT gateway or a private NAT gateway.
Video Tutorial
This video introduces what NAT Gateway is.
Public NAT Gateways
A public NAT gateway enables cloud and on-premises servers in a private subnet to share an EIP to access the Internet or provide services accessible from the Internet. Cloud servers are ECSs and BMSs in a VPC. On-premises servers are servers in on-premises data centers that connect to a VPC through Direct Connect or Virtual Private Network (VPN). A public NAT gateway supports up to 20 Gbit/s of bandwidth.
Public NAT gateways offer source NAT (SNAT) and destination NAT (DNAT).
- SNAT translates private IP addresses into EIPs so that traffic from a private network can go out to the Internet.
Figure 1 shows how an SNAT rule works.
- DNAT enables servers in a VPC, regardless of if they are in the same AZ, to share an EIP to provide services accessible from the Internet. With an EIP, a public NAT gateway forwards the Internet requests from only a specific port and over a specific protocol to a specific port of a server, or it can forward all requests to the server regardless of which port they originated on.
Figure 2 shows how a DNAT rule works.
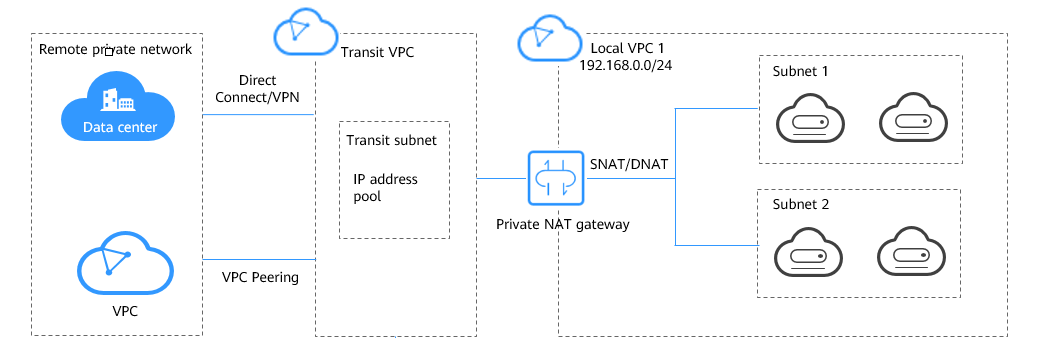
Private NAT Gateways
Private NAT gateways provide network address translation, allowing ECSs and BMSs in a VPC to communicate with servers in other VPCs or on-premises data centers. You can configure SNAT and DNAT rules for a NAT gateway to translate the source and destination IP addresses of originating packets into a transit IP address.
Specifically,
- SNAT enables servers in a VPC, regardless of if they are in the same AZ, to share a transit IP address to access on-premises data centers or other VPCs.
- DNAT enables servers in a VPC, regardless of if they are in the same AZ, to share the same transit IP address to provide services accessible from on-premises data centers or other VPCs.
Transit Subnet
A transit subnet is a transit network and is the subnet to which the transit IP address belongs.
Transit IP Address
A transit IP address is a private IP address that can be assigned from a transit subnet. Cloud servers in your VPC can share a transit IP address to access on-premises networks or other VPCs.
Transit VPC
A transit VPC is where a transit subnet belongs to.
How Do I Access the NAT Gateway Service?
- Management console
Log in to the management console and choose NAT Gateway from the service list.
- APIs
If you need to integrate NAT Gateway on the cloud platform into your own system, use APIs to access NAT Gateway. For details, see NAT Gateway API Reference.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot







