Handling False Alarms to Get Improved Basic Web Protection
After you connect your website to Web Application Firewall (WAF) and enable basic web protection, WAF detects and blocks requests that match the rules you configured. If a normal request matches a basic web protection rule and is blocked by WAF, you can handle the event as false alarm. In this way, WAF will no longer block the same type of request.
Prerequisites
You can view false alarm events on the Events page.
Constraints
An event can only be handled as a false alarm once.
Application scenarios
Sometimes normal service requests may be blocked by WAF. For example, suppose you deploy a web application on an ECS and then add the public domain name associated with that application to WAF. If you enable basic web protection for that application, WAF may block the access requests that match the basic web protection rules. As a result, the website cannot be accessed through its domain name. However, the website can still be accessed through the IP address. In this case, you can handle the false alarms to allow normal access requests to the application.
Impact on the System
- The event will not be displayed on the Events page and you will not receive any alarm notifications about the event.
- If an event is handled as a false alarm, the rule hit will be added to the global protection whitelist rule list. You can go to the Policies page and then switch to the Global Protection Whitelist page to manage the rule, including querying, disabling, deleting, and modifying the rule.
Procedure
- Log in to the management console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - Click
 in the upper left corner and choose Web Application Firewall under Security & Compliance.
in the upper left corner and choose Web Application Firewall under Security & Compliance. - In the navigation pane on the left, choose Events.
- In the event list, search for false alarms by protected website, event type, source IP address, and URL.
Figure 1 Events
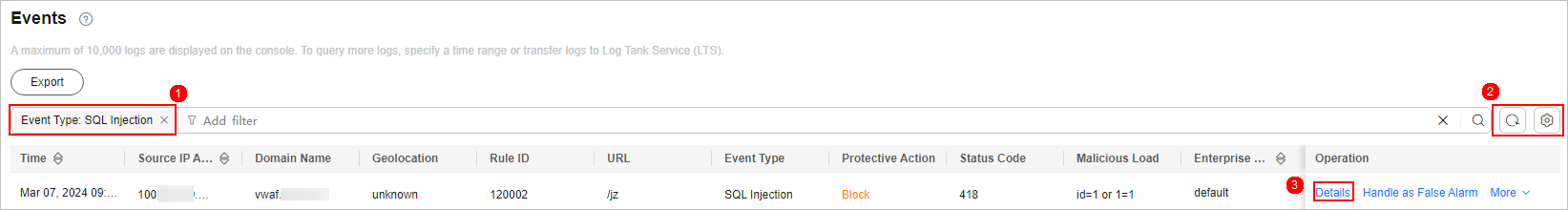
- In the Operation column of an event you consider as a false alarm, click Details. On the displayed page, confirm that the event is a false alarm.
Figure 2 Event Details

- In the row containing the event, click Handle as False Alarm.
- In the displayed dialog box, add a false alarm handling policy.
Figure 3 Add Global Protection Whitelist Rule

Verification
A false alarm will be deleted within about a minute after the handling configuration is done. It will no longer be displayed in the event list. You can clear the cache, refresh the browser, and access the page again to verify whether the false alarm was successfully handled. If the requested page responds normally, the configuration takes effect.
Basic Web Protection Check Items
WAF basic web protection defends against common Open Web Application Security Project (OWASP) security threats. WAF uses built-in semantic analysis and regular expression engines for basic web protection to detect and block threats such as malicious scanners, IP addresses, and web shells. You can enable all protection rules in basic web protection or only the ones you want. For details, see Table 1.
Type |
Description |
|---|---|
General Check |
Defends against attacks such as SQL injections, XSS, remote overflow vulnerabilities, file inclusions, Bash vulnerabilities, remote command execution, directory traversal, sensitive file access, and command/code injections. SQL injection attacks are mainly detected based on semantics.
NOTE:
If you enable General Check, WAF checks your websites based on the built-in rules. |
Webshell Detection |
Protects against web shells from upload interface.
NOTE:
If you enable Webshell Detection, WAF detects web page Trojan horses inserted through the upload interface. |
Deep Inspection |
Identifies and blocks evasion attacks, such as the ones that use homomorphic character obfuscation, command injection with deformed wildcard characters, UTF7, data URI scheme, and other techniques.
NOTE:
If you enable Deep Inspection, WAF detects and defends against evasion attacks in depth. |
Header Inspection |
This function is disabled by default. When it is disabled, General Check will check some of the header fields, such as User-Agent, Content-type, Accept-Language, and Cookie.
NOTE:
If you enable this function, WAF checks all header fields in the requests. |
Shiro Decryption Check |
This function is disabled by default. After this function is enabled, WAF uses AES and Base64 to decrypt the rememberMe field in cookies and checks whether this field is attacked. There are hundreds of known leaked keys included and checked for.
NOTE:
If your website uses Shiro 1.2.4 or earlier, or your website uses Shiro 1.2.5 or later but no AES keys are not configured, it is strongly recommended that you enable Shiro decryption detection to prevent attackers from using leaked keys to construct attacks. |
Basic Web Protection Levels
WAF provides three basic web protection levels, Low, Medium, and High. The default level is Medium. The lower the protection level, the higher the false negative rate and the lower the false positive rate. For details, see Table 2.
Protection Level |
Description |
|---|---|
Low |
WAF only blocks the requests with obvious attack signatures. If a large number of false alarms are reported, Low is recommended. |
Medium |
The default level is Medium, which meets a majority of web protection requirements. |
High |
WAF blocks the requests with no attack signature but have specific attack patterns. High is recommended if you want to block SQL injection, XSS, and command injection attacks. |
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot








