Limiting Accesses Through IP Address-based Rate Limiting
If no proxy is used between WAF and web visitors, limiting source IP addresses is an effective way to detect attacks. IP address-based rate limiting rules are recommended.
Use Cases
Attackers use several hosts to continuously send HTTP POST requests to website www.example.com. Those malicious requests will use up website resources, such as the website connections and bandwidth. As a result, the website fails to respond to normal requests and its competitiveness decreases sharply.
Protective Measures
- Based on the access statistics, check whether a large number of requests were sent from a specific IP address. If yes, it is likely that the website was hit by CC attacks.
- Log in to the management console and route website traffic to WAF. For details about how to connect a domain name to WAF, see Adding a Domain Name.
- In the Policy column of the row containing the target domain name, click the number of enabled protection rules. On the displayed Policies page, keep the Status toggle on (
 ) for CC Attack Protection.
Figure 1 CC Attack Protection configuration area
) for CC Attack Protection.
Figure 1 CC Attack Protection configuration area
- Then, add a CC attack protection rule to limit the rate of request traffic destined for the domain name. Set Rate Limit Mode to Per IP address, Rate Limit based on your service features, and Protective Action to Verification code to prevent blocking legitimate users.
- Rate Limit Mode: Select Source and then Per IP address to distinguish a single web visitor based on IP addresses.
- Rate Limit: Number of requests allowed from a web visitor in the rate limiting period. The visitor's access request is denied if the limit is reached.
- Protective Action: To prevent legitimate requests from being blocked, select Verification code.
Verification code: A verification code is required if your website visitor's requests reaches Rate Limit you configured. WAF allows requests that trigger the rule as long as the website visitors complete the required verification.
If the number of access requests exceeds the configured rate limit, the visitors are required to enter a verification code to continue the access.
- Set other parameters based on site requirements.
Figure 2 Per IP address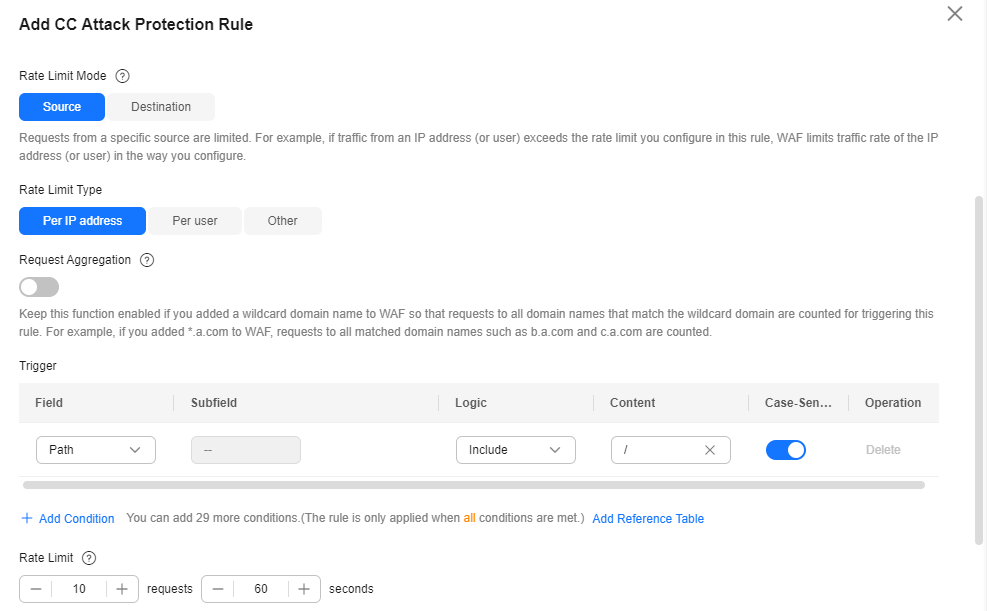
- In the navigation pane on the left, choose Events. You can view details about attack events.
Figure 3 Querying CC attack event logs

Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





