Using the RangerKMS Native UI to Manage Permissions and Keys
Scenario
After KMS is installed, you need to create a user on FusionInsight Manager and associate the user with the KeyAdmin role to grant it the permission to manage keys and encrypt HDFS partitions.
If it is your first time logging in to the RangerKMS UI, you can log in as user rangerkms or keyadmin. By default, the keyadmin user has only the key management permission. User rangerkms has both key management permission and key operation permission.
This section applies to MRS 3.3.0-LTS or later.
Prerequisites
- The Ranger service has been installed and is running properly.
- You have created a human-machine user and do not need to add permission.
Adding the KeyAdmin Role to a User
- Log in to FusionInsight Manager as user admin. Choose Cluster > Services > Ranger.
- Click RangerAdmin in the Basic Information area. The Ranger web UI is displayed.
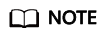
- On the Ranger web UI, click the username in the upper right corner, and choose Log Out to log out of the current user.
- Log in to the system again as user rangerkms or keyadmin. The default password of user rangerkms is Rangerkms@123, and that of user keyadmin is Keyadmin@123. Change the password upon the first login.
- Choose Settings > Users. In the User Name column, click the user to whom you want to assign the KeyAdmin role permission.
- Select KeyAdmin from the Select Role drop-down list box. In the dialog box that is displayed, click OK.
- Click Save. The KeyAdmin role is added.
Key Permission Management
- Log in to the Ranger UI as rangerkms, keyadmin, or a user with the KeyAdmin role.
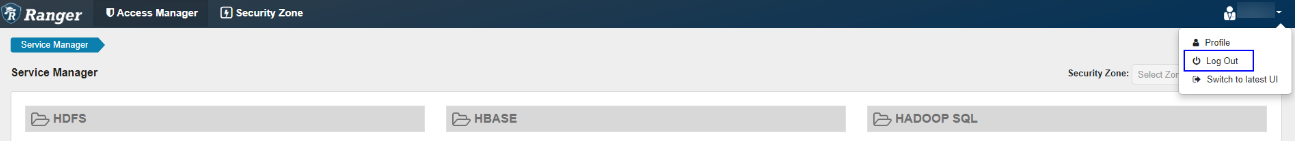
- On the Access Manager page, click kmsdev.
- You can click Add New Policy in the upper right corner to add a policy.
- Configure the parameters listed in the table below based on service requirements.
Table 1 Parameters for adding a new policy Parameter
Description
Policy Type
Access
Policy Name
Policy name, which is mandatory.
Policy Label
Policy label, which is used to classify policies.
Key Name
Key name and EZK name stored in KMS. This policy takes effect for the configured key. If this parameter is set to *, all keys are selected.
Description
Content of a policy.
Audit Logging
Audit function.
Allow Conditions
Allow policy to grant permissions to selected users, user groups, or roles. Available key words are as follows:
- Create: Create a key.
- Delete: Delete a key.
- Rollover: Update a key.
- Set Key Material: Set the key ciphertext.
- Get: Read a key.
- Get keys: Read all keys (keys configured in the policy).
- Get Metadata: Get the metadata of a key.
- Generate EEK: Generate an EEK.
- Decrypt EEK: Decrypt an EEK.
Exclude from Allow Conditions: Configure exception rules.
Deny All Other Accesses
Whether to reject all other access requests.
- True: All other access requests are rejected.
- False: Deny Conditions can be configured.
Deny Conditions
Policy rejection condition, which is used to configure the permissions and exceptions to be denied in the policy. The configuration method is similar to that of Allow Conditions.
The priority of Deny Conditions is higher than that of allowed conditions configured in Allow Conditions.
Exclude from Deny Conditions: exception rules excluded from the denied conditions
- Click Add. The role, user group, or user corresponding to the policy has the key-related permissions in the policy.
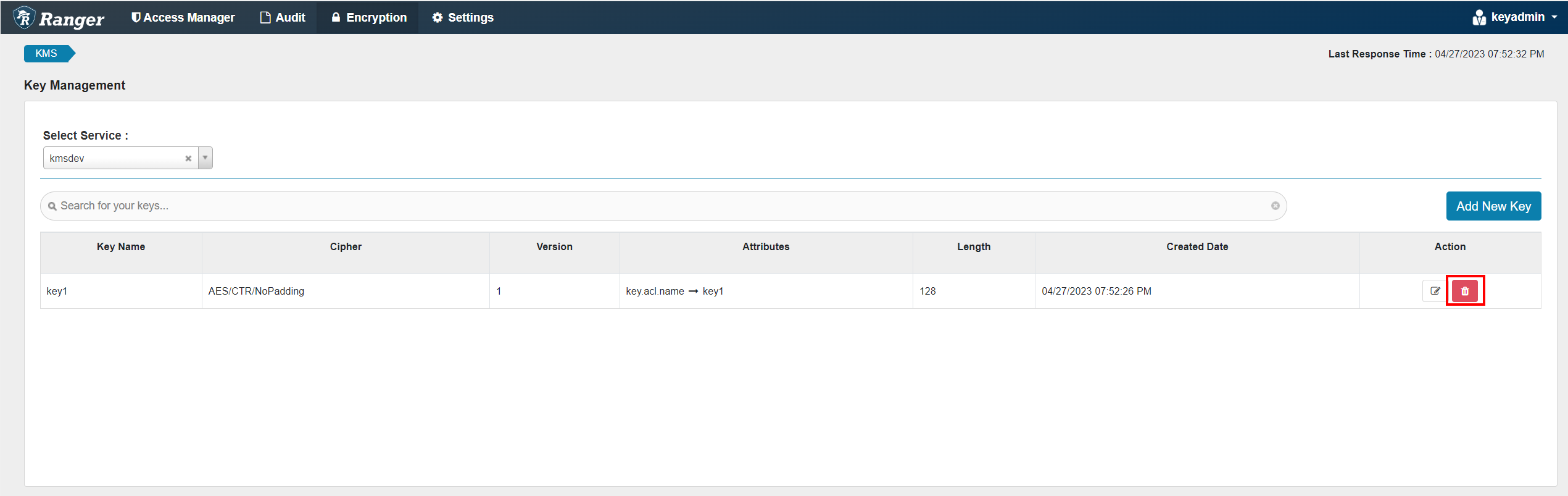
Managing Keys on the Native UI
- Log in to the Ranger management page as user rangerkms or keyadmin.
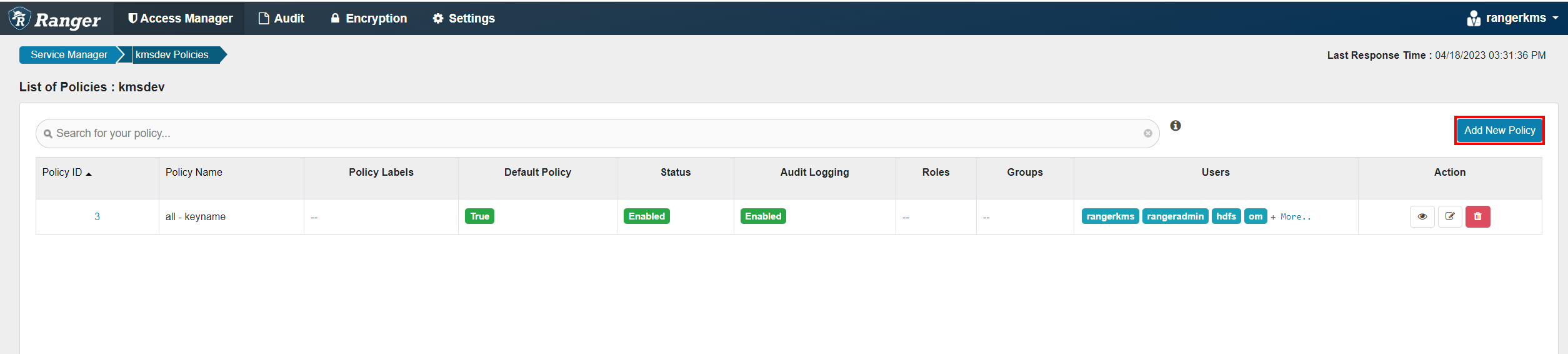
- Click Encryption. The key management page is displayed.
- Select kmsdev from the Select Service drop-down list.
- Click Add New Key on the right to create a key.
Table 2 Parameters on the Add New Key page Parameter
Description
Key Name
Key name.
Cipher
Encryption algorithm. The default value is AES/CTR/NoPadding and cannot be changed.
Length
Key length. The value can be 128 or 256.
Description
Content of a key.
Attributes
Custom attribute of the key. You do not need to add any attributes.
- Click the modification icon to update a key.
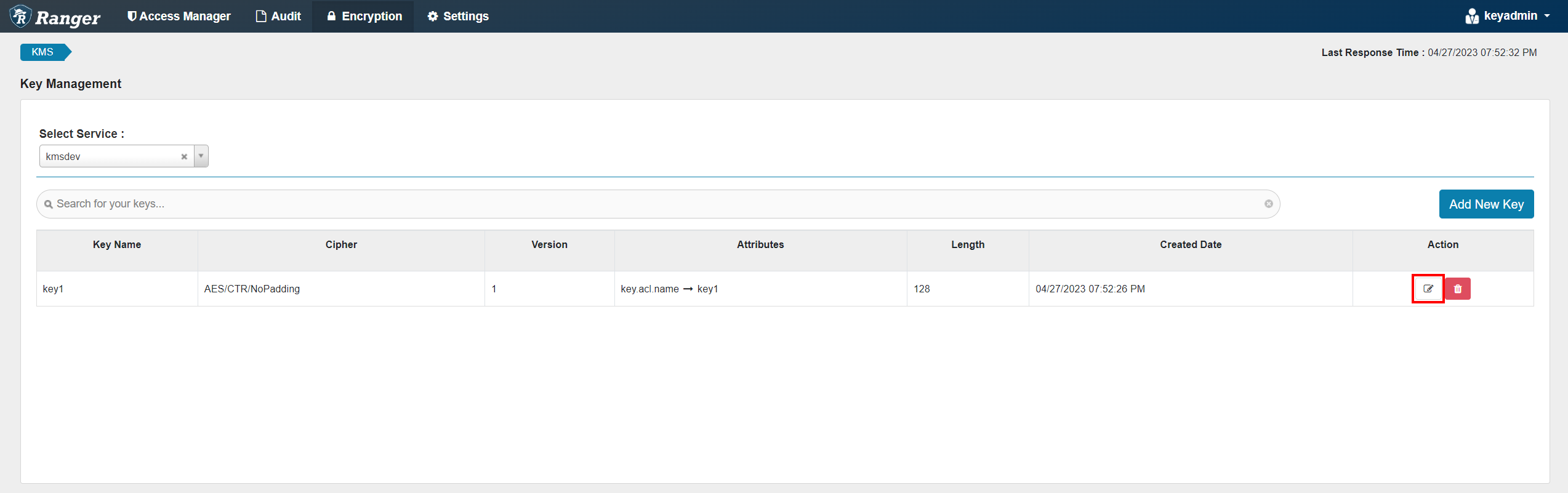
- If you need to delete a key, click the delete icon.
Permission Management for Common Clusters
- Log in to FusionInsight Manager, choose Cluster > Services > Ranger, click Configurations > RangerKMS, and click Customizations.
- Add the following parameter to the dbks-site.xml line:
hadoop.kms.security.authorization.manager and empty value
- Save the configuration and restart RangerKMS.
- If the key management permission is required, add the user to the rkmsadmin group.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





