Adding an RDS Database
If you have granted permissions for accessing your database assets to DSC, purchased RDS DB instances, and created databases on the DB instances, you can follow the instructions described in this section to authorize permissions for performing relevant operations. Details are as follows:
- Grant the read-only permission: Only the sensitive data identification function can be used.
- Grant the read and write permission: The sensitive data identification and data anonymization functions can be used.
DSC cannot scan and mask sensitive data in MySQL databases which SSL has been enabled for on the RDS DB instance.
Prerequisites
- DSC has been allowed to access the database assets. For details, see Allowing or Disallowing Access to Cloud Assets.
- You have subscribed to RDS, and assets are available in RDS. There are available IP addresses in the corresponding subnet.
- The RDS DB instance is in the Normal state.
Procedure
- Log in to the management console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - In the navigation pane on the left, click
 and choose .
and choose . - In the navigation pane, choose Assets and select the Database tab and then the Unauthorized tab.
Figure 1 Unauthorized database assets

- In the row containing the desired RDS DB instance, click Authorize in the Operation column.
If you only need to authorize permissions for a single database in an RDS database instance, click
 on the left of instance. In the row containing the desired database, click Authorize in the Operation column.
on the left of instance. In the row containing the desired database, click Authorize in the Operation column. - In the displayed dialog box, set required parameters based on Table 1.
Figure 2 Batch permission authorization for databases
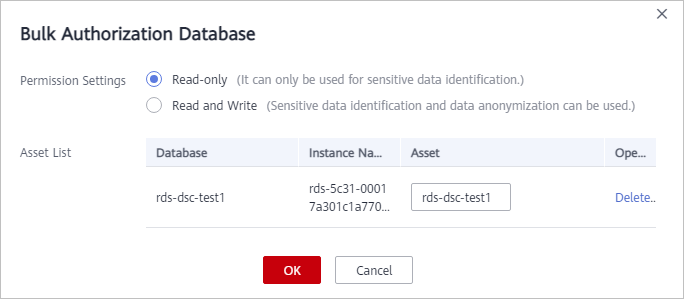
Table 1 Parameter description Parameter
Description
Permission Settings
- Read-only: It can only be used for sensitive data identification.
CAUTION:
After the RDS read-only permission is authorized, DSC creates an account dsc_readonly in RDS.
- After the password of the dsc_readonly account is reset in RDS, it will not be automatically synchronized to DSC. As a result, the sensitive data identification task fails. Therefore, do not reset the password of this account.
- If you have reset the password of dsc_readonly in RDS, delete the authorized RDS DB instance in DSC and re-authorize the instance.
- Read and Write: Sensitive data identification and data masking functions can be used.
Asset List
- If Read-only is selected for Permission Settings, you can change the names of the database assets to be authorized.
- If Read and Write is selected for Permission Settings, you can change the names of the database assets to be authorized. The usernames and passwords for accessing the databases must be configured.
- Read-only: It can only be used for sensitive data identification.
- Click OK. The authorized databases are displayed on the Authorized tab page.
Figure 3 Connectivity test
 DSC will check the connectivity of the added database, and the connectivity status of the added database is Checking.
DSC will check the connectivity of the added database, and the connectivity status of the added database is Checking.- If DSC can access the added database, the connectivity status is Succeeded.
- If the DSC cannot access the added database, the connectivity status Failed. Click Cause to view the failure cause.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





