Managing Threat Intelligence Types
Scenario
This section describes how to manage threat intelligence types.
- Viewing Threat Intelligence Types: describes how to view existing threat intelligence types and their details.
- Adding a Threat Intelligence Type: describes how to create custom threat intelligence types.
- Associating a Threat Intelligence Type with a Layout: describes how to associate a custom threat intelligence type with an existing layout.
- Editing a Threat Intelligence Type: describes how to edit a custom threat intelligence type.
- Managing a Threat Intelligence Type: describes how to enable, disable, and delete a custom threat intelligence type.
Limitations and Constraints
- By default, built-in intelligence types are associated with existing layouts. You cannot customize associated layouts.
- Built-in intelligence types are enabled by default and cannot be edited, enabled, disabled, or deleted.
- After a user-defined threat intelligence type is added, the type ID cannot be modified.
Viewing Threat Intelligence Types
- Log in to the management console.
- Click
 in the upper part of the page and choose Security > SecMaster.
in the upper part of the page and choose Security > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace.
Figure 1 Workspace management page

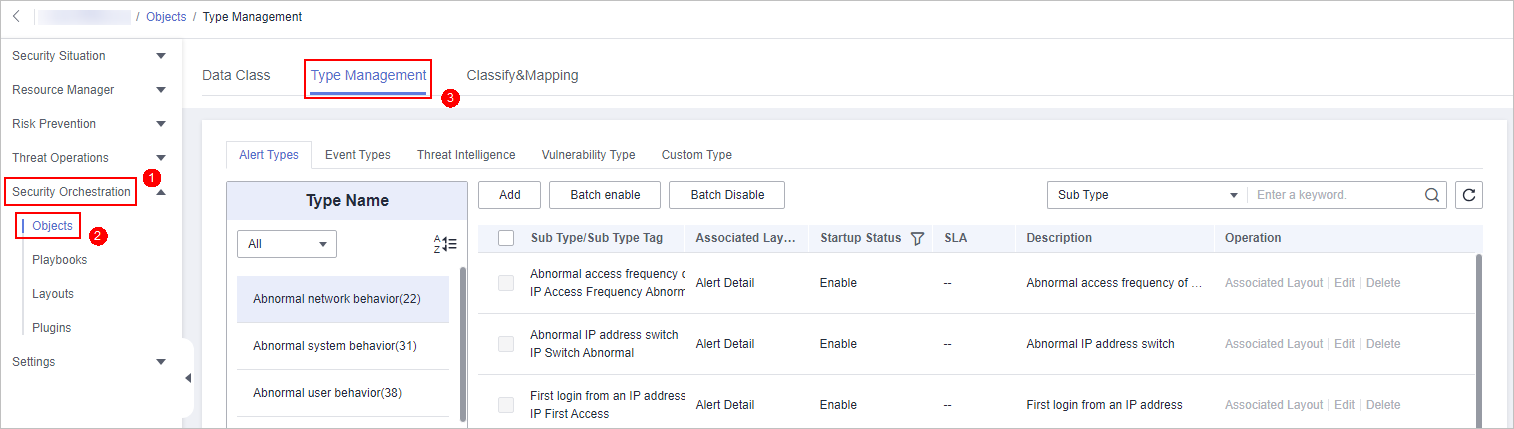
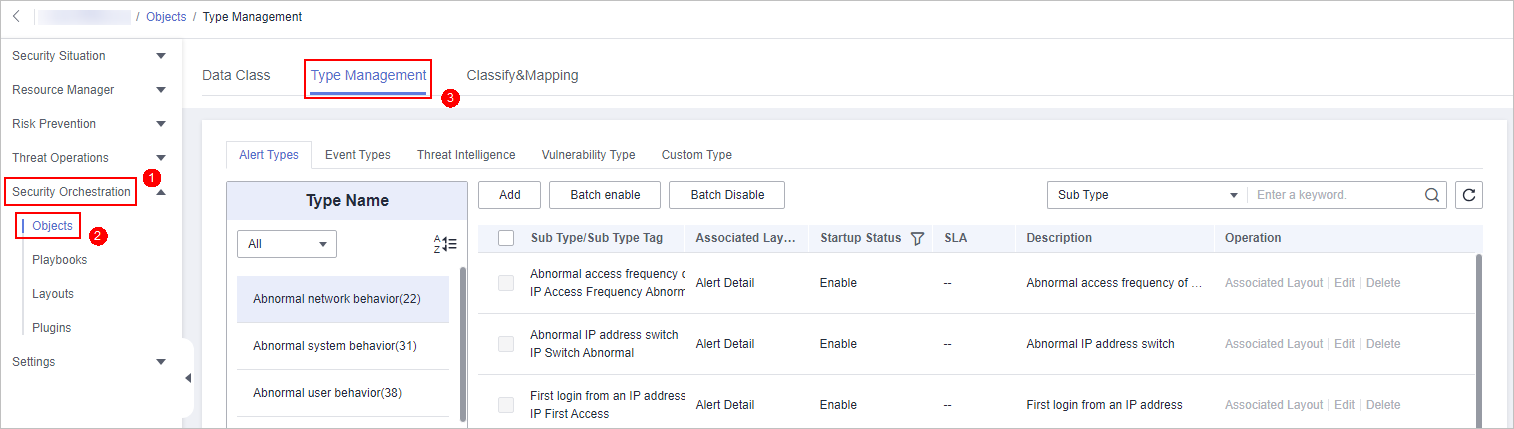
- In the navigation pane on the left, choose . On the displayed page, click the Type Management tab.
Figure 2 Type Management page
- On the Type Management page, click the Threat Intelligence tab.
- On the Threat Intelligence page, view details. For details about the parameters, see Table 1.
Table 1 Threat intelligence type parameters Parameter
Description
Type Name/Type Tag
Name and type tag of threat intelligence
Associated Layout
Layout associated with threat intelligence
Startup Status
Indicates the enabling status of a threat intelligence type:
- Enabled: The current type has been enabled.
- Disabled: The current type has been disabled.
Expired Time
Expiration time of threat intelligence.
Built-in
Indicates whether the threat intelligence is built in the system.
Description
Description of a threat intelligence
Operation
You can edit and delete the threat intelligence.
Adding a Threat Intelligence Type
- Log in to the management console.
- Click
 in the upper part of the page and choose Security > SecMaster.
in the upper part of the page and choose Security > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace.
Figure 3 Workspace management page

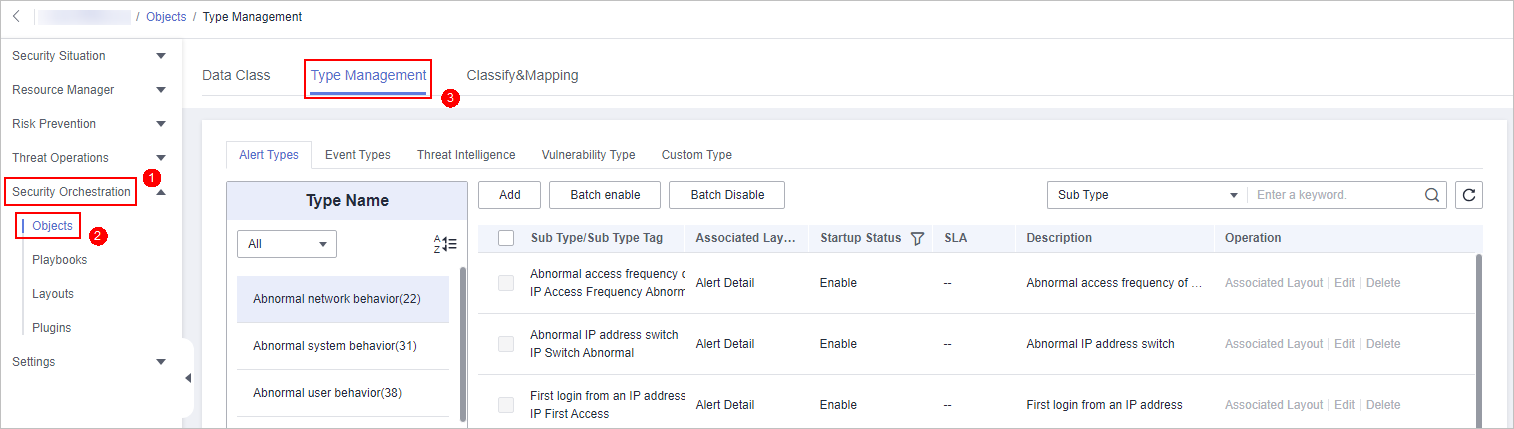
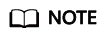
- In the navigation pane on the left, choose . On the displayed page, click the Type Management tab.
Figure 4 Type Management page
- On the Type Management page, click the Threat Intelligence tab.
- On the Threat Intelligence page, click Add. On the Add Threat Intelligence slide-out panel, set type parameters.
Table 2 Threat intelligence type parameters Parameter
Description
Type Name
Name of the threat intelligence to be added.
Type Tag
Enter the threat intelligence type ID. The keyword must comply with the upper camel case naming rules, for example, TypeTag.
Startup Status
Set the enabling status of a threat intelligence.
Expired Time
Set the expiration time of threat intelligence.
- Never Expire: The current intelligence type never expires.
- Time Interval: Set the interval for invalidating intelligence.
Description
Description of a custom threat intelligence
After a user-defined threat intelligence type is added, the type ID cannot be modified.
- In the lower right corner of the page, click OK.
After the threat intelligence type is added, you can view the new type in the table on the Threat Intelligence page.
Associating a Threat Intelligence Type with a Layout
By default, built-in threat intelligence types are associated with existing layouts. You cannot customize associated layouts.
- Log in to the management console.
- Click
 in the upper part of the page and choose Security > SecMaster.
in the upper part of the page and choose Security > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace.
Figure 5 Workspace management page

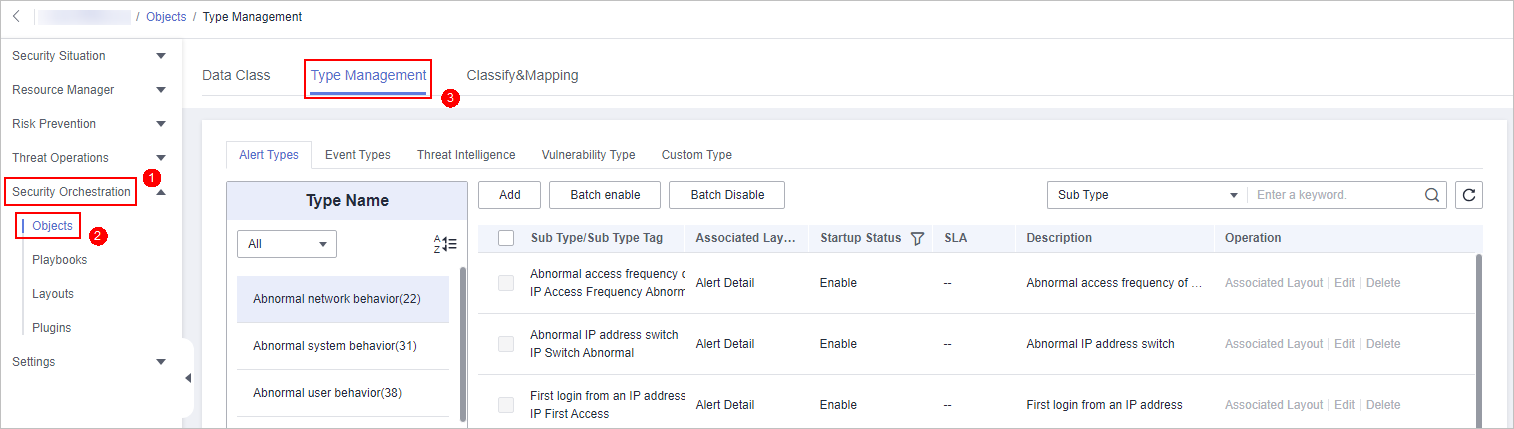
- In the navigation pane on the left, choose . On the displayed page, click the Type Management tab.
Figure 6 Type Management page
- On the Type Management page, click the Threat Intelligence tab.
- On the Threat Intelligence page, select the type to be associated with a layout and click Associated Layout in the Operation column of the target type. The Associate Layout dialog box is displayed.
- In the Associate Layout dialog box, select the target layout and click OK.
Editing a Threat Intelligence Type
- Currently, built-in threat intelligence types cannot be edited.
- After a custom threat intelligence type is added, the type tag cannot be edited.
- Log in to the management console.
- Click
 in the upper part of the page and choose Security > SecMaster.
in the upper part of the page and choose Security > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace.
Figure 7 Workspace management page

- In the navigation pane on the left, choose . On the displayed page, click the Type Management tab.
Figure 8 Type Management page
- On the Type Management page, click the Threat Intelligence tab.
- On the Threat Intelligence page, select the type to be edited and click Edit in the Operation column of the target type. The editing page is displayed on the right.
- On the displayed page, edit the parameter information of the corresponding type.
Table 3 Threat intelligence type parameters Parameter
Description
Type Name
Name of the user-defined threat intelligence type.
Type Tag
Threat intelligence type ID, which cannot be modified.
Startup Status
Indicates the enabling status of threat intelligence:
Expired Time
Set the expiration time of threat intelligence.
- Never expire: The current intelligence type never expires.
- Interval: Set the interval for intelligence type expiration.
Description
Description of a custom threat intelligence type
- In the lower right corner of the page, click Confirm.
Managing a Threat Intelligence Type
- Log in to the management console.
- Click
 in the upper part of the page and choose Security > SecMaster.
in the upper part of the page and choose Security > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace.
Figure 9 Workspace management page

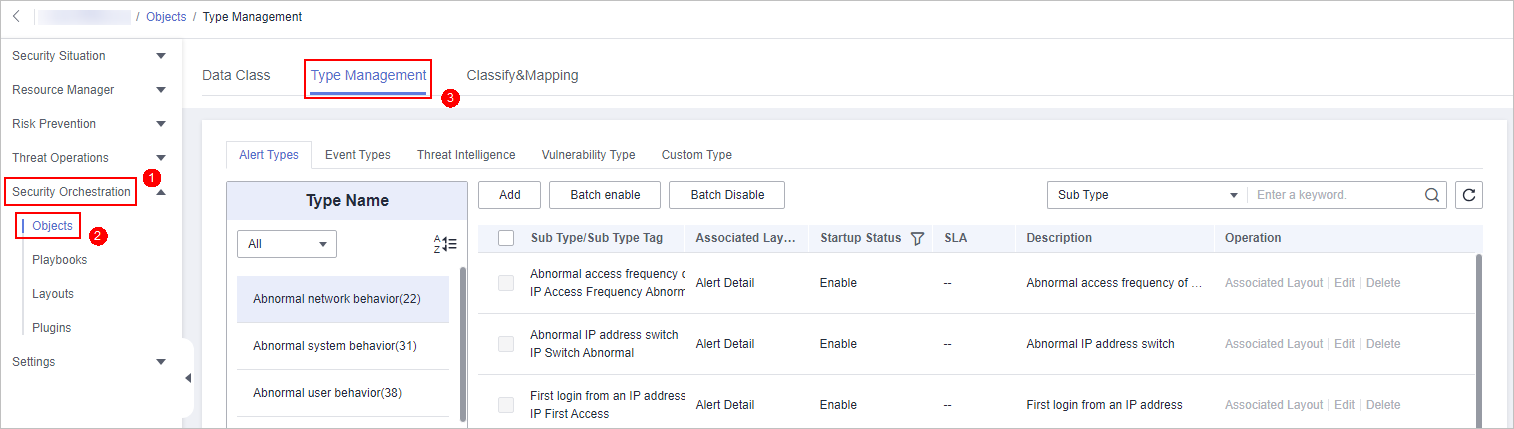
- In the navigation pane on the left, choose . On the displayed page, click the Type Management tab.
Figure 10 Type Management page
- On the Type Management page, click the Threat Intelligence tab.
- On the threat intelligence type tab, manage threat intelligence types.
- Built-in threat intelligence types are enabled by default. You do not need to manually enable them.
- Currently, built-in threat intelligence types cannot be disabled or deleted.
Table 4 Managing a threat intelligence type Operation
Description
Enable
- On the Threat Intelligence page, select the types to be enabled and click Batch enable in the upper left corner of the type list.
Alternatively, locate the row containing the threat intelligence to be enabled, click Disable in the Status column.
- In the dialog box displayed, click OK.
If the system displays a message indicating that the operation is successful and the status of the target type changes to Enable, the target type is enabled successfully.
Disable
- On the Threat Intelligence page, select the types to be disabled and click Batch Disable in the upper left corner of the type list.
Alternatively, locate the row containing the threat intelligence to be disabled, click Enable in the Status column.
- In the dialog box displayed, click OK.
If the system displays a message indicating that the operation is successful and the Status of the target type changes to Disable, the target type is disabled successfully.
Delete
- On the threat intelligence type management tab, select the type to be deleted and click Delete in the Operation column.
- In the displayed dialog box, enter DELETE and click OK.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





