Creating a User with ClickHouse Permissions
Scenarios
This section describes how to create and configure a ClickHouse role and bind it with a user on Manager as an MRS cluster administrator. You can grant the administrator permission and permissions to read and write tables and databases to the ClickHouse role.
Prerequisites
- The ClickHouse and Zookeeper services are running properly.
- The ON CLUSTER statement has been used to create a database or table in the cluster to ensure that the metadata of the database and table on each ClickHouse node is the same.
After the permission is granted, it takes about 1 minute for the permission to take effect.
Adding the ClickHouse Role
- Log in to FusionInsight Manager.
- Choose System > Permission > Role. On the Role page, click Create Role.
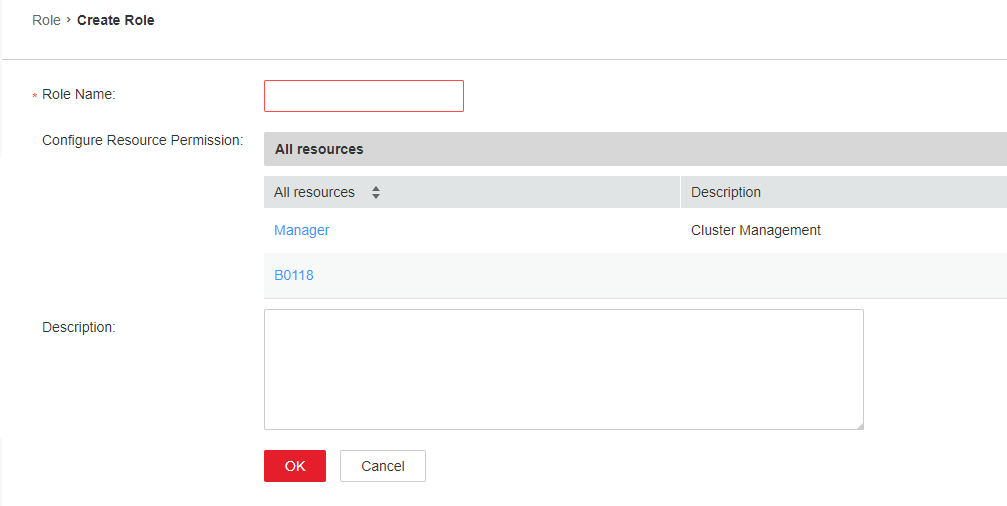
- On the Create Role page, specify Role Name. In the Configure Resource Permission area, click the cluster name. On the service list page that is displayed, click the ClickHouse service.
Determine whether to create a role with the ClickHouse administrator permissions based on service requirements.
- The ClickHouse administrator has all the database operation permissions except the permissions to create, delete, and modify users and roles.
- Only the built-in user clickhouse of ClickHouse has the permission to manage users and roles.
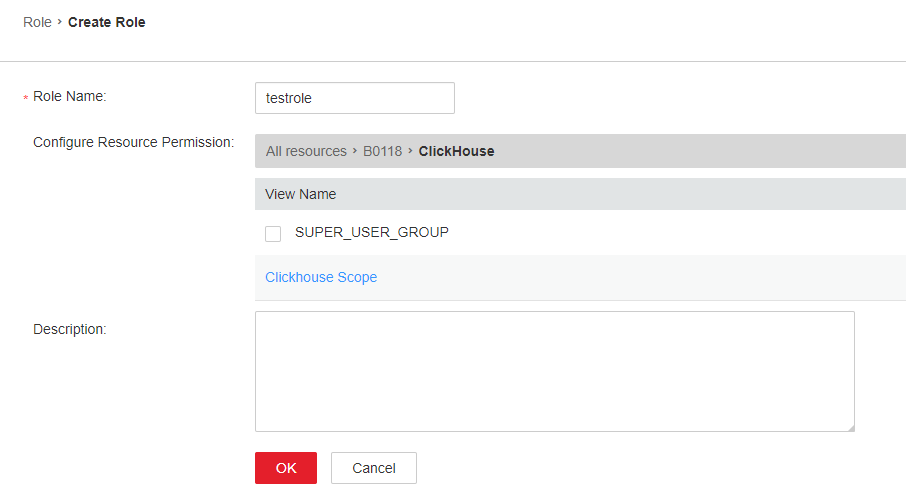
- Select SUPER_USER_GROUP and click OK.
- Click Clickhouse Scope. The ClickHouse database resource list is displayed. If you select create, the role has the create permission on the database.
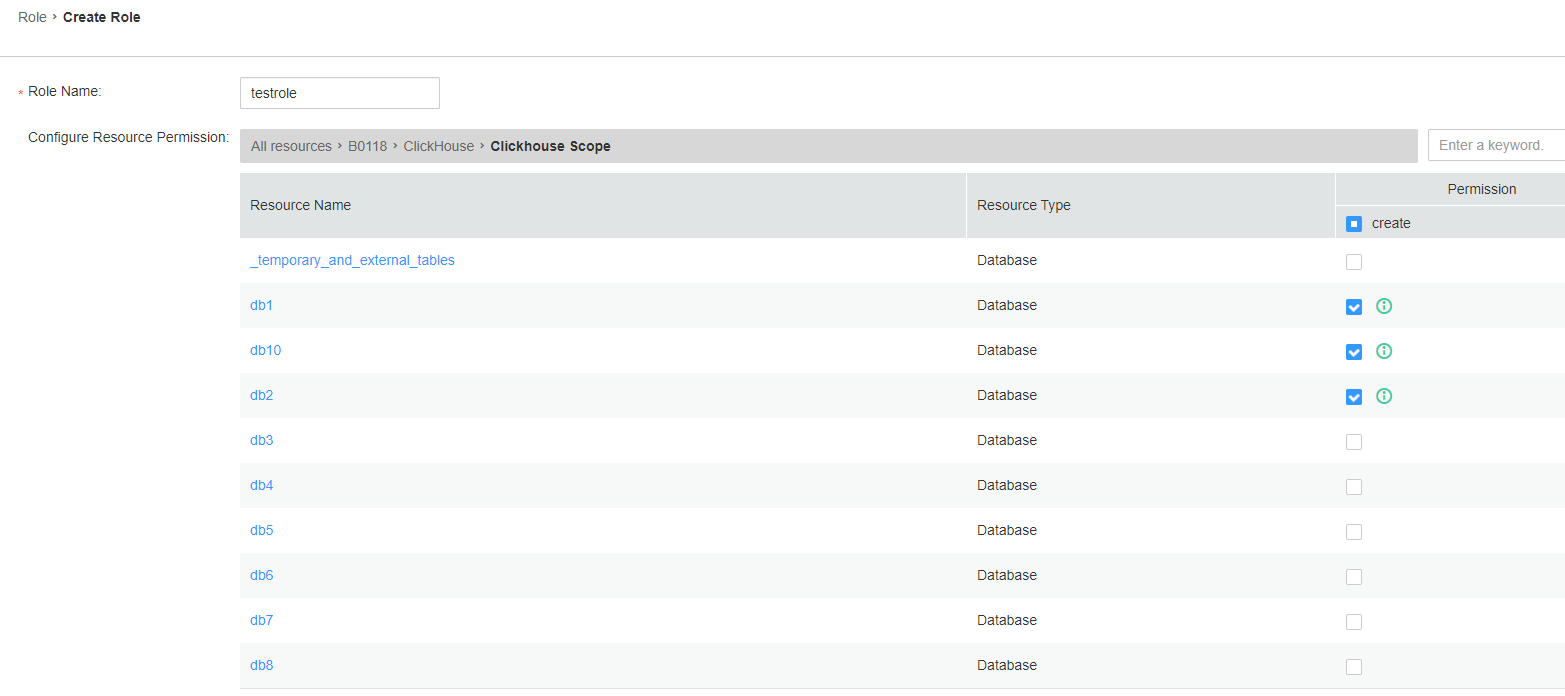
Determine whether to grant the permission based on the service requirements.
- If yes, click OK.
- If no, go to 6.
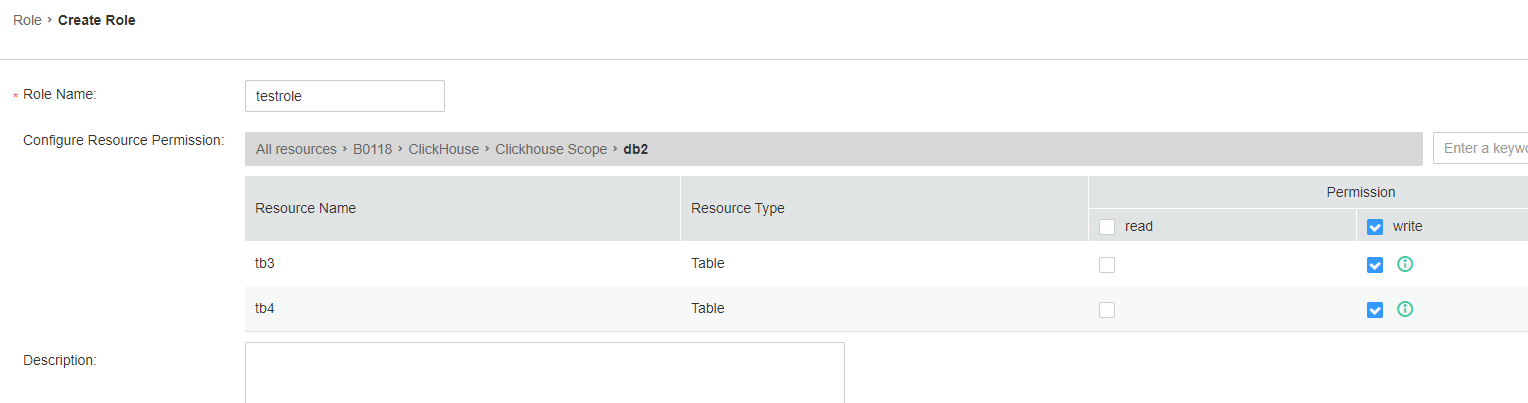
- Click the resource name and select the Database resource name to be operated. On the displayed page, select READ (SELECT permission) or WRITE (INSERT permission) based on service requirements, and click OK.
Adding a User and Binding the ClickHouse Role to the User
- Log in to FusionInsight Manager.
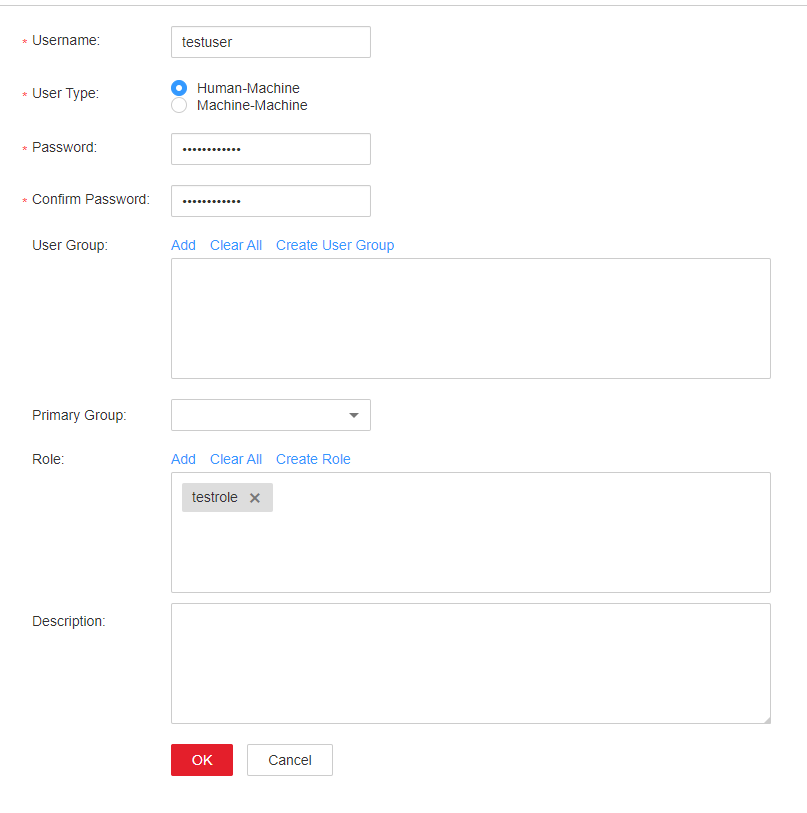
- Choose System > Permission > User and click Create.
- Select Human-Machine for User Type and set Password and Confirm Password to the password of the user.
- Username: The username cannot contain hyphens (-). Otherwise, the authentication will fail.
- Password: The password cannot contain special characters $, ., and #. Otherwise, the authentication will fail.
- In the Role area, click Add. In the displayed dialog box, select a role with the ClickHouse permission and click OK to add the role. Then, click OK.
- Log in to the node where the ClickHouse client is installed and use the new username and password to connect to the ClickHouse service.
- Run the following command to go to the client installation directory:
- Run the following command to configure environment variables:
- If Kerberos authentication is disabled for the current cluster, run the following command to connect to the ClickHouse server:
clickhouse client --host IP address of the ClickHouse instance --multiline --port 9000 --secure
- If Kerberos authentication is enabled for the current cluster, run the following commands to connect to the ClickHouse server. To run the commands, the user must have the permission to create ClickHouse tables. For details about how to obtain the permission, see Adding the ClickHouse Role.
kinit User added in step 2
For a new user, change the password upon first login.
clickhouse client --host IP address of the ClickHouse instance--user User added in step 2 --password --port 9440 --secure
MRS 3.2.0-LTS and earlier: For a cluster in normal mode, the default user is used. Alternatively, you can create an administrator using the open source capability provided by the ClickHouse community. You cannot use the users created on FusionInsight Manager.
MRS 3.3.0-LTS and later: For a cluster in normal mode, you can use the users created on FusionInsight Manager.
Granting Permissions Using the Client in Abnormal Scenarios
By default, the table metadata on each node of the ClickHouse cluster is the same. Therefore, the table information on a random ClickHouse node is collected on the permission management page of Manager. If the ON CLUSTER statement is not used when databases or tables are created on some nodes, the resource may fail to be displayed during permission management, and permissions may not be granted to the resource. To grant permissions on the local table on a single ClickHouse node, perform the following steps on the background client.
The following operations are performed based on the obtained roles, database or table names, and IP addresses of the node where the corresponding ClickHouseServer instance is located.
- To obtain the IP address of the ClickHouseServer instance, log in to FusionInsight Manager, choose Cluster > Services > ClickHouse, and click the Instances tab.
- The default system domain name is hadoop.com. Log in to FusionInsight Manager and choose System > Permission > Domain and Mutual Trust. The value of Local Domain is the system domain name. Change the letters to lowercase letters when running a command.
- Log in to the node where the ClickHouseServer instance is located as user root.
- Run the following command to obtain the path of the clickhouse.keytab file:
ls ${BIGDATA_HOME}/FusionInsight_ClickHouse_*/install/FusionInsight-ClickHouse-*/clickhouse/keytab/clickhouse.keytab
- Log in to the node where the client is installed as the client installation user.
- Run the following command to go to the client installation directory:
cd /opt/client
- Run the following command to configure environment variables:
source bigdata_env
- Run the following command to connect to the ClickHouseServer instance:
If Kerberos authentication is enabled for the current cluster, run the following command:
clickhouse client --host IP address of the node where the ClickHouseServer instance is located --user clickhouse/hadoop.<System domain name> --password clickhouse.keytab path obtained in 2 --port ClickHouse port number --secure
If Kerberos authentication is disabled for the current cluster, run the following command:
clickhouse client --host IP address of the node where the ClickHouseServer instance is located --user clickhouse --port ClickHouse port number
- Run the following statement to grant permissions to a database:
In the syntax for granting permissions, DATABASE indicates the name of the target database, and role indicates the target role.
GRANT [ON CLUSTER cluster_name] privilege ON {DATABASE|TABLE} TO {user | role}
For example, grant user testuser the CREATE permission on database t2:
GRANT CREATE ON t2 to testuser;
- Run the following commands to grant permissions on the table or view. In the following command, TABLE indicates the name of the table or view to be operated, and user indicates the role to be operated.
Run the following command to grant the query permission on tables in a database:
GRANT SELECT ON TABLE TO user;
Run the following command to grant the write permission on tables in a database:
GRANT INSERT ON TABLE TO user;
For details about ClickHouse GRANT operations and permission description, visit https://clickhouse.tech/docs/en/sql-reference/statements/grant/.
- Run the following command to exit the client:
quit;
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.






