Why Does a Protection Rule Not Take Effect?
All Traffic Is Allowed Even If a Rule Is Configured to Allow Only Several EIPs
After EIP protection is enabled on CFW, the access control policy allows all traffic by default. If you want to allow traffic of only several EIPs, you need to configure a protection rule to block all traffic and set the lowest priority.
- Log in to the CFW console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - (Optional) Switch to another firewall instance. Select a firewall from the drop-down list in the upper left corner of the page.
- In the navigation pane, choose Access Control, and choose Internet Border Protection Rules or VPC Border Protection Rules.
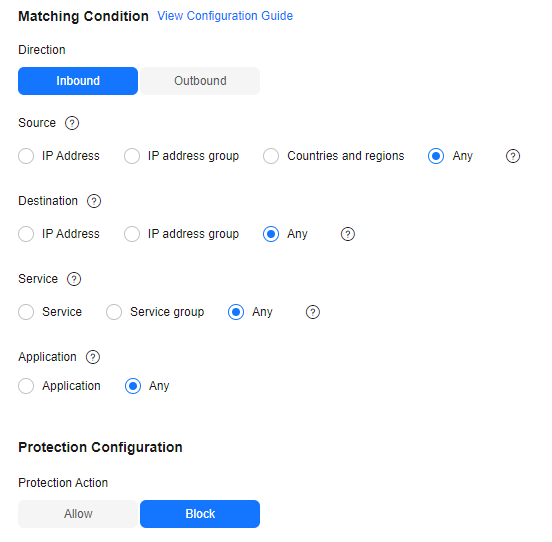
- Configure a global blocking rule. Click Add Rule. Use the parameter settings shown in Figure 1 and configure other parameters as needed.
Table 1 Allowing a specified IP address Parameter
Example Value
Description
Direction
Inbound
Direction of the protected traffic.
Source
IP Address
192.168.0.0
Origin of network traffic.
Destination
Any
Receiver of network traffic.
Service
Any
Protocol, source port, and destination port of network traffic.
Action
Allow
Action taken when traffic passes through the firewall.
You are advised to enable the rules after adding all required ones.
- Configure an allow rule. For details about how to add a protection rule, see Adding a Protection Rule.
- Set the priority of the global blocking rule in the 5 to the lowest. For details, see Setting the Priority.
- Enable all rules. You are advised to enable the allow rules prior to the blocking rules.
Blocked IP Addresses Are Still Allowed Through Even If a Global Blocking Rule Is Configured
The EIP protection rules configured on CFW are applied based on the EIP management list. If you have enabled global blocking (0.0.0.0/0) but the traffic of EIPs not in an allow rule is allowed through, check whether the EIPs are protected. For more information, see Enabling EIP Protection.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.