What Are the Differences Between IAM and Enterprise Management?
Enterprise Management enables enterprises to manage cloud resources at the organization and project levels. Enterprise Management mainly provides project management, personnel management, and resource management.
Identity and Access Management (IAM) is an identity management service that provides identity authentication, permissions management, and access control.
Both IAM and Enterprise Management can be used to manage users and access permissions. However, Enterprise Management supports more fine-grained resource permissions management than IAM. Enterprise Management is recommended for medium- and large-sized enterprises.
For more information about IAM features, see Identity and Access Management User Guide.
Differences Between IAM and Enterprise Management
- Enabling method
- IAM can be used free of charge immediately upon successful account registration.
- Enterprise Management can be used free of charge immediately upon successful account registration.
- Resource isolation
- Using IAM, you can create multiple projects in a region to isolate resources, and authorize users to access resources in specific projects.
- Using Enterprise Management, you can create enterprise projects to isolate resources across regions. Enterprise Management makes it easy to assign permissions for specific cloud resources. For example, you can add an Elastic Cloud Server (ECS) to an enterprise project, and assign permissions to a user for it to manage the ECS in the project. The user then can manage only this ECS.
Relationship Between Enterprise Management and IAM
- The functions of creating users and user groups are synchronous between IAM and Enterprise Management.
- The function of granting permissions to user groups in Enterprise Management is subject to the fine-grained IAM authorization. If the system-defined policies cannot meet your requirements, you can create custom policies in IAM. The custom policies will then be synchronized to Enterprise Management and can be associated with user groups in the two services.
- If a user group is granted permissions in both IAM and Enterprise Management, users in the group get permissions from the policies attached to the group in the two services. Requests of these users will then be authenticated based on the actions in the associated policies.
- If the attached policies contain the same action, the effect of the action in IAM takes the priority. For example, when a user requests for creating a cloud server, the Deny effect defined in IAM is applied. Therefore, the user cannot create cloud servers.
A policy attached in an IAM project contains the following action: { "Action": [ "ecs:cloudServers:create" ], "Effect": "Deny" } A policy attached in an enterprise project contains the following action: { "Action": [ "ecs:cloudServers:create" ], "Effect": "Allow" } - All different actions in the policies attached in IAM and Enterprise Management will take effect. The following are two actions that allow users to create and delete cloud servers.
A policy attached in an IAM project contains the following action: { "Action": [ "ecs:cloudServers:create" ], "Effect": "Allow" } A policy attached in an enterprise project contains the following action: { "Action": [ "ecs:cloudServers:delete" ], "Effect": "Allow" }
- If the attached policies contain the same action, the effect of the action in IAM takes the priority. For example, when a user requests for creating a cloud server, the Deny effect defined in IAM is applied. Therefore, the user cannot create cloud servers.
Authentication Process
When a user initiates an access request, the system authenticates the request based on the actions in the policies attached to the group to which the user belongs. The following figure shows the authentication process.
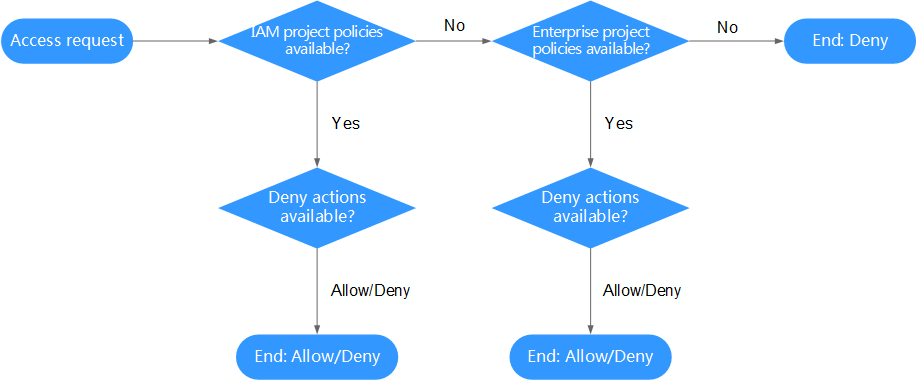
- A user initiates an access request.
- The system looks for IAM project policies and then looks for matched actions in the policies.
- If a matched Allow or Deny action is found, the system returns an authentication result (Allow or Deny). Then the authentication is finished.
- If no matched actions are found in IAM project policies, the system continues to look for enterprise project policies and matched actions.
- If a matched Allow or Deny action is found, the system returns an authentication result (Allow or Deny). Then the authentication is finished.
- If no matched actions are found, the system returns a Deny. Then the authentication is finished.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





