Why Is No Data Displayed on the Access Control Logs Page?
Symptom
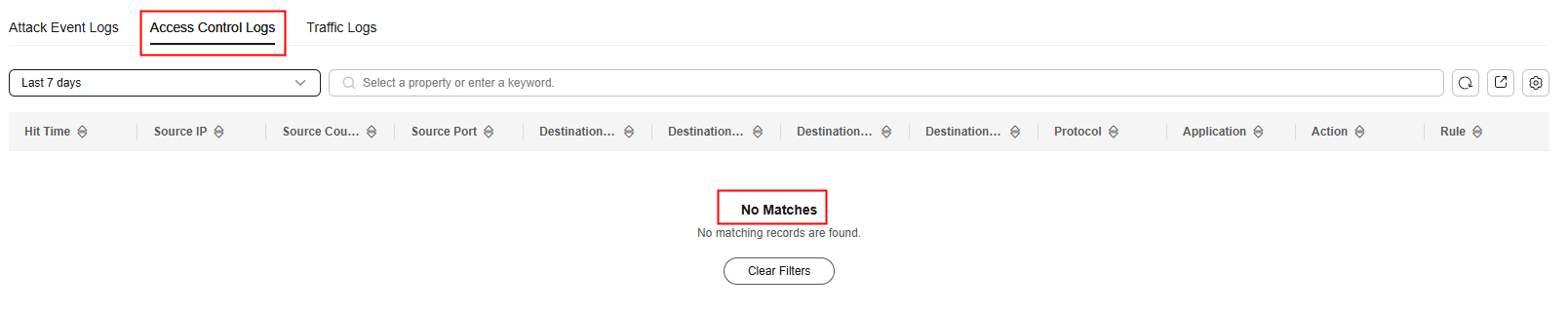
There is traffic, but no data is displayed on the access control log page, as shown in Figure 1.
Possible Causes
Access control logs display the traffic that hits an ACL protection policy (a protection rule or blacklist/whitelist). If the firewall is not enabled for cloud resources or no ACL policies are configured, no access control logs will be generated.
Solution
- Enable the firewall to protect cloud resources.
- For details about how to enable EIP protection, see Enabling EIP Protection.
- For details about how to enable VPC border protection, see Enabling VPC Border Traffic Protection.
- Add an ACL policy.
- For details about how to add a protection rule, see Adding a Protection Rule.
- For details about how to add a blacklist or whitelist, see Adding a Blacklist or Whitelist Item.
References
- For details about the records of all traffic passing through CFW, see Traffic Logs.
- For details about attack event records, see Attack Event Logs.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.