Viewing Inbound Traffic
The inbound traffic page displays the traffic from the Internet to the cloud EIPs protected by the current firewall instance. The data is collected from sessions. The statistics of a session is reported only after it is terminated.
Prerequisites
EIP protection is enabled and there is already traffic passing through the EIP. For details, see Enabling Internet Border Traffic Protection.
Viewing Inbound Traffic
- Log in to the CFW console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - (Optional) Switch to another firewall instance. Select a firewall from the drop-down list in the upper left corner of the page.
- In the navigation pane, choose .
- Check the traffic passing through the firewall within a time range, from 5 minutes to 7 days.
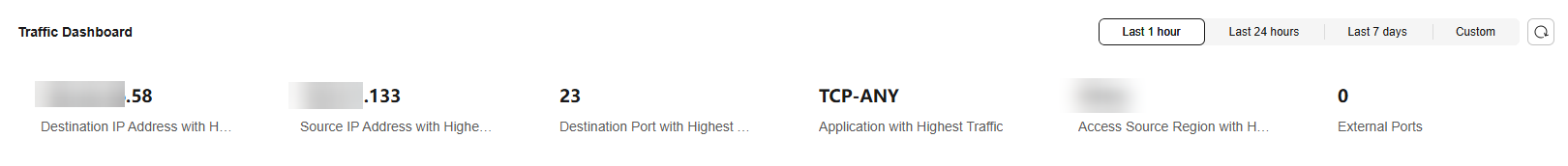
- Traffic Dashboard: Information about the highest traffic from the Internet to internal servers. Figure 1 Inbound traffic - traffic dashboard
- Inbound Traffic: Inbound request traffic and response traffic. The traffic statistics of up to 30 EIPs can be queried at a time.
The data displayed is the average bits per second (bps) of the sessions ended at the specified time in traffic logs.
Figure 2 Inbound traffic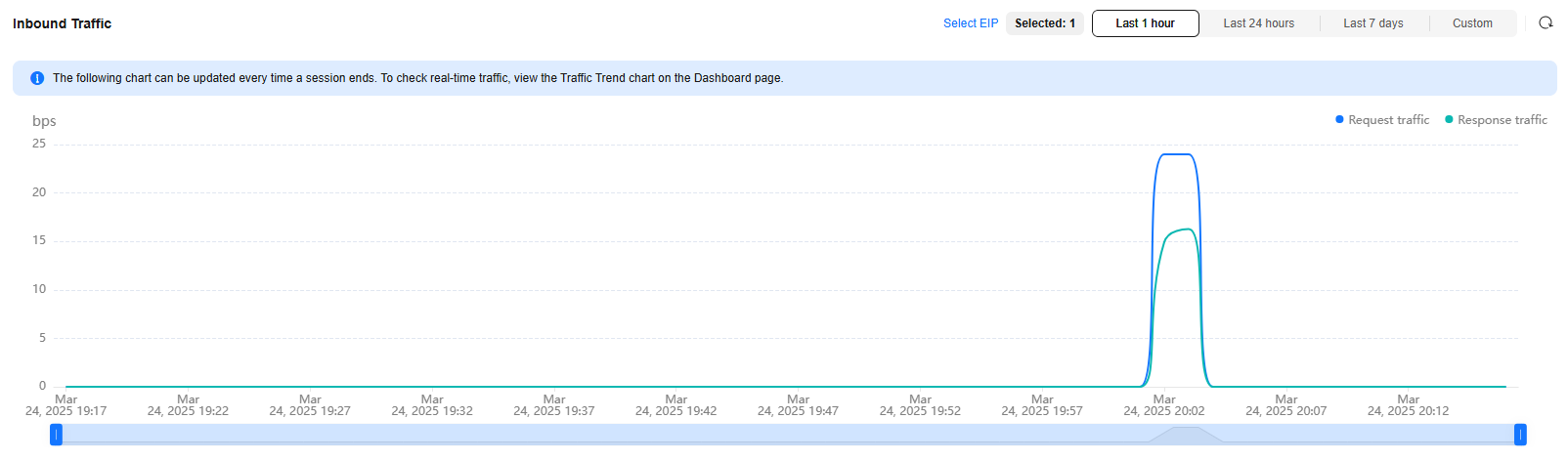
Table 1 Value description Time Range
Value
Last 1 hour
Average value within every minute
Last 24 hours
Average value within every 5 minutes
Last 7 days
Average value within every hour
Custom
- 5 minutes to 6 hours: average value within every minute
- 6 hours (included) to 3 days: average value within every 5 minutes
- 3 (included) to 7 days (included): average value within every 30 minutes
- Visualizations: View the top 5 items ranked by specific parameters of inbound traffic within a specified period. For more information, see Table 2. You can click a data record to view the traffic details. A maximum of 50 data records can be viewed. Figure 3 Inbound traffic - visualized statistics
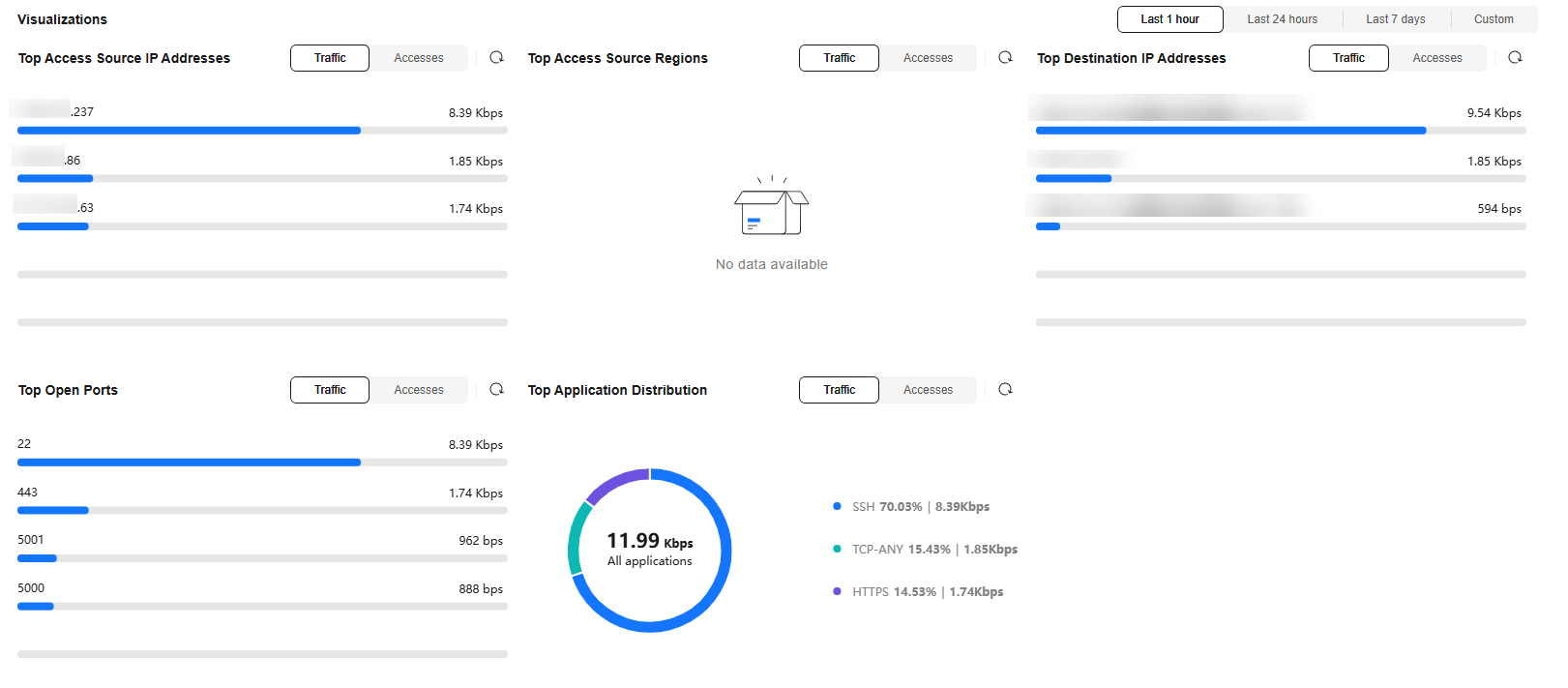
Table 2 Inbound traffic parameters Parameter
Description
Top Access Source IP Addresses
Source IP addresses of inbound traffic.
Top Access Source Regions
Geographical locations of the source IP addresses of inbound traffic.
Top Destination IP Addresses
Destination IP addresses of inbound traffic.
Top Open Ports
Destination ports of inbound traffic.
Top Application Distribution
Application information about inbound traffic.
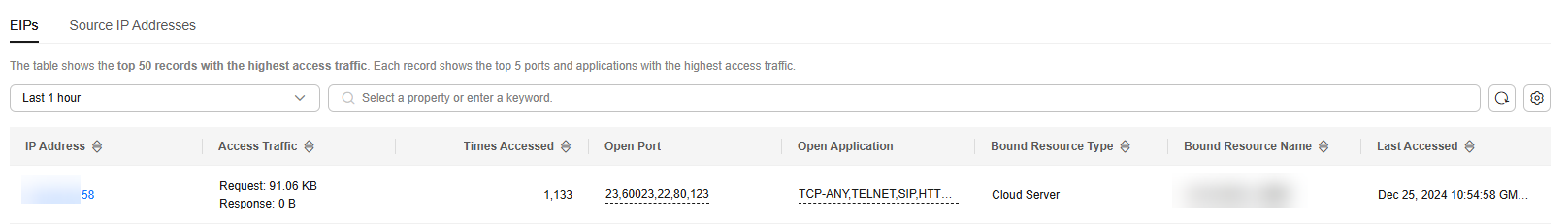
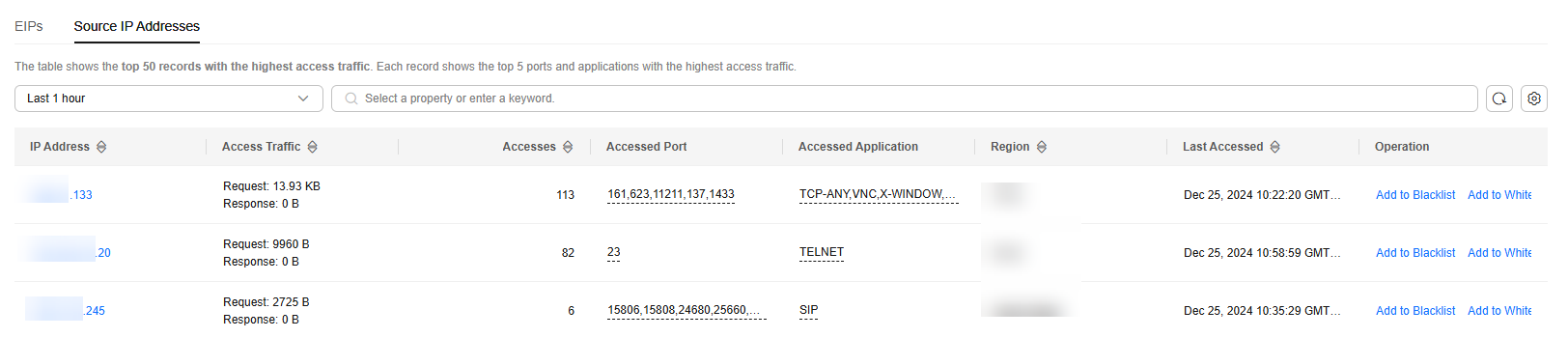
- IP analysis: Top 50 traffic records in a specified period.
- EIPs: Traffic information about destination IP addresses. Figure 4 EIP analysis
- Source IP Addresses: Traffic information about source IP addresses. Figure 5 Source IP address analysis
- EIPs: Traffic information about destination IP addresses.
- Traffic Dashboard: Information about the highest traffic from the Internet to internal servers.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.






