Asset Security Screen
Scenarios
There are always such scenarios as presentation, reporting, or real-time monitoring where you need to present the analysis results of SecMaster on big screens to achieve better demonstration effect. It is not ideal to just zoom in the console. Now, SecMaster Large Screen is a good choice for you to display the service console on bigger screens for a better visual effect.
By default, SecMaster provides an asset screen for you. With this screen, you will learn about overall information about your assets at a glance, including how many assets you have, how many of them have been attacked, and how many of them are unprotected.
Prerequisites
You have enabled Large Screen. For details, see Buying Value-Added Packages.
Viewing the Asset Security Screen
- Log in to the SecMaster console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 1 Workspace management page

- In the navigation pane on the left, choose Situation Awareness > Large Screen. Figure 2 Large Screen
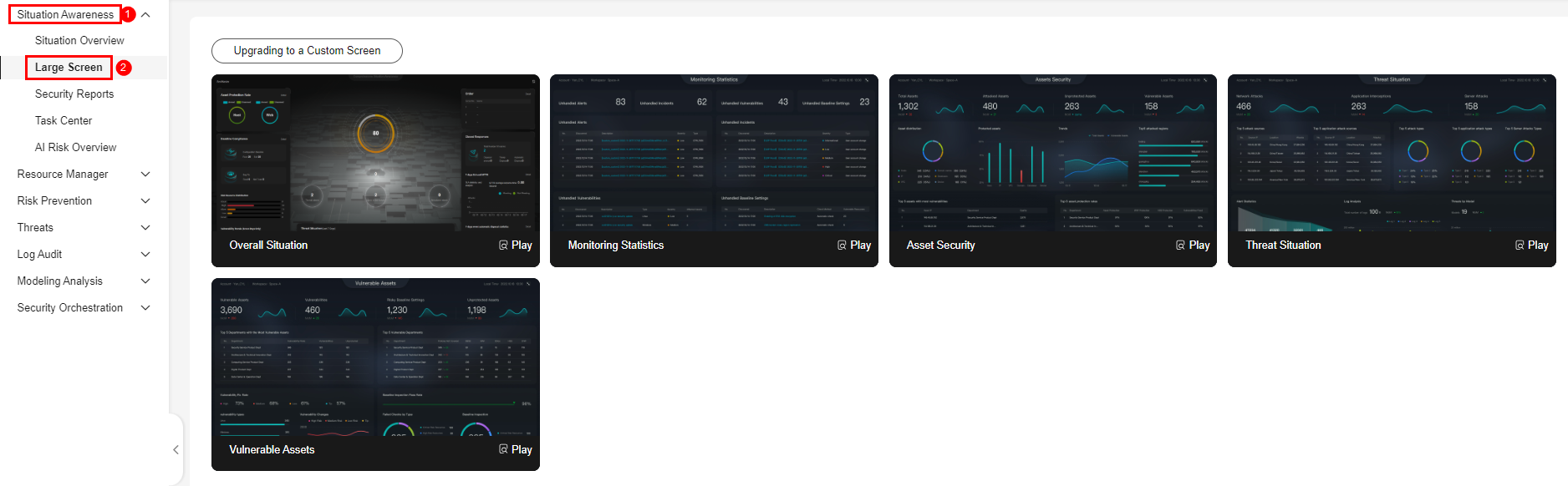
- Click Play in the lower right corner of the asset security image to access the screen.
This screen includes many graphs. More details are provided below.
Asset Security Screen Overview
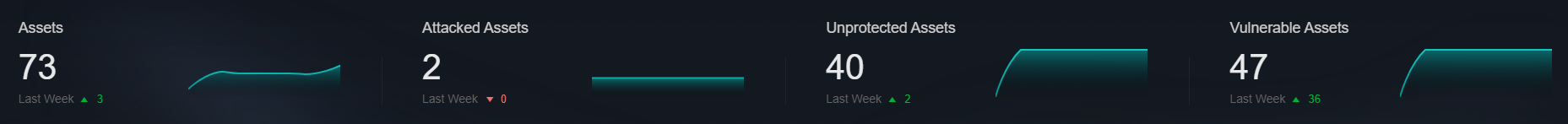
On this screen, as shown in Figure 3, you can view the total numbers of assets, attacked assets, unprotected assets, vulnerabilities, and assets with unsafe settings in the current workspace.
| Parameter | Statistical Period | Update Frequency | Description |
|---|---|---|---|
| Assets | Real-time | Hourly | Total number of assets managed in Resource Manager. |
| Attacked Assets | Last 7 days | Hourly | Number of assets affected by alerts aggregated in in the current workspace. |
| Unprotected Assets | Real-time | Hourly | Number of assets that are not protected by any security service; for example, ECSs that are not protected by HSS and EIPs that are not protected by DDoS. You will learn of how many assets with Protection Status marked as Unprotected in Resource Manager. In Resource Manager, the protection status for assets is as follows:
|
| Assets with Vulnerabilities or Unsafe Settings | Real-time | Hourly | These assets include assets affected by vulnerabilities and assets that have unsafe settings discovered during baseline inspection. The duplicated assets are counted only once. The vulnerability data comes from the Risk Prevention > Vulnerabilities page, and the baseline inspection data comes from the Risk Prevention > Baseline Inspection > Resources to Check page. |
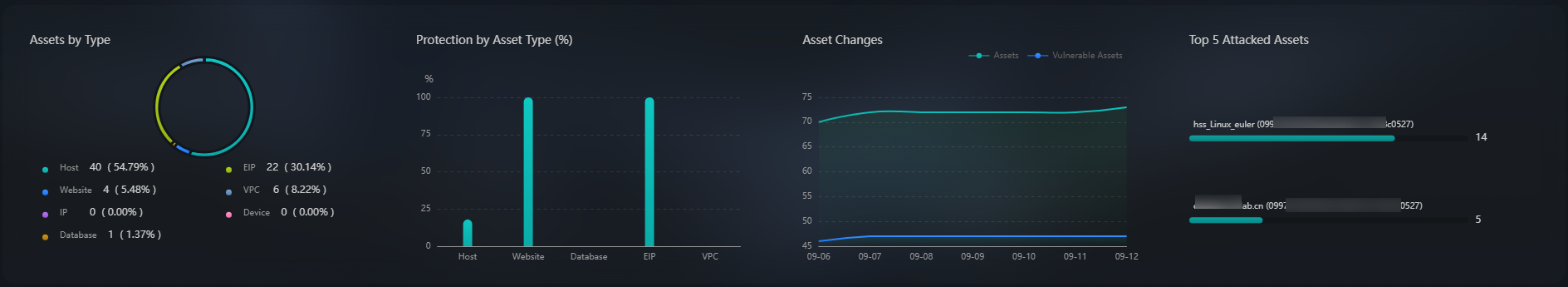
Asset Distribution
In this area, as shown in Figure 4, you can view assets by type, asset protection rate, asset change trend, and distribution of the five assets attacked most.
| Parameter | Statistical Period | Update Frequency | Description |
|---|---|---|---|
| Assets by Type | Real-time | Hourly | Number of different types of assets in Resource Manager. |
| Protection by Asset Type (%) | Real-time | Hourly | Percentage of protection for different types of assets. Protection rate of a certain type of assets = Protected assets/Total number of assets of this type. |
| Asset Changes | Last 7 days | Hourly | Statistics on the total number of assets, and the number of assets with vulnerabilities and unsafe settings in the last seven days. |
| Top 5 Attacked Assets | Last 7 days | Hourly | Top 5 attacked assets in the last seven days and the number of attacks. The data comes from the page. You can view details on this page. |
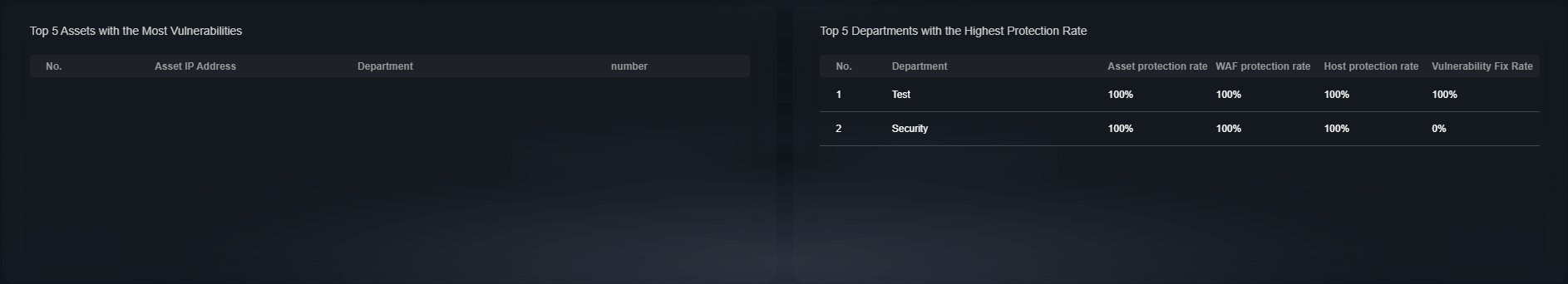
Top 5 Assets with the Most Vulnerabilities and Top 5 Departments with the Highest Protection Rate
In this area, as shown in Figure 5, you will see the five assets with the most vulnerabilities and the five departments with the highest protection rate.
| Parameter | Statistical Period | Update Frequency | Description |
|---|---|---|---|
| Top 5 Assets with the Most Vulnerabilities | Real-time | Hourly | Top 5 assets with the most vulnerabilities in different departments. This data is generated based on the assets affected by vulnerabilities in Risk Prevention > Vulnerabilities. Note that the assets must have department details provided, or the affected assets may fail to be counted toward this data. |
| Top 5 Departments with the Highest Protection Rate | Real-time | Hourly | This graph lists the five departments that have the highest protection rate, in descending order. Note that the assets on Resource Manager must have department details provided, or the assets cannot be counted toward this rate. |
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot