What Are Regions and AZs?
Concepts
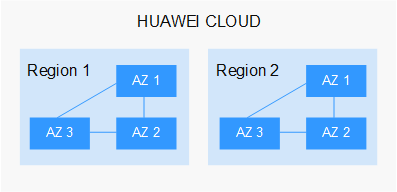
A region and availability zone (AZ) identify the location of a data center. You can create resources in a specific region and AZ.
- Regions are divided from the dimensions of geographical location and network latency. Public services, such as Elastic Cloud Server (ECS), Elastic Volume Service (EVS), Object Storage Service (OBS), Virtual Private Cloud (VPC), Elastic IP (EIP), and Image Management Service (IMS), are shared within the same region. Regions are classified as universal regions and dedicated regions. A universal region provides universal cloud services for common tenants. A dedicated region provides services of the same type only or for specific tenants.
- An AZ contains one or more physical data centers. Each AZ has independent cooling, fire extinguishing, moisture-proof, and electricity facilities. Within an AZ, computing, network, storage, and other resources are logically divided into multiple clusters. AZs within a region are interconnected using high-speed optical fibers to allow you to build cross-AZ high-availability systems.
Figure 1 shows the relationship between the regions and AZs.
Huawei Cloud provides services in many regions around the world. You can select a region and AZ as needed.
Selecting a Region
- Location
You are advised to select a region close to you or your target users. This reduces network latency and improves access rate.
- If you or your users are in the Asia Pacific region and outside the Chinese mainland, select the CN-Hong Kong, AP-Bangkok, or AP-Singapore region.
- If you or your users are in Africa, select the AF-Johannesburg region.
- If you or your users are in Latin America, select the LA-Santiago region.
- Resource price
Resource prices may vary in different regions. For details, see Product Pricing Details.
Selecting an AZ
When determining whether to deploy resources in the same AZ, consider your applications' requirements on disaster recovery (DR) and network latency.
- For high DR capability, deploy resources in different AZs in the same region.
- For low network latency, deploy resources in the same AZ.
Regions and Endpoints
Before using an API to call resources, specify its region and endpoint. For more details, see Regions and Endpoints.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot