Verifying Log Collection
Scenarios
This topic describes how to verify that third-party logs can be forwarded to SecMaster.
|
Scenario |
Verification Method |
|---|---|
|
Enabling SecMaster to collect logs |
Go to the page on the SecMaster console and check whether there are logs of cloud services with log access enabled. |
|
Transferring logs from SecMaster to a third-party system or product |
Go to the third-party system or product and check whether forwarded logs have been received successfully. |
|
Ingesting third-party logs into SecMaster |
Verify the log access by referring to this section. |
Verifying Log Collection
- View data in the collection channel on the SecMaster console.
- Log in to the management console.
- Click
 in the upper part of the page and choose Security > SecMaster.
in the upper part of the page and choose Security > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace.
- In the navigation pane on the left, choose . Then, select the Collection Channels tab.
- On the Collection Channels tab, click the setting button in the upper right corner of the table and select Received and Sent.
- In the table, view the monitoring information of the corresponding collection channel. If there is data in the Received and Sent columns, the log access is successful.
- Check data in the security analysis log pipeline on the SecMaster console.
- In the navigation pane on the left, choose .
Figure 1 Accessing the Security Analysis tab
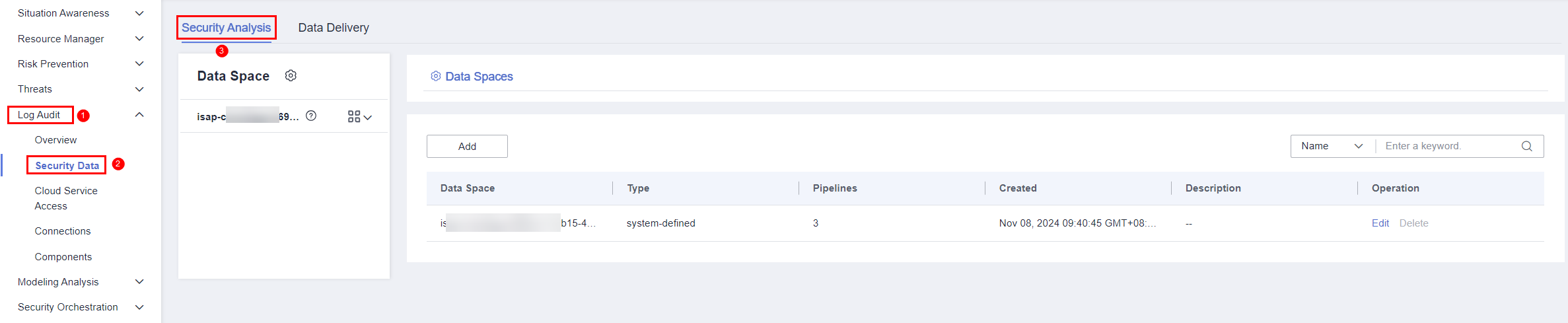
- In the data space navigation tree on the left, click a data space name to show the pipeline list. Click the name of the target pipeline. The pipeline data search page is displayed on the right.
- If data is displayed in the log pipeline, the log access is successful.
- In the navigation pane on the left, choose .
- View data in the security data table on the SecMaster console.
- In the navigation pane on the left, choose .
- On the Tables page, click the name of the target index data table to go to the query and analysis page.
- If data is displayed on the data table query and analysis page, the log access is successful.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





